Now-patched API vulnerability allowed attacker to entry delicate assets
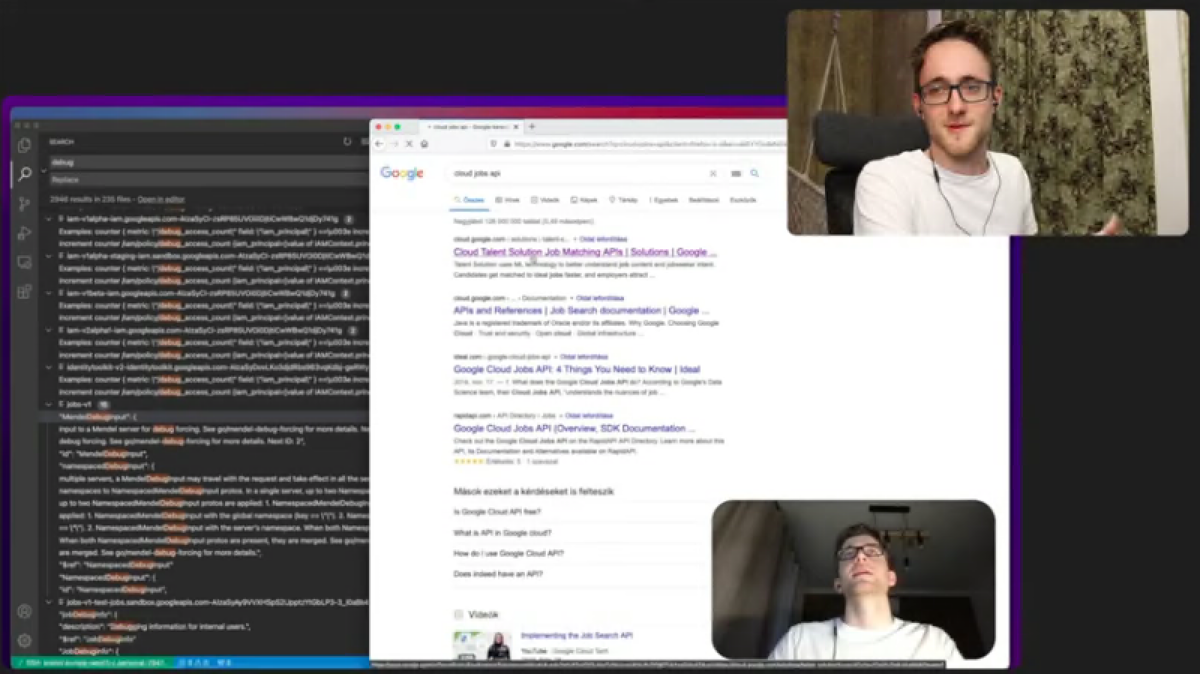
A URL parsing bug left an internal Google Cloud challenge open to server-side request forgery (SSRF) assaults, safety researcher David Schütz has discovered.
Now fastened, the bug, which Schütz has documented in a complete video and blog post, may have allowed an attacker to entry delicate assets and probably run malicious code.
Leaking entry token
Schütz discovered the bug whereas doing analysis on Discovery Documents, knowledge constructions that present specs for Google API companies. While exploring the Discovery Documents, Schütz came across an fascinating service referred to as Jobs API, whose identify recommended it was an internal service.
The Jobs API led him to an software on the Google App Engine that served as a proxy to make the API out there by means of Google’s public product advertising pages. The proxy served as an middleman that offered entry to the API, which meant it had an entry token that would probably function a window for SSRF assaults.
The proxy prevented entry to internal Google assets by working request URLs by means of a whitelist. But with slightly fiddling, Schütz was capable of trick the URL parser and bypass the whitelist to ship requests to arbitrary servers. This enabled him to ship requests from the proxy app to a VPS server he ran on Google Cloud.
The request uncovered the proxy app’s entry token, which he may then use to ship requests to different internal Google Cloud tasks.
“In this explicit bug, the core problem was a URL parsing bug, which result in the SSRF,” Schütz advised The Daily Swig.
Last 12 months, Schütz had discovered a similar bug in a Google JavaScript library that was used in many Google companies.
Accessing assets, working arbitrary code
Through the entry token, Schütz was capable of acquire an inventory of accessible internal tasks, cloud storage buckets, digital machines, and the administration interface of the proxy software.
Through the latter, he was capable of entry logs that had delicate consumer info (although he didn’t obtain any of the logs) and situations of the app itself, which might be reverse-engineered to acquire its supply code.
Read more of the latest cloud security news
The administrative interface is particularly harmful as a result of it has full management of the App Engine occasion, permitting an attacker to disrupt the service, acquire consumer info, or add malicious code.
To present the affect of the bug, Schütz created and uploaded a Python software on the proxy service that returned a base64 message. To keep away from disrupting the principle service, he uploaded the appliance as a non-default model of the proxy service.
“This problem appears like an industry-wide drawback since completely different functions are parsing URLs primarily based on completely different specs,” Schütz stated.
“After disclosing the preliminary problem in the Google JS library, I’ve already seen this getting fastened in merchandise from completely different firms as effectively. Even although, this problem nonetheless retains popping up even at Google. This SSRF is a good instance of it.”
Schütz was rewarded a $4,133 bounty by the Google Vulnerability Rewards Program for the invention.
After the bug was fastened, he had one other shot on the proxy and noticed that though the unique exploit now not labored, the URL parser may nonetheless be bypassed by means of one other scheme. Reporting this new bug obtained him one other $3,133 in double bounty.
He later obtained an additional $3,133 by discovering and reporting that previous variations of the proxy software had been nonetheless up and working.
https://portswigger.internet/daily-swig/researcher-finds-ssrf-bug-in-internal-google-cloud-project-nabs-10-000-bounty