- Friday
- May 17th, 2024
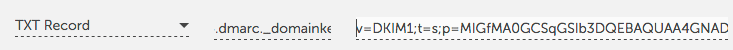
Domain-based Message Authentication, Reporting and Conformance (DMARC) is an more and more necessary method for serving to make sure the integrity of e-mail coming from a given area. Unfortunately, this necessary email security normal will not be turned on by...

Axis App Access Cloud Recognized for Simple, Secure Approach to Enterprise Remote Access SAN MATEO, CA, April 15, 2021 – Axis Security, the chief in Zero Trust Network Access (ZTNA), introduced as we speak that it has been named certainly...
Axis App Access Cloud Recognized for Simple, Secure Approach to Enterprise Remote AccessSAN MATEO, Calif., April 15, 2021 /PRNewswire/ -- Axis Security, the chief in Zero Trust Network Access (ZTNA), introduced at present that it has been named one in every...

The safety features for verifying the supply of an electronic mail header fail to work collectively correctly in lots of implementations, in accordance to a crew of researchers.Three requirements for electronic mail safety which can be supposed to confirm the...

More than ten totally different superior persistent risk (APT) teams have been discovered to be exploiting the latest vulnerabilities in Microsoft's Exchange software program to compromise email servers, based on cybersecurity firm ESET. ESET mentioned its analysis unit has...
If your on-line life revolves round Gmail, Chrome, and different Google software program and companies, your Google account is one among your most valuable on-line assets. That's very true when you use the Gmail handle related to that account as...
WASHINGTON — U.S. Rep. John Katko is giving mixed opinions to a pair of nominees set to guide two of the nation’s most distinguished security businesses because the congressman once more visited the southern border.Katko, in his fourth time period,...

Jake Sullivan, a longtime Democratic aide whom President-elect Joe Biden’s transition crew tapped as the subsequent national security adviser, was a central determine in the email scandal that rocked the ultimate days of Hillary Clinton’s presidential marketing campaign in 2016.Clinton and her...

Email Account Takeover (ATO) assaults happen when a risk actor features unauthorized entry to an e-mail account belonging to another person. Cybercriminals acquire stolen person credentials by commerce or buy on the darkish internet. Typically, the credentials are obtained by...
 Loading posts...
Loading posts...  All posts loaded
All posts loaded
No more posts

