If your on-line life revolves round Gmail, Chrome, and different Google software program and companies, your Google account is one among your most valuable on-line assets. That’s very true when you use the Gmail handle related to that account as your major electronic mail handle.
An on-line prison who will get maintain of these credentials may cause chaos and do catastrophic injury to your on-line life, which is why it is necessary to defend your Google account from being compromised.
Also: Best VPNs • Best security keys
In this put up, I record seven steps you possibly can take to assist secure your Google account so it is secure from on-line assaults. If this sounds acquainted, it is a mirror of the suggestions I printed earlier for Microsoft accounts: “How to lock down your Microsoft account and keep it safe from outside attackers.” Although there are similarities between the 2 firms’ safety instruments, there are additionally some necessary variations.
As with all issues security-related, making your on-line belongings safer from outdoors assault includes trade-offs with comfort. To assist with that balancing act between comfort and safety, I’ve divided the steps into three teams, primarily based on how tightly you need to secure your Google account.
(And please notice that the steps described on this article are about private accounts related to free Gmail addresses. Google’s paid enterprise companies, together with Google Workspace, are managed by area directors. Although some person configuration steps are the identical, directors can set insurance policies that have an effect on safety settings. If your Gmail account is offered by your employer, verify with them about finest practices for securing that account.)
Baseline safety
This degree is ample for many bizarre PC customers, particularly those that do not use their Gmail handle as a major issue for signing in to different websites. If you are serving to a pal or relative who’s technically unsophisticated and intimidated by passwords, that is a good choice.
At a minimal, it is best to create a sturdy password on your Google account. That password must be one which’s not utilized by every other account.
In addition, it is best to activate 2-step verification (Google’s time period for multi-factor authentication) to defend your self from phishing and different types of password theft. When that function is enabled, you’ve gotten to provide a further proof of your identification whenever you check in for the primary time on a new machine or whenever you carry out a high-risk exercise, reminiscent of paying for a web-based buy. The extra verification usually consists of a code despatched as an SMS textual content message to a trusted machine or a immediate despatched to a smartphone.
Also: Better than the best password: How to use 2FA to improve your security
Better safety
Those baseline precautions are sufficient, however you possibly can tighten safety considerably with a couple further steps.
First, arrange your smartphone as an authentication issue, utilizing an app reminiscent of Google Authenticator. You may check in on a smartphone utilizing your Google account, which mechanically permits it to obtain prompts to be used as a sign-in and verification choice. Then take away the choice for utilizing SMS textual content messages to confirm your identification.
With that configuration, you possibly can nonetheless use your cell phone as an authentication issue, however a would-be attacker will not have the ability to intercept textual content messages or spoof your telephone quantity.
Also: Microsoft urges users to stop using phone-based multi-factor authentication
Maximum safety
For probably the most excessive safety, add at the least one bodily {hardware} key together with the Google Authenticator app and, optionally, take away private electronic mail addresses as a backup verification issue. That configuration locations vital roadblocks in the best way of even probably the most decided attacker.
This configuration requires an additional funding in {hardware} and it undoubtedly provides some friction to the sign-in course of, nevertheless it’s by far the simplest manner to secure your Google account.
Also: Best security keys in 2020: Hardware-based two-factor authentication
STEP 1: CREATE A NEW, STRONG PASSWORD
First issues first: You want a sturdy, distinctive password on your Google account. The finest manner to be certain that you’ve got nailed this requirement is to use your password supervisor’s instruments to generate a brand-new password.
(No password supervisor? Try a web-based choice just like the 1Password Strong Password Generator or the LastPass Password Generator Tool.)
Generating a new password ensures that your account credentials aren’t shared with every other account; it additionally ensures that an older password that you simply may need inadvertently reused is not a part of a password breach.
To change your password, go to the Google Account Security web page at https://myaccount.google.com/security. Sign in, if mandatory, then click on Password (underneath the Signing In To Google heading) and comply with the prompts to change your password.
Also: The best password managers for business: 1Password, Keeper, LastPass, and more
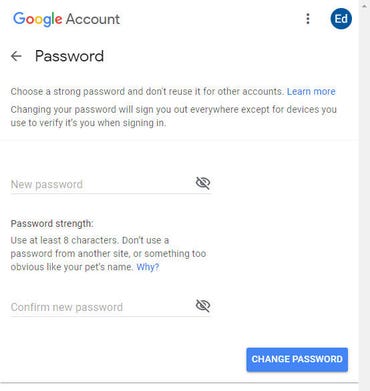
Make certain the password you enter right here is powerful and is not used for every other on-line account.
Follow the directions to save the brand new password utilizing your password supervisor. Feel free to write it down, when you choose a bodily backup. Just be sure that to retailer the paper in a secure location, reminiscent of a locked file drawer or a secure.
STEP 2: TURN ON TWO-STEP VERIFICATION
Don’t depart the Google Account Security web page simply but. Instead, scroll up to the Two-Step Verification part and ensure this feature is turned on. Use the default choice to obtain codes by way of textual content message on a cell phone you personally personal. (You can arrange different, extra superior types of verification as properly, however we’ll get to these later.)
The setup course of is a pretty simple wizard that confirms you’re able to obtain verification messages. After it is full, keep on that web page for the subsequent step.
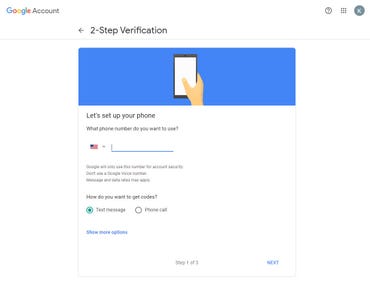
Basic 2-step verification makes use of SMS textual content messages, that are sufficient for low-risk accounts.
STEP 3: PRINT OUT RECOVERY CODES
Next step is to save a set of restoration codes. Having entry to one among these codes will permit you to check in to your account when you’ve forgotten the password or when you’ve misplaced your telephone. Without this backup, you threat being completely locked out.
On the Google Account Security web page, discover the Backup Codes choice and click on Set Up. That opens a pop-up dialog field just like the one proven right here, containing 10 codes that you need to use whenever you’re prompted for a second verification issue. Print out that web page and file it away in the identical locked file cupboard or secure the place you set your password.
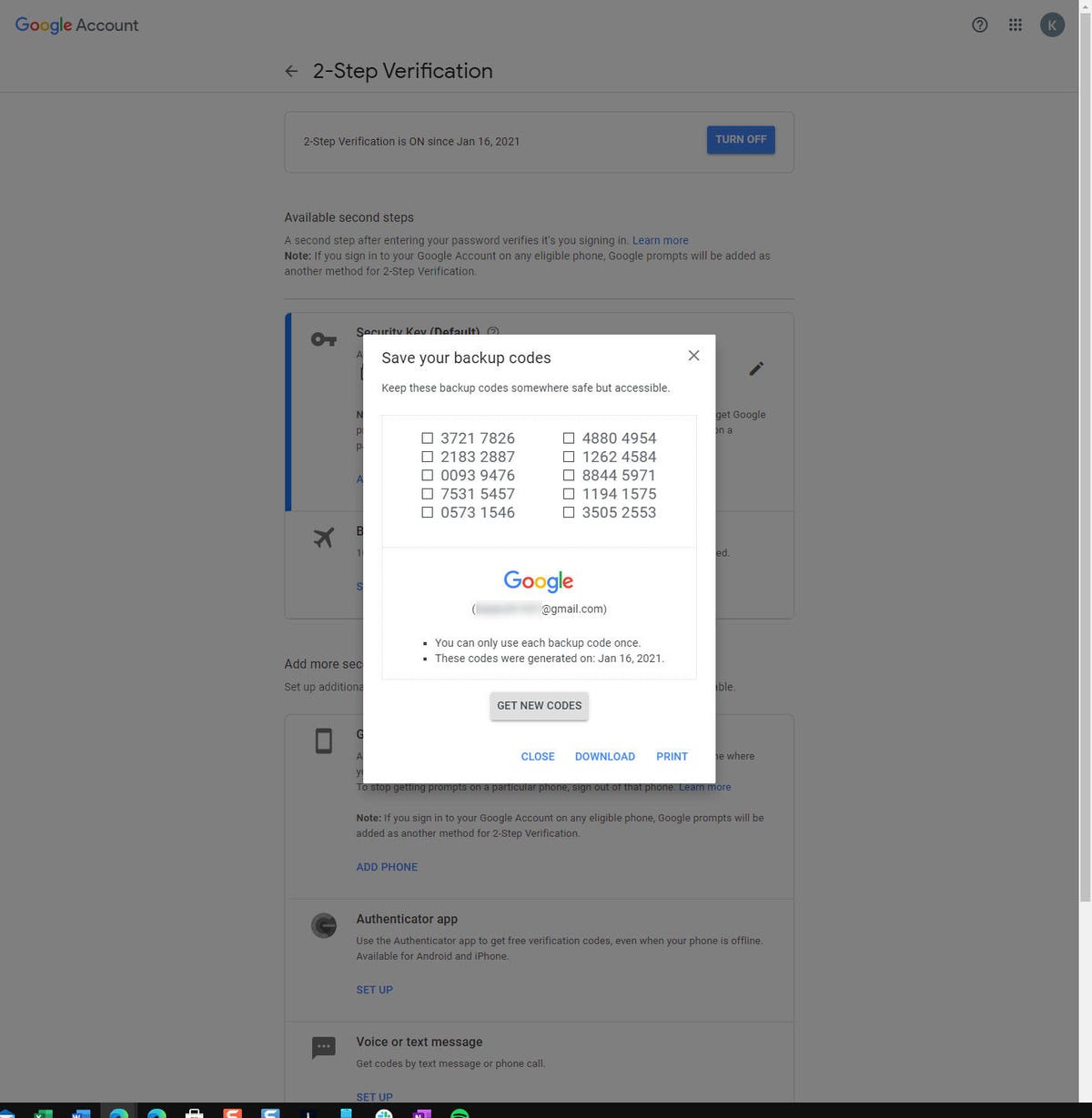
Print out a set of restoration codes and retailer them in a secure place the place you will discover them shortly when you lose entry to your account.
Note which you can return to this web page at any time to see your record of backup codes and print a contemporary copy. Codes can solely be used one time, and might be indicated as “Already used” when you reprint the record. Generating a new batch of codes renders the outdated batch invalid.
And now for some extra superior safety choices.
STEP 4: ADD A RECOVERY EMAIL ADDRESS
Registering a restoration electronic mail handle is a vital safety precaution. In the occasion that Google detects suspicious exercise in your account, you will obtain a notification at this handle.
Having a restoration electronic mail can be useful when you overlook your password. When two-step verification is enabled, resetting your password requires at the least two types of verification, reminiscent of a printed backup code and a code from an electronic mail message despatched to a registered electronic mail account. You’ll want to provide each of these types of identification otherwise you threat being completely locked out.
Go again to the Google Account Security web page and click on Recovery Email (underneath the Ways We Can Verify It’s You heading). Enter or change the restoration electronic mail handle. You’ll obtain a notification at that handle to verify that it is obtainable for restoration,
Which handle must you use right here? A free backup electronic mail handle, reminiscent of a Microsoft Outlook.com account, is suitable in case your safety wants are minimal. A greater choice is a enterprise electronic mail handle, which is underneath the management of an administrator and is harder to hack into than a private account.
Also: Best email hosting services in 2020: G Suite, Microsoft 365, and more options
STEP 5: SET UP YOUR SMARTPHONE AS AN AUTHENTICATOR
When you register your smartphone as a trusted machine, Google offers you two methods to use it for authentication functions.
If you utilize an Android machine that is signed in utilizing your Google account, you possibly can check in to any Google service by responding to prompts from Google. This choice would not require any further setup.
On an iPhone or iPad, you want to obtain the Google or Gmail app, check in together with your Google account, and activate push notifications. (Full directions are on this Google Support web page: “Sign in with Google prompts.”)
In addition, you need to use Google Authenticator or one other smartphone app that generates Time-based One-time Password Algorithm (TOTP) codes for multi-factor authentication. I extremely advocate utilizing one among these apps for any service that helps them. (For extra on these choices, see “Protect yourself: How to choose the right two-factor authenticator app.”)
To arrange Google Authenticator (or one other authenticator app) to be used with a Google account, go to the Google Account 2-Step Verification page. Under the Authenticator App heading, click on Set Up. (If you are changing your telephone, click on Change Phone). Install the app, if mandatory, after which comply with the prompts to add your account utilizing the bar code that the authenticator app shows.
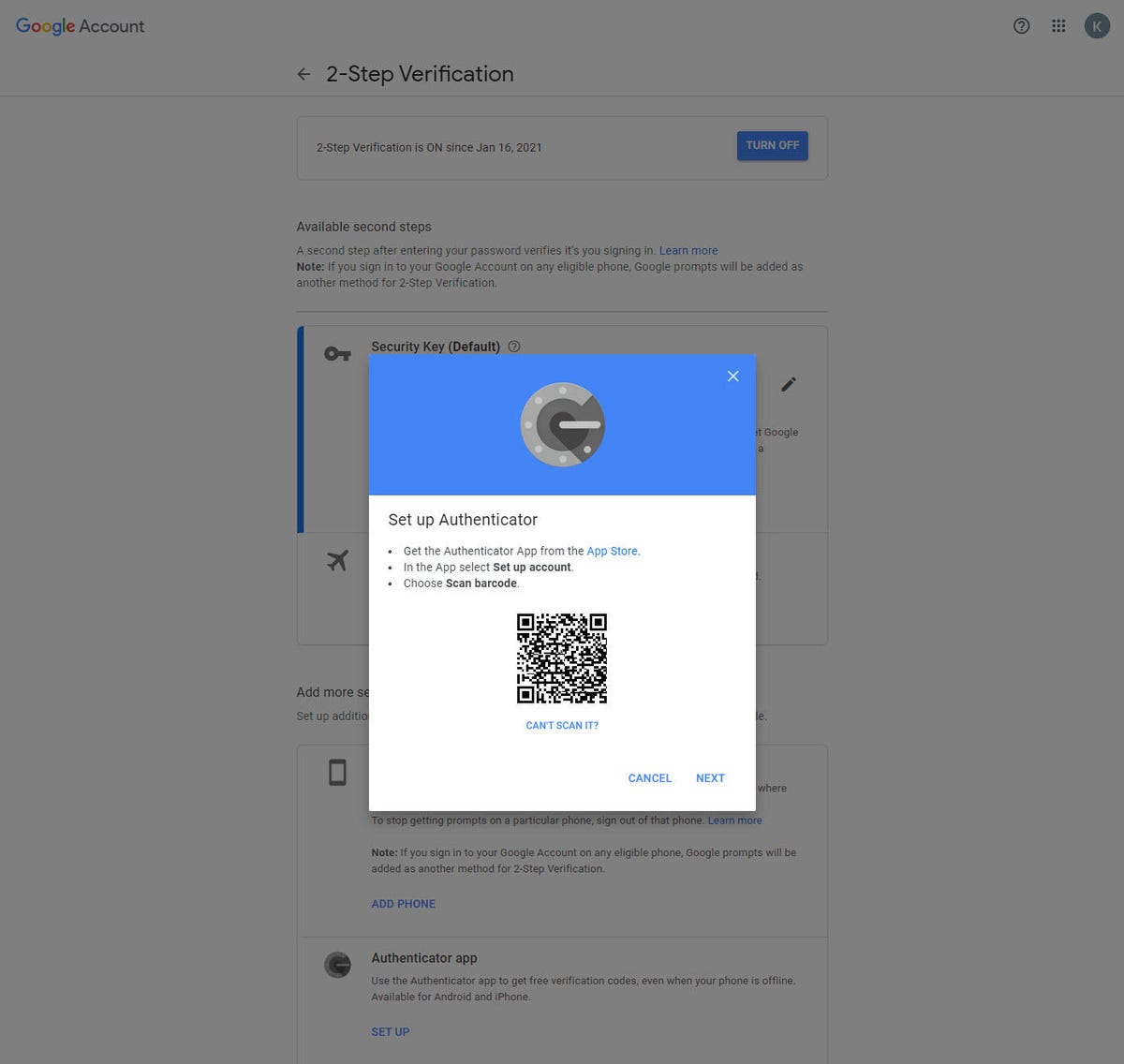
After putting in an authenticator app, use this barcode to arrange your Google account to generate TOTP codes.
STEP 6: REMOVE SMS TEXT MESSAGES AS A FORM OF VERIFICATION
By this level, it is best to have greater than sufficient secure methods to authenticate your self and confirm your identification. That means it is time to take away the weakest hyperlink within the chain: SMS textual content messages.
What makes SMS textual content messages so problematic from a safety viewpoint is the fact that an attacker can hijack your cell account. It happened to my ZDNet colleague Matthew Miller a few years ago, and I would not want that nightmare on anybody. (For particulars and a few extra safety recommendation, see “Protect your online identity now: Fight hackers with these 5 security safeguards.”)
Before you modify this setting, verify that you’ve got at the least two different types of verification (a secure electronic mail handle and the Google Authenticator app, for instance) and that you’ve got saved backup codes for the account. Then, from the Google Account 2-Step Verification page, go to the Voice Or Text Message part. There, you will discover entries for every of the telephone numbers registered as 2FA components on your account.
Click the pencil icon to the appropriate of a quantity to open its properties and click on Remove Phone to eradicate its entry. Repeat for different numbers you need to take away.
STEP 7: USE A HARDWARE SECURITY KEY FOR AUTHENTICATION
Using a {hardware} key, you possibly can check in to your Google account with a faucet.
This step is probably the most superior of all. It requires an funding in further {hardware}, however the requirement to insert a machine into a USB port or make a connection by way of Bluetooth or NFC provides the very best degree of safety.
For an outline of how such a {hardware} works, see “YubiKey hands-on: Hardware-based 2FA is more secure, but watch out for these gotchas.”
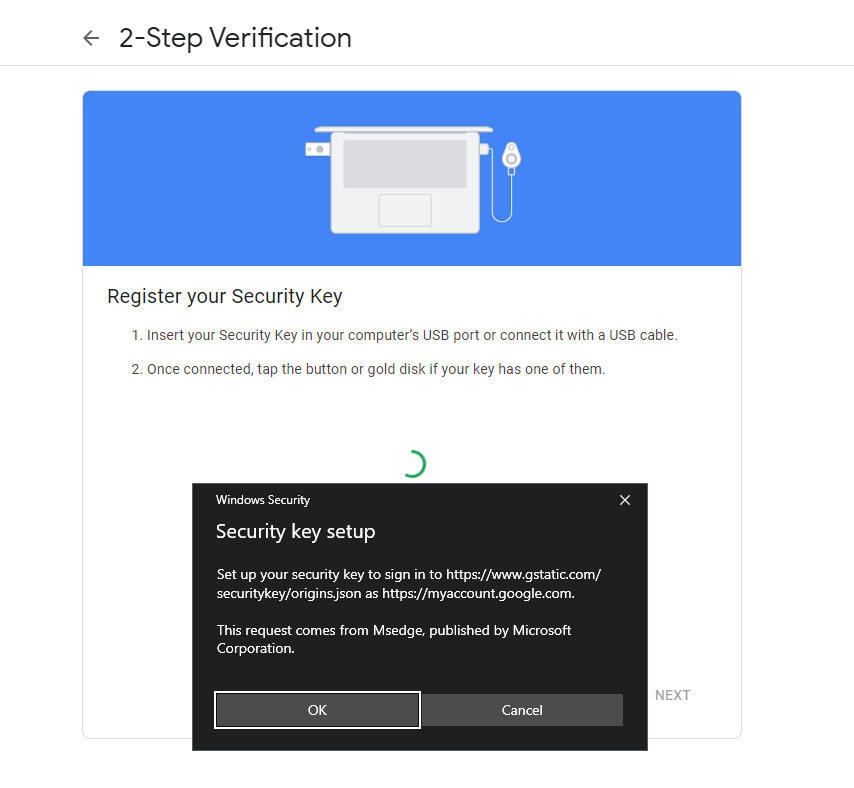
To configure a {hardware} key, go to the Google Account 2-Step Verification page, click on Add Security Key, after which comply with the prompts.
You’ll want to enter the PIN on your {hardware} key, then contact to activate it. When that setup is full, you’ve got received a highly effective manner to check in to any service powered by your Google account with out having to fuss with passwords.
As I discussed initially of this text, most individuals do not want this degree of superior safety. But in case your Google Drive account contains beneficial paperwork like tax returns and financial institution statements, you will need to lock it down as tightly as doable.





:max_bytes(150000):strip_icc()/HowtoSpecifyaPreferredSMTPServerforaMacOSXMailAccount2016-01-04-568a7f403df78ccc153b7b78.png)