- Monday
- April 29th, 2024
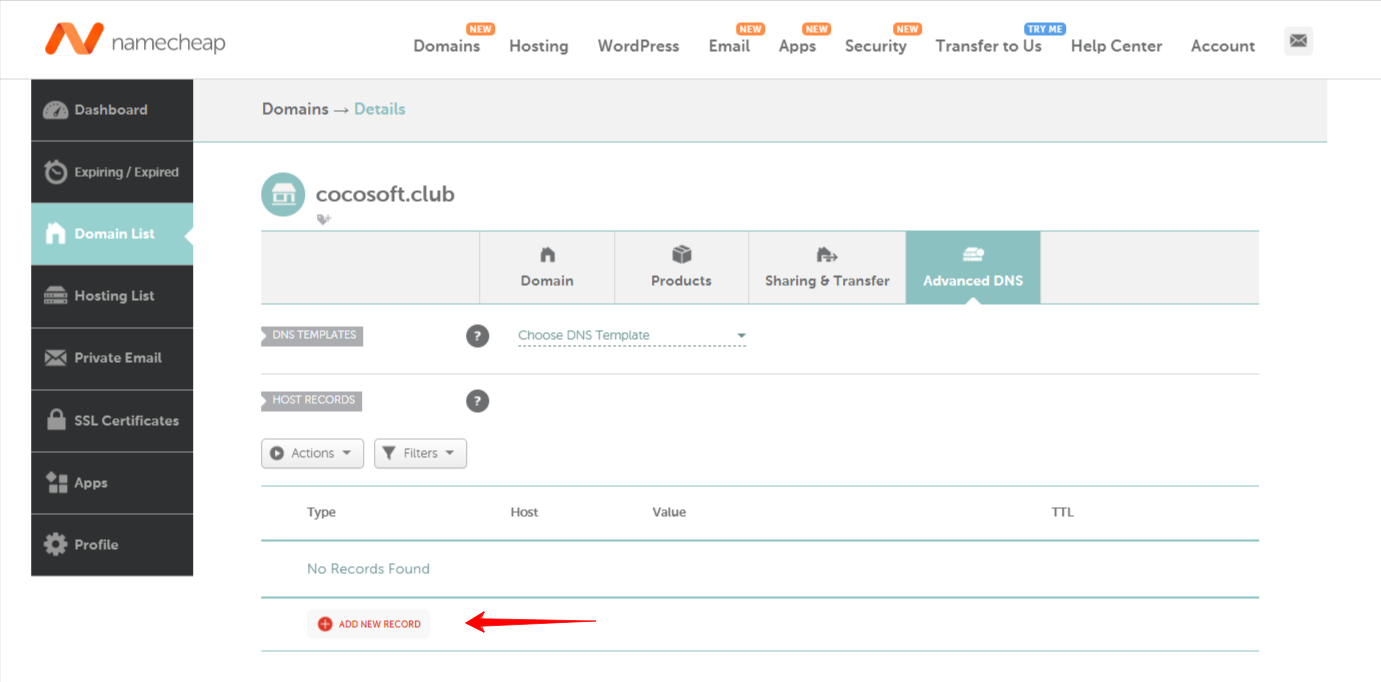
For any group, its electronic mail infrastructure should be essential. The first step to begin defending your area on your shoppers, distributors, companions, and everyone you ship emails to is time to look into electronic mail safety protocols. DMARC, the...

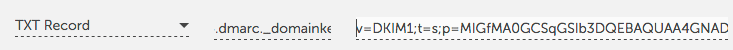
It’s not sensible to check DMARC vs. DKIM. They’re each authentication protocols used to validate emails, prevent spoofing, and safeguard your e-mail area. But that’s the place the similarities finish. While each protocols use public key cryptography, every makes use...

Email is extensively utilized by each group to talk with workers, potential prospects, and enterprise companions. Since its inception, e-mail communication has at all times had safety points, and sadly, easy message encryption between e-mail servers isn’t sufficient to preserve...

Email has at all times had safety issues, and sadly, merely encrypting message transfers between e mail servers will not be sufficient to cease spammers and different senders of undesirable e mail. Phishing scams, spamming and e mail spoofing depend...

The sheer quantity of spam and phishing scams on the market which have made e-mail servers begin to work fastidiously to maintain undesirable and sketchy emails out of prospects' inboxes - and typically, your messages can get caught up within...
DMARC is a vital a part of an total e mail safety technique – not simply one other cybersecurity acronym. (more…)

If you aren't utilizing international e mail safety requirements SPF, DKIM and DMARC, you have to be. They’ve been round for a few years and used and trusted by thousands and thousands of individuals. They can solely assist.Sender Policy Framework...
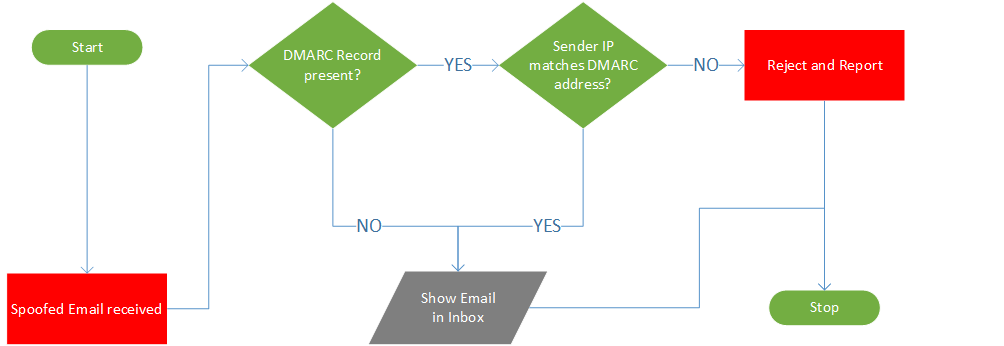
Email will proceed to be the dominant mode of digital communication for the foreseeable future. However, the e-mail framework was not designed with safety in thoughts. There nonetheless are safety flaws that unhealthy actors repeatedly exploit to their benefit.Recently, researchers...