- Friday
- April 19th, 2024
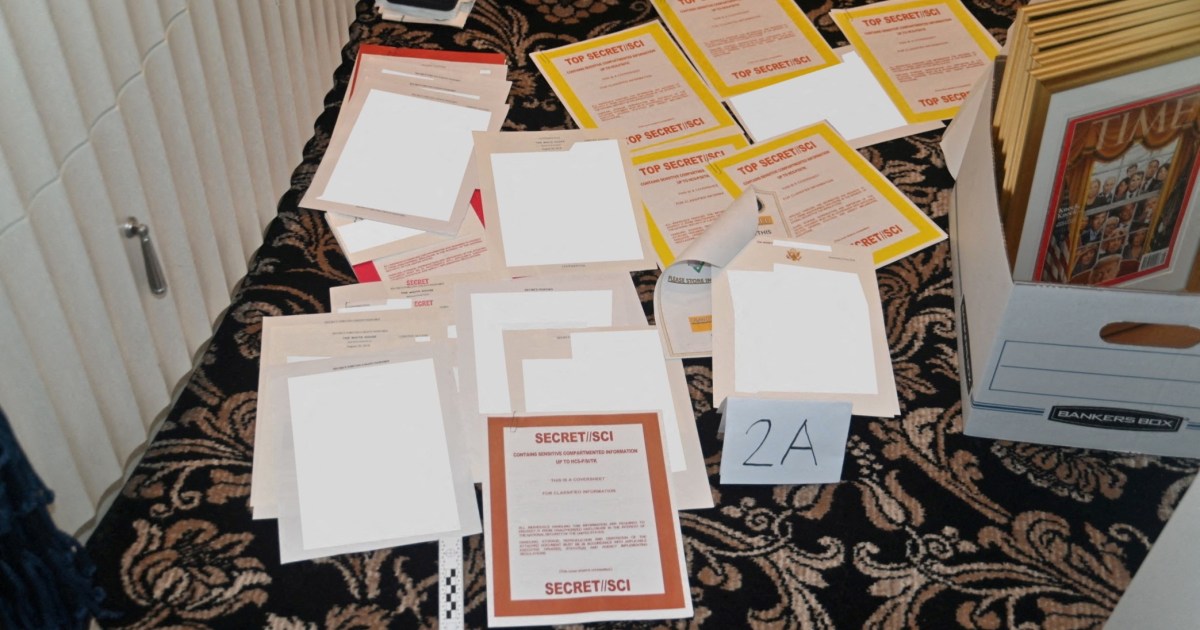
In gentle of the issues which were encountered first by President Trump and now by President Biden over the dealing with of labeled paperwork, many are questioning about how the doc classification system works. The federal authorities has a reasonably...

Apple @ Work is brought to you by Mosyle, the one Apple Unified Platform. Mosyle is the one resolution that absolutely integrates 5 completely different purposes on a single Apple-only platform, permitting Businesses to simply and routinely deploy, handle & shield...

Mimi Thian / Unsplash Nobody enjoys being advised they want to enhance. It will be troublesome to hear that, regardless of your finest efforts, your efficiency at work is just not the place it wants to be. In addition to...

Mails, mail servers, and extra. Emails are at the moment a very powerful type of communication amongst companies. So it goes with out saying that you have to means to verify your e-mail communications are as safe and environment friendly...

How Does Managed Hosting Work? Technology Managed Virtual Private Server internet hosting is the place your internet hosting supplier manages your web site and all related processes. The buyer takes no accountability for server administration. The internet hosting service takes...

President Donald J. Trump’s son-in-law and official White House adviser, Jared Kushner, used a private email server — arrange after the election — to conduct White House enterprise, according to a new report in Politico. Kushner used the private account...

Email has at all times had safety issues, and sadly, merely encrypting message transfers between e-mail servers isn't sufficient to cease spammers and different senders of undesirable e-mail. Phishing scams, spamming and e-mail spoofing depend on strategies that forge messages...

Did you already know that the majority e-mail companies like Gmail and Outlook solely use primary e-mail encryption strategies, leaving your e-mail susceptible to information assaults? This tutorial discusses the assorted information encryption strategies you'll be able to implement to...

Your PC has damaged down, and you'll’t get to the restore store till the weekend. A deadline is due, and all you've gotten is a Raspberry Pi single-board laptop. What do you do? Well, you utilize the Raspberry Pi. But...
 Loading posts...
Loading posts...  All posts loaded
All posts loaded
No more posts

