
The Winter Vivern Russian hacking group has been exploiting a Roundcube Webmail zero-day in attacks targeting European government entities and think tanks since at least October 11.
The Roundcube development team released security updates fixing the Stored Cross-Site Scripting (XSS) vulnerability (CVE-2023-5631) reported by ESET researchers on October 16.
These security patches were pushed five days after the Slovak cybersecurity company detected Russian threat actors using the zero-day in real-world attacks.
According to ESET’s findings, the cyberespionage group (also known as TA473) used HTML email messages containing carefully crafted SVG documents to remotely inject arbitrary JavaScript code.
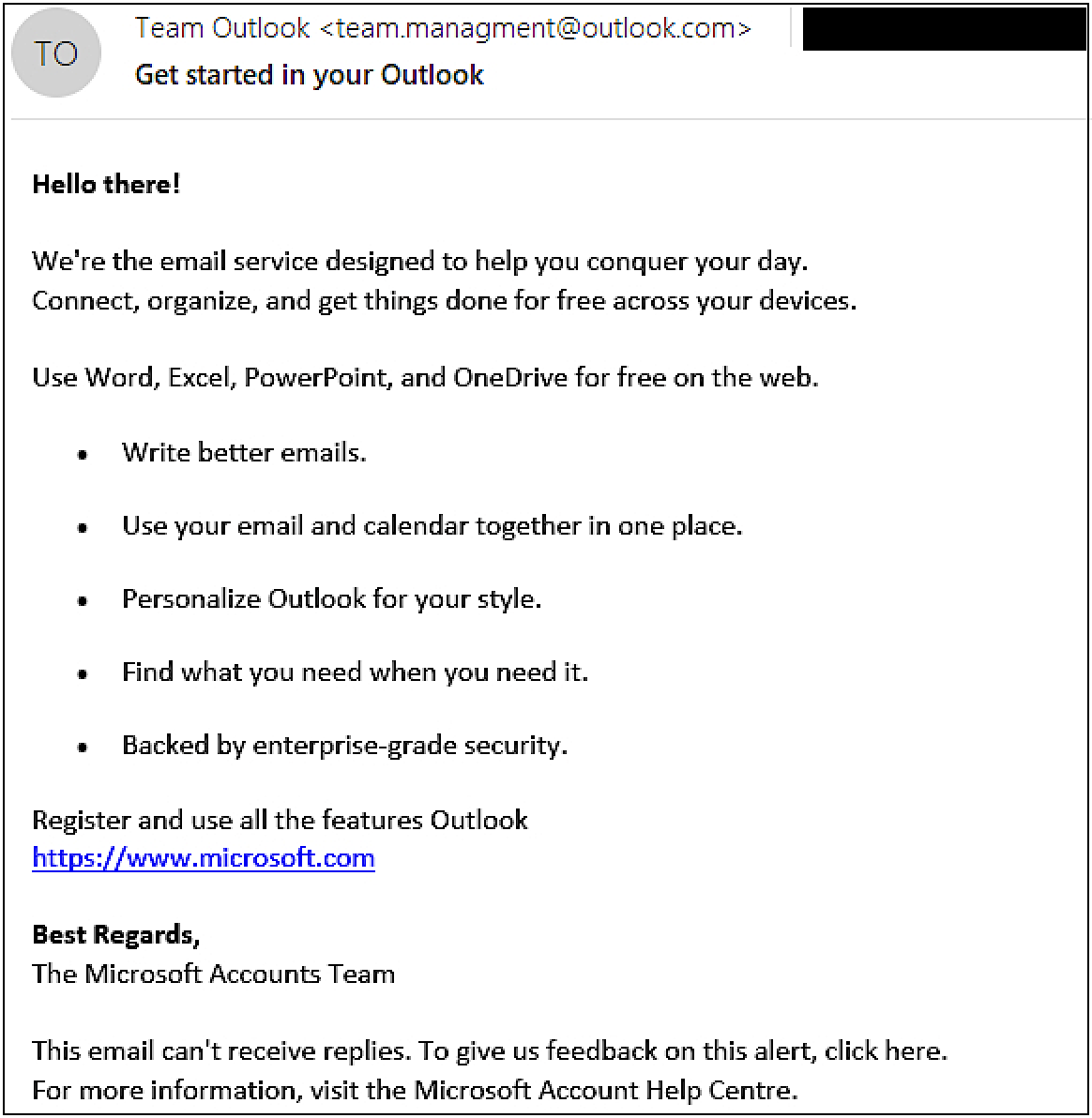
Their phishing messages impersonated the Outlook Team and tried to trick potential victims into opening malicious emails, automatically triggering a first-stage payload that exploited the Roundcube email server vulnerability.
The final JavaScript payload dropped in the attacks helped the malicious actors harvest and steal emails from compromised webmail servers.
“By sending a specially crafted email message, attackers are able to load arbitrary JavaScript code in the context of the Roundcube user’s browser window. No manual intervention other than viewing the message in a web browser is required,” ESET said.
“The final JavaScript payload [..] is able to list folders and emails in the current Roundcube account, and to exfiltrate email messages to the C&C server.”
First spotted in April 2021, Winter Vivern has garnered attention for its deliberate targeting of government entities across the globe, including nations such as India, Italy, Lithuania, Ukraine, and the Vatican.
According to SentinelLabs researchers, the group’s objectives closely align with the interests of the governments of Belarus and Russia.
Winter Vivern has been actively targeting Zimbra and Roundcube email servers owned by governmental organizations since at least 2022.
These attacks included exploiting the Roundcube XSS vulnerability (CVE-2020-35730) between August and September 2023, per ESET telemetry data.
Notably, this same vulnerability was exploited by Russian APT28 military intelligence hackers affiliated with Russia’s General Staff Main Intelligence Directorate (GRU) to compromise Roundcube email servers belonging to the Ukrainian government.
The Russian cyberspies also exploited the Zimbra CVE-2022-27926 XSS vulnerability in attacks against NATO countries to steal emails belonging to NATO officials, governments, and military personnel.
“Winter Vivern has stepped up its operations by using a zero-day vulnerability in Roundcube. Previously, it was using known vulnerabilities in Roundcube and Zimbra, for which proofs of concept are available online,” ESET said.
“The group is a threat to governments in Europe because of its persistence, very regular running of phishing campaigns, and because a significant number of internet-facing applications are not regularly updated although they are known to contain vulnerabilities.”
https://www.bleepingcomputer.com/news/security/european-govt-email-servers-hacked-using-roundcube-zero-day/






