This article is part of NarcoFiles: The New Criminal Order, a transnational journalistic investigation into global organized crime, its innovations, its tentacles, and those who fight it. The project, led by the Organized Crime and Corruption Reporting Project (OCCRP) in partnership with Centro Latinoamericano de Investigación Periodística (CLIP), began with a leak of emails from the Colombian Prosecutor’s Office that was shared with InSight Crime and more than 40 media outlets around the world. Reporters examined and corroborated the materials along with hundreds of other documents, databases and interviews. This article is republished with permission from OCCRP and the Miami Herald. Read the rest of the articles in this series here.
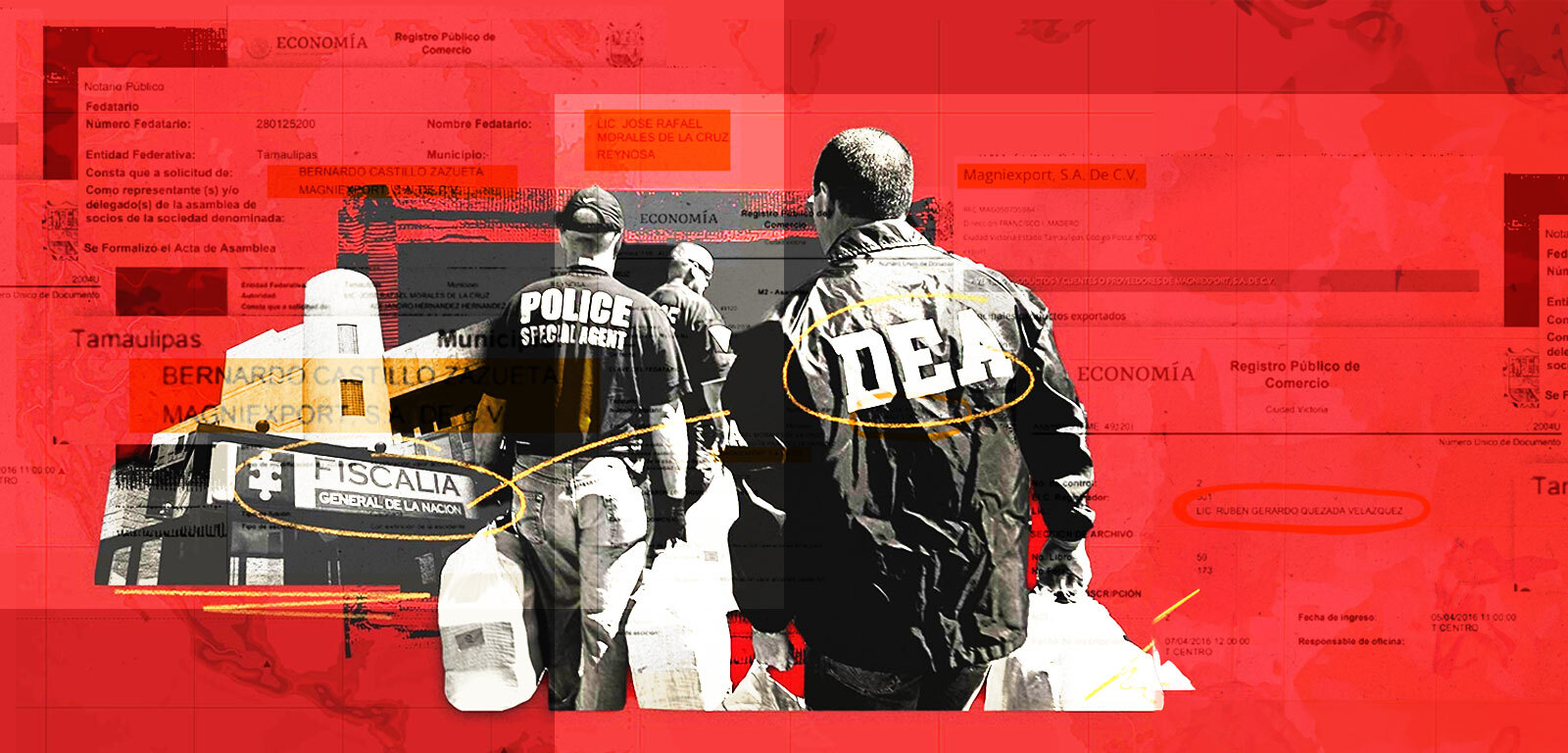
A cyber breach at Colombia’s prosecutor’s office has exposed the identities of more than 100 agents of the US Drug Enforcement Administration and other federal law enforcement entities, along with scores of their Colombian and global counterparts.
The names of at least 90 DEA agents and at least 15 Homeland Security Investigations agents were revealed in the leak, which was shared with journalists and included a huge trove of emails and other data.
Although the DEA itself was not breached and journalists are not publishing the names or any identifying information about the agents, the leak demonstrates a lack of safeguards maintained by Colombia, a strategic US ally in its efforts to counter drug cartels.
“It’s one of their nightmares because (cartels) … can identify agents and informants, especially if you are still in-country,” said Mike Vigil, a former DEA international operations chief who helped the agency expand its global intelligence footprint worldwide.
“Anytime that unauthorized people have the name of an agent or an informant, it’s not difficult to locate them.”
SEE ALSO: Suriname VP, Ex-President Linked to Drug Trafficking in Colombia AG Emails
A cartel might not want to risk the consequences of killing a DEA agent, Vigil said, but “to them, informants are fair game because they are considered traitors and will kill them to send a message to others thinking of cooperating.”
The leak from the Colombian prosecutor’s office provided the basis for the NarcoFiles, a multinational investigative reporting project by OCCRP along with more than 40 other news outlets, including the Miami Herald.
In October 2022, the Colombian prosecutor’s office acknowledged in a statement that there had been a breach, but it did not say what was exposed in the hack. The leak poses a potentially greater threat to Colombian law enforcement and other authorities since it includes names of undercover agents, witnesses, and key details about informants.
A “hacktivist” organization calling itself Guacamaya, a common word in parts of Latin America for the macaw parrot, has claimed responsibility.
Guacamaya also said it had hacked the Mexican Defense Ministry, as well as the defense departments of Chile, Colombia, and others — apparently by exploiting a vulnerability in the Microsoft Exchange email server, which is used by companies and governments around the world. (Read more about the leak here.)
In its manifesto, Guacamaya called the Colombian prosecutor’s office “one of the most corrupt organizations in the country,” and accused it of being servile to US interests.
Once it had hacked the prosecutor’s office, Guacamaya shared the five terabytes of information, including about seven million emails, with two groups, who then shared the data with journalists.
Spokespersons for the DEA and Justice Department did not respond to multiple emails requesting comment.
US Requests for Assistance
The NarcoFiles documents include dozens of requests from the US Justice Department for assistance in providing wiretaps, surveillance, arrests, and extradition of suspects wanted for drug trafficking and money laundering.
Because the documents are tied to legal investigations that will be or were used in court cases, they contain the names of agents who worked particular cases — and, in the case of witnesses or informants, often phone numbers as well as other details that could expose them to severe danger.
Some documents also contained the cell phone numbers and aliases of suspects the DEA asked for help in tracking.
The Colombian documents include extensive personal details about undercover Colombian agents and family members, often documenting personal history drawn from background checks.
SEE ALSO: Israeli Gangs’ Colombia Operations Detailed in Hacked AG Files
By contrast, DEA policy requires details about informants kept on special forms that are safeguarded and accessible only under documented circumstances, said Vigil, the former operations chief. He said that informants were given code numbers which were used to identify them.
“If the informant was mentioned in any document, it was always that number,” said Vigil, adding that it was never shared with the host country because “there was always the chance of a compromise.”
OCCRP identified at least 90 members of the DEA, most of whom work in or with Colombia, in the NarcoFiles. Some appeared in court cases or public documents, but many had no online footprint.
Tom Devine, legal director of the Government Accountability Project, a group that brings whistleblower cases against the US federal government, said that the identification of DEA personnel “poses a life-threatening risk to those agents.”
“There’s a big difference between rumors and US government confirmation of a working relationship,” he said.
Colombia has received more than $13 billion in US foreign aid since 2000, much of it for Colombia’s military and in support of counter-narcotics efforts.
It’s unclear to what degree the DEA has funded and advised its partner on information security, or what demands it has placed on protection of sensitive information.
Colombia ranked 81 out of 182 nations and territories on the 2020 Global Cybersecurity Index, published by the International Telecommunication Union with input from the United Nations. The index weighs a country’s laws, tech capacity, organizational structures, and global cooperation.
“The region’s continuing trend of major governmental cyber crises is strong evidence that coordinated effort at the national and regional levels must be intensified,” the Council of Foreign Relations said in a blog post by experts this March, which cited the Guacamaya hacks.
Related Content
https://insightcrime.org/news/dozens-dea-agents-exposed-colombian-prosecutors-office-leak/






