Every company deals with off-boarding employees. Yet it feels like many organizations make basic security mistakes in this process. Is it just a case of HR and IT being out of sync, or is this an inevitably leaky process?
This week’s episode is hosted by me, David Spark (@dspark), producer of CISO Series and Andy Ellis (@csoandy), operating partner, YL Ventures. Joining us is our special guest Lorna Koppel, CISO, Tufts University.
Got feedback? Join the conversation on LinkedIn.
Huge thanks to our sponsor, LimaCharlie

Full Transcript
[Voiceover] Best advice for a CISO. Go!
[Lorna Koppel] Take time each week to put your feet up on your desk and look out the window. Problem is that might be an interesting image you set, but it’s one that’s going to pay back in the future.
[Voiceover] It’s time to begin the CISO Series Podcast.
[David Spark] Welcome to the CISO Series Podcast. My name is David Spark, I am the producer of the CISO Series, and the co-host for this episode, the person who is joining me is Andy Ellis. He’s the operating partner over at YL Ventures. Andy, say hello to the audience.
[Andy Ellis] Hello to the audience.
[David Spark] There you go. We’re available at CISOseries.com. If you’re not familiar with it, just go to CISOseries.com, and you’ll find not just us but all of our wonderful programming. Our sponsor for today’s episode is LimaCharlie, the SecOps Cloud Platform. Hey, more about exactly what that is later in the show.
Andy, we are recording this in May, and I am actually next month going to be going to Tel Aviv.
[Andy Ellis] Which is excellent.
[David Spark] I’m very excited. I think one out of five of all of our sponsors is from Tel Aviv. It seems that way.
[Andy Ellis] It’s a very hot cybersecurity community.
[David Spark] Crazy hot, crazy hot. I have overbooked myself I think because I just have the weekend or really a day and a half on the weekend free and absolutely nothing else.
[Andy Ellis] A lot of people do that when they go to Tel Aviv.
[David Spark] But I have done a good job in that when I booked the meetings, I found where everybody was and everyone’s either walking distance and only maybe one or two cases I’ll have to do a 10-minute drive, but that’s it. I’m in pretty, pretty good shape.
[Andy Ellis] Make sure you use the Gett app for getting around.
[David Spark] I am familiar with the Gett app. That’s to call the taxis there. I had someone from Tel Aviv said, “You’re going to kill yourself doing the meetings.” Am I going to kill myself doing this?
[Andy Ellis] So you really might because some of it might be the temperature might be a little warmer than you’re expecting, I know you’re coming out of San Diego.
[David Spark] Oh, San Diego weather’s perfect. It’s not that hot at all here.
[Andy Ellis] I know. But Tel Aviv in June can start to get pretty spicy and not everybody runs on time so you may find yourself a little crunched between meetings. The real question is how many a day do you have.
[David Spark] Well, I baked 30 minutes, except for like one or two, I baked 30 minutes in between each, so I’m in good shape there. But I think I have eight to nine but I’ve included lunches and dinners there as well.
[Andy Ellis] Yeah, that’s going to be really interesting to see how you feel by the end of it. What time does your day start?
[David Spark] Not too early, 9:30 AM.
[Andy Ellis] So, what I recommend is get up in the morning and go for a walk to the beach.
[David Spark] Well, I’m going to be staying on the beach so I’m already there.
[Andy Ellis] It’s a short walk for you, go walk, walk on the beach, maybe get in a nice swim to start your day, really just get your juices flowing.
[David Spark] That’s a plan. I won’t go swim in the ocean. I live near the ocean here. And by the way, San Diego never gets hot, or where I live in San Diego.
[Andy Ellis] Right. No, San Diego’s beautiful idyllic year-round.
[David Spark] It is. This is the thing I tell to people – I almost never turn on my heat and I almost never turn on my air conditioning. I can count the hours on my hand the number of times I had to do both. Pretty much everyone hates me when I tell them that.
[Andy Ellis] It’s what San Diego’s for.
[David Spark] It’s awesome in that respect. All right. Enough of that. Enough of making other people jealous about my wonderful weather. Let’s bring on our guest who I’m excited to have, who you know as well in the Boston area. She is a CISO at a university that my sister used to teach at as well. And what I also love to say about this – many famous comedians have also graduated this university as well.
I believe Spalding Grey, Jay Leno, I’m trying to remember some of the others, but many have. Possibly our guest knows. Anyways. It is the CISO over at Tufts University, Lorna Koppel. Lorna, thank you so much for joining us.
[Lorna Koppel] Great pleasure to be here today. Thank you.
What’s the starting point for a CISO?
4:05.439
[David Spark] I hear again and again that CISOs look to other CISOs for advice, and Slack has turned out to be a really popular channel for that. Christina Shannon, now a CIO at KIK Consumer Products and a four-time CISO compiled an enormous amount of advice on what to do your first 100 days as a CISO.
It was divided into four parts – understand, plan, build, execute. Sounds great, but I can’t imagine it can be that linear, and the article is just packed with advice from colleagues. I don’t want to talk specifically about the advice, but how does a new CISO manage so much input and “what to do next”?
With so much advice you could fall into decision paralysis. Andy, what’s your advice?
[Andy Ellis] So, it’s sort of interesting because by the time this podcast drops, I’ll have just published my eBook, which is The First 91 Days as a CISO.
[David Spark] Oh, so she’s adding an extra nine days.
[Andy Ellis] She’s adding an extra nine days, I went for the quarter boundary. So, I think the answer is twofold. So, the first is, and I’ll point to my book, Chapter 48 for those who have it, there is no perfect plan, there’s only the best plan so far. You can always fall into analysis paralysis where you’re trying to get to a best plan and you miss the opportunities to act.
And so my recommendation for somebody who is starting from a whole cloth, right, they’ve come into a new program, they want to figure out what to do, is you basically just set aside slots, and you say, “There’s three quick wins I can execute on, there’s three medium-term, and there’s four long-term projects.”
And as you start to learn things, slot them into the right places. If there’s an easy win that you hear about, put it into a quick win, and after about a week you should already know what your three quick wins are and you’re already executing on those while you’re settling in on your medium- and your long-term wins.
And if it turns out that there’s a fourth quick win that pops up on week three, slot it in as a medium win and push out some medium wins. But it is better to make small victories than it is to have massive mediocre projects that go nowhere.
[David Spark] Very good point. All right, Lorna. Have you had the problem trying to deal with way too many options?
[Lorna Koppel] That is always the case. I think that follows us through our careers and that’s something that we are continually having to deal with. And I totally agree with Andy about needing to pick your wins, and you need to show success quickly. So, being able to get the people that you’re working with to see that you can deliver results and that’s something that they want, then it’s a great opportunity.
You should be focusing on those opportunities.
[David Spark] So, Andy, one of the things I keep hearing again and again is how powerful the Slack channel is to CISOs for advice. I know one CISO who used that Donut app who just had a meeting with another CISO every week, and he would just hammer that person with questions. He literally sort of built his CISO career doing just that.
[Andy Ellis] Yeah. Look, all of us learn from the people around us. Slack just makes for easy communities and there’s a number of CISO communities on Slack where you see CISOs who are communicating together, sharing advice, either in these one on ones using Donut, or just in group channels. Where there’s an Ask Us Anything channel for CISOs to say, “Hey.
This is a problem I’ve got. What are you using?” or vendor feedback. Just so all you vendors know if you’re really awful to one CISO, odds are they’re telling lots of other CISOs about it in one of the many Slack channels that are out there.
[David Spark] But also it goes the other way. If you’re very good, they have a great experience.
[Andy Ellis] If you’re awesome, you will get raves that you don’t even know are happening.
[David Spark] How do you get feedback, Lorna? Like when you have a difficult problem, how do you lean and how do you get the information? And how do you decide? You get so much input too.
[Lorna Koppel] That’s great and that’s probably the reason why I love getting involved with events and connecting with people in lots of different methods including Slack. I love forming the relationships where I can reach out and trust people and get some quick feedback on something. But be conscious of how much advice you ask for because then you do have to sift through it and figure out what you’re going to use.
[David Spark] Have you made that mistake?
[Lorna Koppel] Overwhelming amount of advice? Yes. [Laughter]
[Andy Ellis] And you have to learn who gives good advice because there are some people who will just critique what your plan is and ask you open-ended questions when you were looking for a simple answer, and other people who think there’s a simple answer when you were looking for an open-ended mind-blowing experience.
[Lorna Koppel] Totally.
They didn’t think that through all the way, did they?
8:55.046
[David Spark] Does offboarding employees pose a significant security risk? On CSO Online, Michael Hill boiled it down to five of the biggest risks – data theft, disgruntled employees becoming malicious insiders, shadow IT or SaaS usage, IT and HR being out of sync, and access not removed in a timely, thorough manner.
Does that sum it up or are there other significant issues? Which ones do you see – Lorna, I’ll start with you – companies screwing up again and again, and are there any that are inevitable? My feeling is people often take their lead list or customer list with them and often, they’ll have that long before they’re let go.
So, what do you think of this list and is there more or what’s the biggest problem on this list?
[Lorna Koppel] I think the biggest problem on this list is the fact that all of these things are not necessarily tied to leaving a company. You have access to do all of these things way before somebody leaves a company.
[David Spark] Yes.
[Lorna Koppel] So just waiting to deal with that until they leave is bad timing.
[David Spark] Where is, though, the dividing line between how we’re dealing with employees in their day to day and when we have to let them go because we do give them some level of access and we have to unload that and all these issues are, as you mentioned some there, the last one – access not removed in a timely, thorough manner – I mean, I can see that being a big one and there could be a lot of access issues that people don’t know about.
[Lorna Koppel] Yes. Managing access is a nightmare and very difficult. One of the things we always have to start with is can we trust our employees and we have to build that trust relationship. And if you can’t trust them, they shouldn’t have the access in the first place. Now that being said, if somebody’s starting to go towards termination, you want to understand what they have access to and be able to make sure that the most important ones are removed quickly.
That’s just reducing your attack surface.
[David Spark] Andy, from this list, where do you see it getting screwed up the most and is there anything that’s not on this list that we should be paying attention to?
[Andy Ellis] So, I think you correctly identified the thing that wasn’t on the list which is I guess tied to data theft, which is sales reps take their leads and customers with them. If you don’t believe that to be the case, you haven’t been paying attention. In fact, I know a number of – I don’t want to say mediocre – they’re sales reps who basically have a small set of relationships and they move from company to company and they’ll sell their product into these 50 customers, and as soon as they have done that, they’ll leave and go to the next company because they’re not interested in hunting for new relationships.
And they’ll sell to those same 50 customers, possibly against you, the person they just were selling on behalf of, or maybe they’ll wait till they’re two or three companies down the road to supplant you.
[David Spark] Yeah. I mean, no salesperson’s going to start from ground zero at every new job. No way.
[Andy Ellis] Right. But I think a lot of people don’t really acknowledge that that’s just a norm, and if you want to think of that as data theft, you can, but it puts you sort of in this weird oppositional model. I think what’s really missing here the most, especially in a termination where the employer has decided to do it, is the malicious compliance you will get from your employees who say, “Well, I’m not an employee anymore so I’m not going to tell you the important things you need to know.”
[David Spark] This is a good point.
[Andy Ellis] I know of a company recently that terminated someone who did like 75 different jobs for them, they supported every facet of the business. And they’d had a new boss that had come in that wasn’t really aware of that, and so they let the person go. And the person was like, “Well, screw you.
I’m not going to tell you what a big mistake you just made.” And in fact, they’re already back to work for the company as a contractor because all of the other parts of the business that they supported have hired them, and they’re making more money now…
[David Spark] Of course they are.
[Andy Ellis] …doing less work. That is one of the most dangerous things you can now have is this person who doesn’t really like you or specific parts of your business decides not to tell you all of the things you’ve just sabotaged and maybe they’ll come back and help you as a contractor but maybe they won’t.
[David Spark] That’s a really good point is letting knowledge go that you need.
[Andy Ellis] But you’re not even aware of.
[David Spark] Oh, worse if you’re not aware of. Lorna, have you had this experience yourself where just knowledge walks out the door and like, “Wait, we needed that”? This seems like something that’s just not addressed at all in this article.
[Lorna Koppel] I totally agree that that is a problem because in every job that I’ve been in, people have left and they’ve taken the knowledge with them and we didn’t have enough cross-training and we didn’t have enough procedures documented or any of the skeletons in the closets were not well understood, and so that’s a total problem.
I see that and a lot of people shudder being in higher ed about how long people keep access after they’ve left the institution. And that’s because we bring them back to do the work that we needed them to do that they didn’t pass off to anybody else before they left.
[David Spark] Wait a second. Andy’s showing his book. Is there something like a pre-mortem? Like, “We have to let this person go, what do they know and how can we get this covered and what can’t we get covered?” Andy, have you dealt with that?
[Andy Ellis] That’s Chapter 38 which is Don’t Be Irreplaceable, Be Unclonable. All too many organizations allow people to be irreplaceable where they’re the only one who can do a thing. And you wanted that they’re the only one who can do a specific set of things, but every one of those things is doable by someone else.
And you just have to prep for that. The easiest way to find out – send people on long vacations and see what breaks.
[Lorna Koppel] Especially be wary of the person who never goes on vacation.
[Andy Ellis] Yes.
Sponsor – LimaCharlie
15:07.387
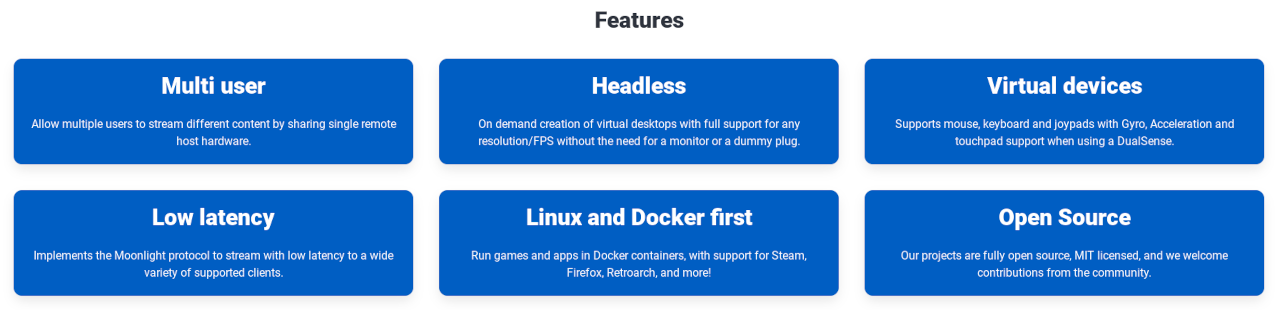
[David Spark] Before we go on any further, let me tell you about LimaCharlie. That is our sponsor for today’s episode. Gone are the days of the one-size-fits-all security solutions – our audience knows that – that do not adequately address the complexities of modern networks and evolving threats. Oh! We talk about this all the time.
So these general-purpose tools lack the flexibility to adapt to your unique environment and specific needs. I am talking to you, people. As a result, you end up with a fragmented collection of tools – oh, my God, yes – that need to be manually integrated, not good, and stitched together, leading to inefficiencies, gaps in security coverage, and extreme costs.
This all sounds familiar, right? Okay. Well, not anymore. Introducing LimaCharlie’s SecOps Cloud Platform, the modern platform that provides businesses with comprehensive enterprise protection that brings together critical cybersecurity capabilities and eliminates integration challenges and security gaps for more effective protection against today’s threats.
Now, the SecOps Cloud Platform provides all the core solutions needed to secure and monitor your organization, like deploying endpoint capabilities through a single agent regardless of the technology, alerting and correlating from logs regardless of the source, and automating analysis and response regardless of your environment.
So it’s kind of universal. Get started for free or learn more about how LimaCharlie is transforming cybersecurity for the modern area with the SecOps Cloud Platform at – now remember this web address – it’s limacharlie.io and tell them I sent you.
It’s time to play “What’s Worse?”
17:04.623
[David Spark] All right. Lorna, this game is really easy to play. It’s two bad scenarios. You’re not going to like either one. Or actually every now and then I have two good scenarios, you have to determine which one is…
[Andy Ellis] You never do that to me. You must only do that to Mike.
[David Spark] I did it with Mike just recently. But here we go. This comes from somebody, a pseudonym, so it’s anonymous user but you’ll like this one. The pseudonym is Heatless Plankton.
[Andy Ellis] Okay.
[David Spark] That’s what we’re going with.
[Andy Ellis] This person sounds very cold.
[David Spark] This is kind of an ethical dilemma one.
[Andy Ellis] Ooh.
[David Spark] All right? The CEO is hacked! A zero-day flaw, a zero-click remote code execution. But good news – you caught it before any real damage was done, meaning there’s no reporting obligation and no one else needs to know about this. The bad news is you have enough information about the attack to prevent other organizations from being attacked but sharing those details would expose your CEO and the organization as being victimized, having a considerable negative impact to your organization.
Do you share the exploit with the security community or do you keep the attack details private?
[Andy Ellis] Oh, this one’s easy. You share the exploit. In fact, when I was at Akamai, my CEO would get up onstage on a regular basis and show phishing messages that were good that he had clicked on.
[David Spark] Really?
[Andy Ellis] Like, we do not expect our employees to be perfect and you just gave this scenario of oh, my God, the perfect phish that hit the CEO. The CEO’s not going to be embarrassed, now it’s a point of pride, “I was hacked by the best, not by some random anybody doing this phishing. This was really good and look how great our security was.
We caught it, we detected it, we prevented bad stuff, and now we’re going to share with everybody so that nobody else gets hit with this on the off chance that the rest of their security program is not as good as ours.” This is fantastic. I love this. This is not negative, this is positive.
[David Spark] Actually, you make a very, very good point, Andy. I’m going to assume you’re going to agree with this, Lorna, yes?
[Lorna Koppel] I totally agree. Find a way to share.
[David Spark] Yes. Find a way to share. First of all, who wouldn’t get nailed by a zero-day attack, right?
[Andy Ellis] I mean, that’s the whole thing. We always are saying you never know who’s going to get hit. And now by the CEO saying they got hit, every one of my employees knows it’s okay to say, “I got hit too.”
[David Spark] So this is actually far from, like we were saying, far from a “What’s Worse?” An actually wonderful scenario.
[Andy Ellis] Absolutely. So, thank you, Heatless Plankton, I really like that one. Sorry if we left you feeling cold and adrift in the oceans of “What’s Worse?”
Would this person be a good fit for the job?
19:59.568
[David Spark] We here at CISO Series just put out a job listing for a writer/producer who knows cybersecurity, which was one very critical requirement. So, I found a few good candidates and by the time you hear this we will hopefully have hired someone. Unfortunately, 90% of the applications were truly garbage.
I provided simple instructions on how to apply, and about 5 out of the 50 followed instructions. How can you hire someone who doesn’t know or care about your company and can’t follow instructions? It’s a pretty low bar to clear, but practically – well, not no one can do it, but a very low percentage can do it.
So, if someone followed my instructions and wrote a cover letter that clearly followed what I asked for, that got my attention. There was truly no resume I looked at and said, “Oh, I have to hire this person.” Andy, I’ll start with you. I get the feeling that most people do not know how to apply for a job.
Agree or did I just get a really bad batch?
[Andy Ellis] So, I think you’re getting a mixed batch, which is you have to understand some of the dynamics of what’s going on out there. There are some people who are on Unemployment Insurance and they’re required to apply for jobs and not all of them are interested in getting jobs.
[David Spark] I will accept that. I was, by the way, unemployed for a period of time and didn’t.
[Andy Ellis] Right. Look. I’m not saying this about everybody who’s on Unemployment, I’ve been there too, I desperately wanted a job. But I’ve known people who are like, “Oh! Why should I go work? I’m totally fine with what I’m doing here.” And so least amount of effort to send out some applications so they can say they’ve applied.
Great. So, that’s one batch. You have another batch and these are a lot like you know the sales lead gen calls we always talk about that are these just cold spamming messages? They’re people who think that quantity has a quality all of its own, and that’s the challenge. You can apply for a thousand jobs and if it’s a bad application, the job you’re going to get is not one you actually want.
[David Spark] And I should say I hear a lot from people saying, “I’ve applied for 500 jobs and I’ve got nothing,” and I said, “If you’re one of these 90% that I get, I can see why you’ve applied for 500 and got nothing.”
[Andy Ellis] Right. And so if you’re one of those people who are saying, “Look. I’m applying for tons and tons of jobs and I’m not getting any feelers,” think about what your application is saying about yourself. Like this is some feedback you should take of how do you get better so that you do stand out, so that you do look different to the hiring manager?
[David Spark] Mm-hmm. Lorna, I’m sure you’ve put lots of job requirements. I will say this – when I did this experience, and I’ve hired a few people, my insight as to how people apply for jobs is very different than when I was applying for jobs myself. I think people applying for jobs should really get some insight into the actual hiring process because I think they would do this a lot differently, yes?
[Lorna Koppel] I totally agree. And the concept of applying to a job and not actually looking at what you’re applying for and showing the passion for the job and following simple instructions.
[David Spark] Oh, my instructions were really simple.
[Lorna Koppel] I know. And if you can’t follow simple instructions, why do you think they’re going to want to even hire you in the first place? It doesn’t show any engagement between you and that actual job opportunity.
[David Spark] One of my requirements, as I said, cybersecurity knowledge, and writing about cybersecurity for at least three years. One person, and through one of the platforms Indeed, it allows people to sort of send a one-way interview, one person clearly asked ChatGPT, say, “Explain cybersecurity to me,” and he just read that on the video.
[Laughter]
[Lorna Koppel] Oh, my.
[David Spark] It was awful!
[Lorna Koppel] Oh, my.
[David Spark] Yeah. I was staring at him like, “This can’t be as bad as it looks, is it? It is. It’s that bad.”
[Lorna Koppel] And that person has wasted your time and theirs.
[Andy Ellis] At that point why don’t you just hire ChatGPT to do your writing? Why waste the middleman?
[David Spark] Well, no. I’m not going to do that. The thing is is that I realize that I care so little about people’s resumes and I care if they can show true interest. If you can show true interest and capability, that trumps any resume that I see.
[Lorna Koppel] 100%.
[David Spark] I mean, how much has someone with talent and interest and capability sans decent resume won a job for either of you?
[Andy Ellis] Oh. I’ve had people that we planned on hiring before we ever saw their resume because we went and met them somewhere and they stood out and we were actively recruiting them for years, right?
[David Spark] Mm-hmm.
[Andy Ellis] Look. That’s problematic for a lot of reasons. It means that other people don’t necessarily get that shot.
[David Spark] That face to face, yeah.
[Andy Ellis] But it’s a challenge and I went into the hiring process with the goal of eliminating candidates as fast as I could. It took me a long time to realize that I did no one a service of advancing a candidate from one phase to another if I had any reason to say no. So if your resume gives me a reason to say no, then you’re done.
I’ve got too many resumes to take a chance on something that has obvious red flags at that stage.
[David Spark] Right. So, have you done this, Lorna, where the resume meant nothing and everything else sold you? And what percentage does everything but the resume weigh in your hiring process?
[Lorna Koppel] Well, for me, resume may get you to get a phone call but then from then on, it’s all about the presence and the passion and the attitude and the engagement and the motivation and what you’re really going to bring to the job, which is not usually on the resume.
[David Spark] Mm-hmm.
[Lorna Koppel] So, yeah, 100% of what I look for is based on the interview and getting to know the person.
[Andy Ellis] The way to look at it is your resume keeps you from getting a phone screen. Your ability to speak keeps you from getting an in-person interview. You’ve got to be able to communicate on the phone to get to an in-person interview. Once you’re in the in-person interview, now you’ve got a shot at the job.
[David Spark] Let me ask you this because this actually came up with one interview subject. They knew our brand, they knew our product, but it’s clear they didn’t do too much research beforehand. And I asked them a question and they said, “Let me spend some time and I’ll get back to you.” Are you okay with that response?
[Andy Ellis] It depends on what the question is.
[David Spark] I pretty much asked what would you want to do differently, like looking at our brand and what we do, what would you like to do differently, that’s what I asked.
[Andy Ellis] If I were the interviewee, I think that’s a trap question. Like I don’t know if you’re so arrogant that you’re going to be grumpy at me if I tell you there’s something to change.
[David Spark] No, no. I’m happy with any answer, to tell you the honest truth.
[Andy Ellis] But not all hiring managers are.
[David Spark] Oh, I didn’t throw it as a trap. Honestly, I just wanted to hear thoughts and ideas.
[Andy Ellis] But at that point, I might say, “Let me think about that for a minute,” because I didn’t walk in with an eye to how I could change the brand.
[David Spark] Right, right. And that’s why I was accepting, I was very accepting, I’d be like, “Yeah, yeah. Take a look at it. Send me a message.”
[Andy Ellis] Great. You’ve got somebody who’s diplomatic.
[David Spark] Yeah.
[Lorna Koppel] Yeah, and I’ve seen that too where a lot of times the person when asked that pointed question, they get nervous. And so I’ll use that as a judgment call whether or not, okay, they just got themselves so nervous that they needed to take some time to breathe and they can find they can come back to me.
But the interview isn’t going well otherwise, then it’s just another symptom of they’re not engaged and they don’t really understand what they’re applying for.
[David Spark] The interview was going fine actually. It was going fine.
[Andy Ellis] Then I would be really happy with that. I would take that as somebody who’s like, “You know something? Rather than just make up something on the spot and just ramble out of nervousness, I’m going to see if I can avoid picking this fight right now and do it later.” That’s the sort of person you want to have in your workforce.
[David Spark] That’s how I took it. I did some writing for a company a long time ago and they did a thing where they bring a bunch of potential writers in a room and they challenge them with a spec script, and the sole reason they did that was just to find out who was serious because half of the people in the room never sent in a script, ever.
Sometimes you have to test people to see where they’re at.
That might not have been the best decision.
28:25.307
[David Spark] “It’s the culture of speaking out and asking questions that makes the organization safer, not some BS phish test percentage,” said a redditor in the cybersecurity subreddit in response to another redditor who was getting pressure from his management to punish their click-happy employees for failing phishing tests.
The redditor wanted to know what others are doing to drive home the point that clicking can be dangerous. Now, the CISO Series audience knows that the ideal situation is getting employees to come to you if they see something phishy. We talked about this before, like the CEO of Akamai. But there were some other arguments.
Another popular response was, “Habitual clickers get reported to their supervisors and get their email access taken away until they complete remedial training.” I can see Andy shivering right now. [Laughter] To which another responded, “Yeah. It’s part of the job now. It’s not a nice to have, it’s safety training.
They don’t let someone who failed their forklift test keep using a forklift.” Andy, I know you’re a fan of creating other redundancies for happy clickers, but what do you think of this last response? It’s for your own safety and our safety that we take your email away until you learn how to use it. Could this scared straight tactic actually work?
[Andy Ellis] Yeah. So, I want to take the person who thinks that email is even remotely as safe as a forklift and tell them that it’s their fault that email is so unsafe and we’re taking away their job until they’re capable of deploying safe technologies.
[David Spark] But what if someone’s a forklift operator? That’s their job.
[Andy Ellis] No, no. But a forklift has so many safeties built into it that it’s actually relatively easy to be relatively safe with a forklift. I can give you forklift safety training and then you can use the forklift to do your normal job and it’s fine, right? I don’t expect you to worry about somebody putting land mines in the pallets so that when you go to lift them up, they blow up.
I wouldn’t blame a forklift operator for that if somebody put bombs on a pallet and exploded them. But that’s what we do with email. Email clients suck, they are awful, and if you’re responsible for an email client and you’re listening to this, I’m not normally this harsh, but I want to say you should be ashamed of yourself and of your product because I am tired of us blaming the humans for being incapable of using an unsafe product, like in a hostile environment, perfectly.
[David Spark] What I’m hearing from you, Andy, is that all email products out there should have as many safety precautions as a forklift.
[Andy Ellis] I would settle for half as many.
[David Spark] All right. So, Lorna, Andy’s passionate about this. Does scared straight tactics work at all here?
[Andy Ellis] No. No, no, no. It’s the biggest draw from productivity as well. And reality, with generative AI and all the things that are going on, they’re getting better and better, and it is really hard to tell the difference. And so what are we going to do with our users when they can’t tell the difference between what we’re sending out and what others are sending out?
It’s not fair to punish the user. It’s all about what can we do to help them be better informed, better to notice what to do.
[David Spark] A number of years ago, and I’m going to just roughly say maybe eight, nine years ago, correct me if you think I’m wrong here, I thought there was a time that if you were just smart about security in general, you wouldn’t get hacked. But now, that is so no longer the case. Do you believe there was a time that if you’re just generally smart, you wouldn’t get hacked?
You’re nodding your head no. There was never a time like that.
[Lorna Koppel] Well, I think that it’s gotten harder to be smart enough.
[David Spark] That’s right, yes, way harder. But there was a time that you could do it, yes or no?
[Lorna Koppel] Yes. I think there was, yeah.
[David Spark] Maybe nine years ago.
[Andy Ellis] No, so I used to use a dumb email reader, like I read email in EMAX [Phonetic 00:32:45], weird to call EMAX a dumb mail reader but as a mail reader it was pretty dumb. It disabled all of the links. It showed me the actual sender of the message, right? Now, granted I couldn’t see images, I had to copy and paste links manually.
So not very user-friendly but it also had all of the sharp edges filed away. And that’s the problem is that we’ve taken all the sharp edges and we hide them from the users but they’re still there. If you get mail and your mail client will display the From field as if it were the sender, which anybody can put in any name they want, so if I get to send mail to David Spark claiming to be Mike Johnson, saying, “Hey, David.
I’m done being a host on the CISO Series, give Andy Ellis all of my slots,” if your mail client will say that came from Mike Johnson, that is not your fault, David.
[David Spark] Good point.
[Lorna Koppel] I totally agree. What do we expect when we have such a diverse community that they don’t understand all the stuff behind the scenes and we expect them to in order to catch these things?
[David Spark] I’m going to just throw this out at the last to both of you because I’ve never heard it from you. Is there any case where the stick, some kind of punishment, works with bad security behavior? Is there ever a scenario?
[Andy Ellis] So, there’s specific scenarios when users do things that required malicious intent. Like I’ve had users who took production servers and said, “I’m going to run my own personal gaming server on this. I’m literally going to steal from my employer.” And then when it finds out I’m being caught, I’ll go delete everything so I hope I get to hide out.
Okay, you’re getting the stick at this point.
[David Spark] Right. Well, when you’re doing something purposely malicious.
[Andy Ellis] Right. Purposely malicious or where you’re stealing. Even if you didn’t think of it as stealing, you’re stealing services from a customer, there’s a lot of violations in there. But if the answer is, “I’ve got a policy,” and the policy looks great on paper but doesn’t actually work, here is my question.
If you require employees to click things to get paid, how dare you complain that an employee clicks things? Just right there. They can’t get paid if they don’t click emails that come from people they have never communicated with in the past. So how do you dare say that it’s a bad security practice on the part of the user to then click things?
[David Spark] Good point. Lorna, obviously malicious, no dice. Any other scenario that you can see a stick would be appropriate?
[Lorna Koppel] Depends on how widely you cast the malicious. The concept of sharing your work computer at home, sharing your login so that other people can do some work for you, things like that, I think that probably falls into the malicious category. But I agree. A stick… If it’s a compliance error and you’ve made compliance mistakes in the past and purposely mishandling it, I think that does fall into the malicious category but otherwise I don’t think a stick works.
[David Spark] Good point. No sticks. We do not recommend sticks.
[Andy Ellis] The best stick, if you want to go down the stick path, right, is everybody here’s trying to jump to, “I want to have the stick and beat someone with it.” The best stick is the attention of the security team. If you have an employee who’s doing things that are correctable, you correct them through attention.
We’re going to give you lots of love until you are tired of our love.
[David Spark] That is tough love from Andy Ellis. That’s the name of your next book, by the way. You can give me credit for that, by the way.
[Andy Ellis] ChatGPT thinks I already wrote that one.
[David Spark] Oh, does it? [Laughter]
Closing
36:30.633
[David Spark] Lorna, that was awesome. Thank you so, so much. I’m going to let you have the last word here. But first, I want to thank our sponsor LimaCharlie, limacharlie.io. Go there. Andy, by the way, has this book called 1% Leadership which I have a copy of as well, which I will have read by the time this episode comes out.
[Andy Ellis] Excellent.
[David Spark] I’m so overloaded with work. That’s why I’m hiring somebody because I’d like to be reading books these days, I haven’t been. And I would like to do what Lorna suggested at the beginning of the show is put my feet up and look out the window because I have a beautiful, nice area that I live in too, for that matter.
Andy, any last words for today’s show?
[Andy Ellis] Everybody should buy my book. I’m not telling you to preorder it, just go get it.
[David Spark] You can just get it now.
[Andy Ellis] Just get it.
[David Spark] You say if you purchase it from your local bookstore, you sign the local ones so you can get a signed copy?
[Andy Ellis] So, if you go to Book Ends in Winchester, Massachusetts, you can just Google them or go to csoandy.com/book and there’s a banner for them, and you can tell them when you order a copy of the book that you would like a signed copy and they will send you a signed copy.
[David Spark] Mm-hmm. I will have to tell you stories and maybe we’ll save it for a future episode of all the celebrities I’ve had sign books and the things that I’ve asked them to say when they sign it. That’s a whole other episode.
[Andy Ellis] Okay. That sounds fascinating.
[David Spark] Lorna, are you hiring over at Tufts?
[Lorna Koppel] I am not, I really wish I was, but hopefully in the future we’ll be having some more positions that’ll become available in the security team.
[David Spark] Do you have any other last words for today’s episode?
[Lorna Koppel] As a CISO, I think it’s really important for everybody to take their time and really do kick back and relax. You got to think and give yourself some slack and think about your mental health because if you can’t take care of yourself, you can’t take care of your family and you can’t take care of what you’re responsible for at work.
So take the time and chill.
[David Spark] Great advice. Thank you very much. That is Lorna Koppel, she is the CISO over at Tufts University. Also Andy Ellis, he is the operating partner over at YL Ventures. And you, our audience, we greatly appreciate your contributions and send us more “What’s Worse?” scenarios and also great topics of conversation.
We love it for the show. We appreciate your contributions and listening to the CISO Series Podcast.
[Voiceover] That wraps up another episode. If you haven’t subscribed to the podcast, please do. We have lots more shows on our website, CISOseries.com. Please join us on Fridays for our live shows – Super Cyber Friday, our virtual meetup, and Cybersecurity Headlines Week in Review. This show thrives on your input.
Go to the Participate menu on our site for plenty of ways to get involved, including recording a question or a comment for the show. If you’re interested in sponsoring the podcast, contact David Spark directly at [email protected]. Thank you for listening to the CISO Series Podcast.
https://cisoseries.com/please-take-some-pens-and-our-company-data-on-your-way-out/