A trio of e-mail authentication requirements work collectively to enhance e-mail deliverability for the sender and e-mail security for the recipient.
Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting, and Conformance (DMARC) assist to make sure that emails despatched out of your firm are actual and that malicious actors should not spoofing or in any other case tampering with them.
SPF, DKIM, DMARC
SPF, DKIM, and DMARC present the receiving e-mail server {that a} given message was despatched from a licensed IP tackle, that the sender is genuine, and that the sender is clear about its identification.
Let’s take each in flip.
Setting up SPF information to your area entails including a kind of TXT report containing a licensed checklist of outgoing mail servers to the Domain Name System (DNS). SPF verifies that emails from your online business’s area come from an authenticated supply, not an imposter.
DKIM keys include two components: a public key saved within the DNS and a personal key saved on the sending mail server. The DKIM signature hooked up to every outgoing e-mail is utilized by recipients’ mail servers to confirm its authenticity. DKIM may point out if a given e-mail message has been altered.
DMARC is a coverage mechanism that enables an organization to regulate how incoming emails from its area needs to be dealt with in the event that they fail the SPF or DKIM authentication. The choices are “reject,” “quarantine,” or “none.” This might be like an alarm bell if a wrong-doer is attempting to make use of your area.
SPF Records
Setting up an SPF report requires entry to your area’s DNS information on the registrar, comparable to GoDaddy or related. If you might have ever needed to confirm your area or transfer it to a brand new server you seemingly up to date its DNS report.
An SPF report is just a TXT report in your area’s DNS.
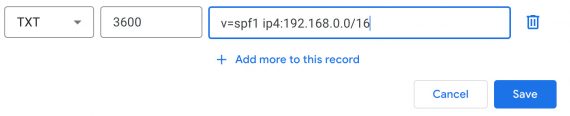
The SPF report might be of the sort “TXT.” And it should begin with the model of SPF you’re utilizing.
v=spf1
The model is adopted by an inventory of approved IP4 or IP6 addresses, as in:
v=spf1 ip4:192.168.0.1
This SPF report would authorize emails from the 192.168.0.1 IP tackle. To enable a variety of IP addresses, you would use Classless Inter-Domain Routing (CIDR) notation (typically referred to as “slash” notation).
v=spf1 ip4:192.168.0.0/16
The above SPF report would authorize a variety of IP addresses from 192.168.0.0 to 192.168.255.255 — that is what the “/16” signifies.
Using the prefix “a,” an SPF report can authorize a website by identify. The report beneath authorizes a server related to the instance.com area.
v=spf1 a:instance.com
Similarly, the prefix “mx” (“mail trade”) authorizes particular mail servers.
v=spf1 mx:mail.instance.com
To authorize a third-party sender, use the prefix “embody.” The instance beneath permits each an IP vary and Google servers.
v=spf1 ip4:192.168.0.0/16 embody:_spf.google.com
There are additionally two SPF qualifiers. The first is ~all with a tilde (~). The second is -all with a hyphen (-).
The tilde model (~all) is a soft-fail qualifier. In most instances, the receiving e-mail server will settle for messages from senders that aren’t within the related SPF report however think about them to be suspicious.
The hyphen model (-all) is a hard-fail qualifier. The receiving e-mail server will seemingly label messages despatched from a server not approved within the SPF report as spam and reject them.
Finally, all of those could also be used collectively for comparatively advanced authorizations.
v=spf1 ip4:192.168.0.0/16 a:instance.com embody:_spf.google.com
Remember, SPF information assist the receiving email servers establish genuine e-mail messages out of your firm’s area.
DKIM Keys
DKIM protects your area and helps to forestall anybody from impersonating your organization. The two DKiM keys enable the recipient’s e-mail server to confirm that your organization despatched the message and that it was not altered after you despatched it.
The first step in establishing DKIM is producing the keys — one public and one non-public. The non-public secret’s safe on the server used for sending emails out of your area. The public secret’s added to the DNS as a TXT report.
The tough half is producing the keys because the actual process for creating them varies from one e-mail service supplier to the subsequent. And it’s utterly totally different if your organization hosts its personal mail server.
Email service suppliers supply directions. Here are a number of examples in no explicit order.
- Mailchimp: Set Up Email Domain Authentication,
- Klaviyo: How to Set up a Dedicated Sending Domain,
- Zoho Campaigns: How to Authenticate My Domain,
- MailerLite: Email domain authentication,
- Campaigner: DKIM, SPF, and DMARC,
- ConvertKit: Using a Verified Domain for Email Sending,
- MailUp: Maximizing Deliverability for Your Emails,
- ActiveCampaign: SPF, DKIM, and DMARC Authentication,
- Keap: DKIM.
In every case, the DKIM is accomplished if you add — copy and paste — the e-mail supplier’s CNAME report to your area’s DNS. This report(s) represents the general public key to authenticate your organization’s outbound email marketing messages.
DMARC
DMARC gives one other layer of safety and likewise instructs e-mail servers what to do with messages that fail SPF or DKIM authentication.
The basis of DMARC is a TXT report positioned in your area’s DNS. This will comprise the DMARC coverage with at the least two parts:
- An e-mail tackle to obtain combination studies of e-mail authentication, and
- The motion to tackle emails that fail authentication (i.e., reject or quarantine).
Here’s an instance DMARC TXT report in a DNS:
v=DMARC1; p=quarantine; rua=mailto:[email protected]; ruf=mailto:[email protected].
The report begins with the DMARC model.
v=DMARC1;
The “p” factor assigns the motion for emails that fail authentication. In this case, it’s set to “quarantine,” which instructs the receiving server to maneuver such messages to a holding space. Other choices embody “none” — which doesn’t cease the e-mail however screens SPF or DKIM failures — or “reject.”
p=quarantine;
The prefixes “rua” and “ruf” inform the receiving server the place to ship combination studies (rua — Reporting URI for Aggregate knowledge) and forensic studies (ruf — Reporting URI for Failure knowledge). These studies can disclose a felony making an attempt to impersonate your online business.
Additional modifiers embody:
- pct — the share of e-mail messages subjected to the DMARC coverage.
- sp — the DMARC coverage for subdomains.
- adkim — assigns strict (adkim:s) or relaxed (adkim:r) mode for DKIM.
- aspf — assigns strict (adkim:s) or relaxed (adkim:r) mode for SPF.
Third-party companies might help generate a DMARC report based mostly on the official standard. These companies embody:
Protect Sender and Recipients
Setting up SPF, DKIM, and DMARC information to your area ensures that e-mail servers acknowledge messages out of your firm as genuine and reject imposters. The outcome protects your organization’s status and shields clients from phishing assaults and different varieties of e-mail fraud.
https://information.google.com/__i/rss/rd/articles/CBMiU2h0dHBzOi8vd3d3LnByYWN0aWNhbGVjb21tZXJjZS5jb20vaG93LXNwZi1ka2ltLWRtYXJjLWRyaXZlLWVtYWlsLWRlbGl2ZXJ5LXNlY3VyaXR50gEA?oc=5






