The IT business has developed quickly. But you actually agree that I can’t say the identical about cybersecurity. It stays a serious concern for many individuals and corporations. In reality, information leaks can happen at any time!
Individuals, corporations, and authorities businesses can expertise monetary and reputational injury if their delicate data will get uncovered to unauthorized events. Cybercriminals can also leverage safety vulnerabilities in IT infrastructures and steal delicate information for private positive aspects. Businesses will then profit from monitoring cybersecurity dangers and taking acceptable steps to forestall information theft.
In this text, I’ll clarify what a knowledge leak is and additionally talk about some sensible options you possibly can implement to stop one from occurring. Let’s start with a definition within the following part!
What Is a Data Leak?
A knowledge leak is an unauthorized information switch from inside an organization to a 3rd social gathering. This information switch can happen in 2 methods. The first approach is by way of digital means, similar to electronic mail or file switch. The second is thru unauthorized bodily entry to gadgets similar to USB keys, laptops, and tablets.
If you endure an analogous information leak, you danger compromising information similar to:
- Financial information similar to checking account particulars, bank card numbers, invoices, and tax experiences
- Personal data like names, addresses, cellphone numbers, and different data you employ to determine, find, or contact people
- Medical information like data that describes your previous, current, or future bodily and psychological well being situation
- Intellectual property others can profit financially from, similar to patents, blueprints, commerce secrets and techniques, and contracts
- Military, political, or different delicate data that may compromise the security of a rustic and its residents, similar to categorized paperwork, assembly recordings, and agreements
These information leaks can have each short-term and long-term penalties and may cause severe losses. Let’s discover what occurs when third events have entry to your confidential data.
What Happens When You Suffer a Data Leak?
Generally, the main concern is the vital monetary and reputational loss your agency can face. For instance, if cybercriminals entry your clients’ non-public information, this may result in identification or monetary theft. In this case, your clients might demand compensation from you. Another instance is when your opponents acquire entry to inside commerce secrets and techniques and use this stolen information to their benefit.
The speedy enterprise prices of a knowledge leak embrace:
- Legal charges
- Regulatory fines as a result of failure to adjust to information safety legal guidelines in your nation
- Cybersecurity investigation prices
- Losses as a result of operational disruption
- Public relation administration and different prices similar to buyer compensation, and so forth.
Data leaks may also have long-term, oblique impacts on a enterprise similar to:
- Drop in share costs
- Increase in enterprise or public legal responsibility insurance coverage premiums
- Reduction in traders’, companions’, and clients’ belief
- Loss of mental property, market share, and market monopoly
I wouldn’t need to undergo all this injury administration. What about you? That’s why I’ll describe how a knowledge leak can happen that will help you keep away from it within the first place.
How Does a Data Leak Occur?
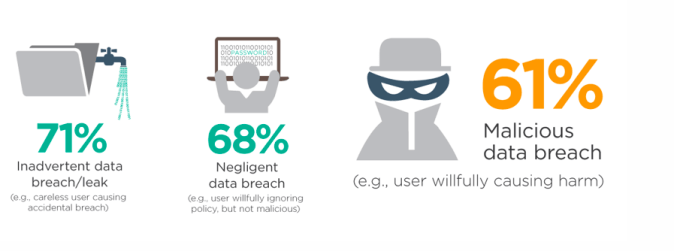
It’s vital to know particularly the supply of a knowledge leak so you possibly can simply discover a resolution. To simplify issues, you possibly can group information leaks into 3 broad classes: unintended information leaks, inside threats, and exterior threats. Let’s talk about every in additional element.
1. Accidental Data Leaks
An unintended information leak happens when a trusted particular person, similar to an worker or administrator, makes a safety mistake. For instance, they might electronic mail confidential data to the improper recipient. Some of the ways in which unintended information leaks happen additionally embrace:
- Loss of firm gadgets as a result of worker carelessness
- Employees by accident clicking on hyperlinks in unauthorized or spam emails
- Teams utilizing weak passwords or revealing safety data by mistake to outsiders
An group remains to be required to take obligation for all security-related errors. It’s vital to notice that you just’re chargeable for implementing safety insurance policies and procedures, similar to worker coaching. This may also cut back the probabilities of unintended information leaks from taking place.
2. Internal Threats
Disgruntled staff or companions might purposely leak data as revenge or in alternate for monetary profit. They might:
- Misuse credentials and entry privileges to repeat delicate information to their gadgets
- Email confidential data on to criminals
- Hand over passwords or login entry data to 3rd events
- Create pretend system credentials, similar to usernames and passwords, for vital providers
- Install malicious software program, like different malware types, into your system
While you possibly can take authorized motion in opposition to the worker or staff concerned, it may be very difficult to construct your case. This may also enhance your authorized prices, relying on the severity of the information leak.
3. External Threats
Sometimes, cybercriminals purposefully goal an organization’s IT infrastructure and try to steal information for private acquire. Types of exterior assaults embrace:
- Malicious software program like viruses, worms, malware, and ransomware
- SQL injections the place the attackers insert malicious code into your net utility kinds
- Remote assaults that concentrate on peripheral gadgets like printers, point-of-sale terminals, or routers
- Attacks by which criminals pose as licensed people; for instance, a pretend electronic mail from the corporate CEO requesting a password change
- Social engineering attacks the place criminals use staff’ social media exercise to trick them into giving entry to inside information
I’ve created a easy desk to summarize the three broad information leak classes and how the identical information leak differs between them. Feel free to refer again to it sooner or later.
| Accidental Data Leak | Internal Threats | External Threats |
| Employees shedding their gadgets | Employees promoting or handing private gadgets containing information | Cyberattackers stealing information from unsecured gadgets |
| Employees utilizing weak passwords or sharing them by accident | Employees handing over passwords or creating pretend credentials for criminals | Cybercriminals utilizing malicious software program to realize entry to your gadgets |
| Employee by accident clicking on spam electronic mail hyperlinks that set up malicious software program | Employee deliberately putting in software program that mechanically sends information to criminals | Cybercriminals attacking your community with viruses, worms, or different sorts of malware to entry your information |
Now that you just perceive what a knowledge leak is and the way it happens, let’s take a look at methods you possibly can forestall one within the first place.
How to Prevent a Data Leak from Happening
Your firm’s information flows by a series of applied sciences and providers. For instance, while you ship a file attachment in an electronic mail, the information goes out of your system to your electronic mail server, then to the recipient’s system. In this case, the information flows by a number of cloud providers, networks, and IT methods in additional complicated functions.
Additionally, many methods retailer a number of copies of the identical information, which makes total information safety much more complicated. That’s why you have to assess all parts in your agency’s IT methods to determine and take away information chain weak hyperlinks. In impact, you’re discovering any loopholes to stop information leaks.
In this part, I’ll offer you some finest practices you possibly can implement to prevent a data leak. Let’s dive proper in!
Identify Sensitive Data
An integral step in information safety is to kind and categorize all vital information. This classification will allow you to assess key IT methods. You may also use it to tailor essentially the most environment friendly defenses for every information class.
Monitor Network Access
Cybercriminals sometimes carry out preliminary safety assessments in your community earlier than launching a full-scale assault. These assessments assist them plan their assaults extra successfully. You can detect and forestall information leak assaults through the use of software program to monitor your community visitors . You may additionally set alerts for any suspicious exercise.
Secure Endpoints
Endpoints are any gadgets that talk with your small business community remotely, both by way of end-users or autonomously. For instance, gadgets might embrace mobiles, laptops, good sensors, and so forth. With most companies now permitting distant work, endpoints have grow to be dispersed, making them tougher to safe. You should prepare your staff to make use of these gadgets securely and keep away from unintended information leaks.
Evaluate Third-Party Risk
A agency’s IT infrastructure sometimes has some elements that exterior distributors partially or absolutely handle. You should assess third-party safety insurance policies frequently to make sure safety incidents on their finish don’t trigger unintentional information leaks for you.
You can implement the above safety practices to cut back the danger of a knowledge leak occurring. You’ll additionally want know-how to automate and make information safety extra environment friendly. Let’s discover a number of the high information leak prevention software program out there available in the market as we speak subsequent.
Top 3 Data Leak Prevention Software
You can cut back the probabilities of a knowledge leak taking place by manually implementing the beforehand talked about safety practices. You do have know-how on the market that may make life a lot simpler for you although. In this part, I’ll talk about 3 of the highest information leak prevention software program, beginning with GFI MailEssentials.
1. GFI MailEssentials

Price: Ranges from $25 to $40/mailbox/yr
Emails are a vital supply of knowledge leaks for any group. GFI MailEssentials is a software program service that mechanically scans and protects your agency’s inboxes in opposition to viruses, spam hyperlinks, and malware. It additionally incorporates the mixed energy of 4 antivirus engines powered by main manufacturers, together with Sophos, BitDefender, Avira, and Cyren.
Using GFI MailEssentials, you possibly can:
- Block email-borne malware and viruses extra successfully
- Stop emails that hyperlink to phishing websites, or come from blocked DNSs and cast senders
- Meet compliance necessities
- Improve electronic mail efficiency
- Control electronic mail safety in your complete firm
2. Forcepoint

Price: You should contact them for a quote
Forcepoint’s DLP Security solution focuses on unified insurance policies, automation, and consumer danger administration. Specifically, you get:
- Visibility and management over human-centric processes to cut back the danger of unintended leaks
- Advanced analytics and user-risk scoring, which helps you deal with vital incidents
- Extendable information leak prevention insurance policies and analytics for vital cloud functions similar to AWS or Azure providers.
3. Proofpoint

Price: You should contact them for a quote
Proofpoint Email DLP detects confidential data and delicate information in outbound worker emails. In essence, it precisely detects information transmission and stops vital information from leaking outdoors your agency by electronic mail.
With this software program, you possibly can:
- Use information matching know-how to determine information specific to your group
- Detect delicate information precisely inside pictures, movies, and different unstructured content material
- Find, monitor, and safe information in emails, endpoints, cloud functions, and on-premises file shares
Those are three of the most effective software program you should utilize to stop a knowledge leak. Consider your organization’s wants when trying to decide on one. Now for a fast recap.
Final Words
A knowledge leak is intentional or unintended information publicity to unauthorized third events. The penalties of a knowledge leak are extreme similar to monetary loss, authorized issues, and lack of belief. Companies may additionally need to pay hefty fines in the event that they don’t adjust to information safety legal guidelines and laws. A well-planned cybersecurity strategy that features information safety applied sciences, procedures, and insurance policies is one of the best ways to stop information leaks.
I hope this text gave you some insights into the risks of knowledge leaks. Feel free to refer again to this text sooner or later.
Do you’ve got any extra questions on information leaks? Check out the FAQ and Resources sections under!
FAQ
What occurs if my information will get leaked?
Data leaks expose your information, similar to banking and monetary data and social safety numbers to 3rd events. Once criminals have these particulars, they will steal your identification and commit fraud in your title. For instance, they might take out loans that the financial institution expects you to repay, use your identification for unlawful entry into your nation, or immediately steal your financial savings. Such crimes depart you with low credit and authorized points which might be very troublesome to defend in opposition to.
Should I modify my password after a knowledge leak?
Yes. You ought to change your password instantly in case your agency fell sufferer to a knowledge leak. If you employ the identical password throughout completely different methods, all of them are actually at risk. Change your password throughout all methods as quickly as potential.
What is the distinction between a knowledge leak and a knowledge breach?
“Data leak” is a basic time period protecting all sorts of information publicity inside a agency. On the opposite hand, a “information breach” is a specific kind of knowledge leak that primarily refers to information loss as a result of exterior brokers. When cybercriminals assault your methods and entry your information, it’s thought of a knowledge breach. However, each phrases are sometimes used interchangeably.
What ought to corporations do after a knowledge leak?
The finest response for an organization affected by a knowledge leak is to conduct an in depth IT safety audit. To that finish, you’d interact an IT safety specialist. The specialist will independently assess the incident and put together a report of all of the data leaked. The specialist may also counsel options to stop future information leaks.
Who do you report a knowledge leak to?
Regulations in most nations require that you just report all information leak incidents to the related information safety authority in your nation. For instance, within the USA, you report information leaks to the Federal Trade Commission, and within the UK to the Information Commissioner’s Office. Across the globe, in Australia, it is best to report the incident to the Australian Information Commissioner.
Resources
TechGenix: Newsletters
Subscribe to our newsletters for extra high quality content material.
TechGenix: Article on Data Leak Prevention
Read extra about preventing data leaks in the cloud.
TechGenix: Article on Data Leaks and Mercedes-Benz
Learn extra about data leaks in Mercedes-Benz.
TechGenix: Article on Protecting and Preserving Confidentiality
Learn about how one can preserve confidentiality and prevent a data leak.
TechGenix: Article on Application Data Leaks
Read about how applications leak private data to the Internet.
https://techgenix.com/data-leak-guide/

:max_bytes(150000):strip_icc()/registration-3938434_1280-e2aa7e5d57264ae19b69027f14c85c2f.jpg)




