Please donate to assist defray the price of trial transcripts. As most of you understand, I now stay in Ireland. I had thought of touring to DC to cowl the Sussmann trial however have points I want to cope with right here. So I’m hoping to cowl as a lot of it as I can (with an apparent delay) by way of trial transcripts. But they’re costly! So for those who admire this protection, please think about a one-time or recurring donation to defray the price of transcripts. Thanks!
When Michael Sussmann legal professional Sean Berkowitz was strolling FBI Agent Scott Hellman by way of the six conferences he had with Durham’s workforce on Tuesday — conferences he first had as a witness in regards to the investigation into the Alfa Bank allegations and later in preparation for his trial testimony — Berkowitz requested Hellman about how, someday earlier this 12 months, Andrew DeFilippis and Jonathan Algor requested him whether or not he might function their DNS skilled for the trial.
Q And then, extra lately, you met with Mr. DeFilippis and I believe Johnny Algor, who can be on the desk right here, who’s an Assistant U.S. Attorney. Correct?
A. Yes.
Q. They needed to speak to you about whether or not you may have the option to act as an skilled on this case about DNS information?
A. Correct.
To Hellman’s credit score, he informed Durham’s prosecutors — who’ve been investigating issues pertaining to DNS information for 2 years — that he solely had superficial information of DNS and so wasn’t certified to be their skilled.
Q. You mentioned, whilst you had some superficial information, you didn’t essentially really feel certified to be an skilled on this case, right, on DNS information?
A. On DNS information, that’s right.
It wasn’t till the third day of trial earlier than Durham’s workforce introduced any proof in regards to the alleged crime. Instead, Durham’s first two witnesses had been their nominal skilled, David Martin, and Hellman, who informed Durham he wasn’t an skilled however who supplied opinions he neither had the experience to provide nor had achieved the work to substantiate.
That’s essential, as a result of DeFilippis used him to present an opinion solely an skilled ought to give. And just about every part about his testimony — his declare to have relied on the information within the supplies with out trying on the thumb drives, an apparently made up declare in regards to the timing of the evaluation, and behaviors that the FBI usually finds suspicious — recommend he’s not solely not a DNS skilled certified to assess this report, however his evaluation of the white paper Sussmann shared additionally suffers from severe credibility points.
The battle over an skilled
The testimony of the nominal skilled, David Martin, was remarkably nondescript, notably given the battle that led up to his testimony. Durham’s workforce sprung even having an skilled on Sussmann at a very late date: on March 30, after months of blowing off Sussmann’s inquiries if they might. Not solely did they need Martin to clarify to the jury what DNS and Tor are, Durham’s workforce defined, however in addition they needed him to weigh in on the validity of conclusions drawn by researchers who had discovered the anomaly.
- the authenticity vel non of the purported information supporting the allegations supplied to the FBI and Agency-2;
- the chance that such purported information was fabricated, altered, manipulated, spoofed, or deliberately generated for the aim of creating the false look of communications;
- whether or not the DNS information that the defendant supplied to the FBI and Agency-2 helps the conclusion {that a} secret communications channel existed between and/or among the many Trump Organization, Alfa Bank, and/or Spectrum Health;
[snip]
- the validity and plausibility of the opposite assertions and conclusions set forth within the varied white papers that the defendant supplied to the FBI and Agency-2;
As Sussmann famous in his motion to restrict Martin’s testimony, he didn’t thoughts the testimony about DNS and Tor. He simply didn’t need this trial to be in regards to the accuracy of the information, particularly with out the lead time to put together his personal skilled.
As the Government has already disclosed to the protection, ought to the protection try to elicit testimony surrounding the accuracy and/or reliability of the information that the defendant supplied to the FBI and Agency-2, Special Agent Martin would clarify the next:
- That whereas he can’t decide with certainty whether or not the information at challenge was cherry-picked, manipulated, spoofed or genuine, the information was essentially incomplete as a result of it was a subset of all international DNS information;
- That the purported information supplied by the defendant nonetheless didn’t assist the conclusions set forth within the main white paper which the defendant supplied to the FBI;
- That quite a few statements within the white paper had been inaccurate and/or overstated; and
- That people conversant in these related topic areas, resembling DNS information and TOR, would know that such statements lacked assist and had been inaccurate and/or overstated.
Based off repeated assurances from Durham that they weren’t going to make accuracy a difficulty of their case in chief, Judge Cooper ruled that the federal government might solely get into accuracy questions if Sussmann tried to increase the accuracy of the information himself. But if he mentioned he relied on the assurances of Rodney Joffe, it wouldn’t are available in.
The authorities means that Special Agent Martin’s testimony might go additional, relying on what theories Sussmann pursues in cross-examination or his protection case. Consistent with its findings above, the Court will enable the federal government’s skilled to testify in regards to the accuracy (or lack thereof) of the precise information supplied to the FBI right here solely in sure restricted circumstances. In specific, if Sussmann seeks to set up at trial that the information had been correct, and that there was actually a communications channel between Alfa Bank and the Trump Campaign, skilled testimony explaining why this might not be the case will change into related. But, because the Court famous above, extra testimony in regards to the accuracy of the information—skilled or in any other case—is not going to be admissible simply because Mr. Sussmann presents proof that he “relied on Tech Executive-1’s conclusions” in regards to the information, or “lacked a motive to conceal details about his purchasers.” Gov’s Expert Opp’n at 11. As the Court has already defined, complicated, technical explanations in regards to the information are solely marginally probative of these protection theories. The Court is not going to danger complicated the jury and losing time on a largely irrelevant or tangential challenge. See United States v. Libby, 467 F. Supp. second 1, 15 (D.D.C. 2006) (excluding proof below Rule 403 the place “any doable minimal probative worth that will be derived . . . is way outweighed by the waste of time and diversion of the jury’s consideration away from the precise points”).
Then, days earlier than the trial, the problem got here up once more. Durham sent a letter on May 6 (ten days earlier than jury choice), elevating a bunch of new points they needed Martin to increase. Sussmann argued that Durham was attempting to develop the scope of what his skilled might current. Among his complaints, Sussmann argued that Durham was attempting to make a materiality argument by way of his skilled witness.
Third, the Special Counsel apparently intends to provide skilled testimony in regards to the materiality of the false assertion alleged on this case. Indeed, the Special Counsel’s supplemental matter 9 concerning the significance of contemplating the gathering supply of DNS information is plainly being supplied to show materiality. But the Special Counsel didn’t disclose this matter in both his preliminary skilled disclosure or Opposition, and the Court’s ruling didn’t allow such testimony. The Special Counsel mustn’t now be allowed to provide a wholly new skilled opinion below the guise of eliciting testimony concerning the kinds of conclusions that may be drawn from a evaluate of DNS information.
Judge Cooper thought of the problem Tuesday morning, earlier than opening arguments. When asking why Martin had to current the idea of visibility, DeFilippis defined that Hellman–the Agent who’s not an skilled on DNS however whom DeFilippis nonetheless had requested to function an skilled on DNS–would speak in regards to the import of understanding visibility to assess information.
THE COURT: Well, however isn’t the query right here whether or not a case agent — is your case agent later going to testify that that was one thing that the FBI checked out or needed to have a look at on this case and was unable to accomplish that, and that that negatively affected the FBI’s investigation ultimately? MR.
DeFILIPPIS: Yes, and I anticipate Special Agent Hellman, who will testify probably in the present day, Your Honor, I anticipate that that could be a idea that he’ll say was related to the willpower that — determinations he was making as he drafted evaluation of the information that got here in. And, once more, I don’t suppose we — for instance, one other method by which this comes up is that the FBI routinely receives DNS information from varied personal firms who gather that information, and it’s at all times related kind of the breadth of visibility that these firms have. So it’s related usually, but in addition on this specific case the truth that the FBI didn’t have perception into the visibility or lack of visibility of that information actually affected steps that the FBI took.
THE COURT: Okay. But Mr. Sussman has not been accused of misrepresenting who the supply is. He’s merely — however relatively who the consumer is. So how do you hyperlink that to the materiality of the alleged false assertion?
MR. DeFILIPPIS: Because, Your Honor, I believe we view them as intertwined. It was as a result of — it was partly as a result of Mr. Sussman mentioned he didn’t have a consumer that made it harder for the FBI to get to the underside of the supply of this information or made it much less probably they might, and so — and, once more, I don’t suppose we anticipate to dwell for a very long time on this, however I believe the brokers and the technical people will say that that’s half of why the origins of the information are extraordinarily related after they took investigative steps right here.
When Cooper famous Sussmann’s objection to Martin discussing doable spoofing of information, DeFilippis once more answered not about what Martin would testify, however what Hellman would.
As DeFilippis defined, he claimed to consider that below Cooper’s ruling, the federal government might put in any little factor they needed that they claimed had been half of the investigation.
And Special Agent Hellman, when he testifies in the present day — now, Your Honor’s ruling we perceive to allow us to put into proof something about what the FBI analyzed and concluded as its investigation unfolded as a result of that goes to the materiality of the defendant’s assertion. So Special Agent Hellman — by way of Agent Hellman we are going to provide into proof a paper he ready when the information first got here in, and amongst its conclusions is that the information may — he doesn’t use the phrase “spoof” — however may need been deliberately generated and may need been fabricated. That was the FBI’s preliminary conclusion in what it wrote up.
So to ensure that the jury to perceive the course of the FBI’s investigation and the conclusions that it drew at every stage, these ideas are on the heart of it.
[snip]
MR. DeFILIPPIS: Okay. Your Honor, I’m sorry. We understood your ruling to be that the FBI’s conclusions because it went alongside had been okay so long as we weren’t asserting the conclusion that it was, actually, fabricated. You know, I imply, it’s troublesome to chart the course of the FBI’s investigation except we are able to elicit at every stage what it’s that the FBI concluded.
Judge Cooper ordered that references to spoofing be eliminated — main to a final minute redaction of an exhibit — however permitted a dialogue of visibility to are available in.
After all that battle, Martin’s testimony was not solely bland, but it surely was recycled powerpoint. He not solely admitted lifting the EFF description of Tor for his PowerPoint, however he included their emblem.
Hellman delivers the non-expert skilled opinion Durham was prohibited from giving
As I mentioned, Martin was witness primary, Hellmann — the self-described non-expert in DNS — was witness quantity two.
Even although Hellman admitted, once more, that he’s not a DNS skilled, DeFilippis nonetheless had him go over what DNS is.
Q. How acquainted or unfamiliar are you with what is called DNS or Domain Name System information?
A. I do know the fundamentals about DNS.
Q. And in your understanding, on a really fundamental stage, what’s DNS?
A. DNS is mainly how one pc would try to talk with one other pc.
After getting Hellman to clarify how he purportedly received chain of custody signatures on September 20, 2016 for the supplies Michael Sussmann dropped off with James Baker on September 19, DeFilippis walked Hellman by way of how, he claimed, he had concluded that the allegations Sussmann dropped off had been unsupported. Hellman reviewed the information accompanying the white paper, Durham’s star cybersecurity witness claimed on the stand, and after reviewing that information, decided there was no allegation of a hack within the supplies and due to this fact nothing for the Cyber Division to have a look at. And, as a report he wrote “inside a day” summarized, he concluded the methodology was horrible.
As you learn the next trade, know that (as I perceive it) some, if not most, of what Hellman describes the methodology to be is unsuitable. Obviously, if Hellman’s understanding of the methodology is unsuitable, then the opinion that DeFilippis elicits from a man who admitted he was not an skilled on DNS however whom DeFilippis nonetheless requested to function his skilled witness on DNS earlier than inviting David Martin in to current slides lifted from the Electronic Frontier Foundation as an alternative [Takes a breath] … If Hellman’s understanding of the methodology and the information he’s taking a look at is unsuitable, then his opinion in regards to the methodology goes to be of little advantage.
With that understanding, word the objection of Sean Berkowitz, who fought DeFilippis’ late hour addition of an skilled that DeFilippis needed to use to opine on the validity of the analysis, bolded beneath.
So we seemed on the prime half, which set out your top-line conclusion. You then have a portion of the paper that claims, “The investigators who performed the analysis seem to have achieved the next.” Now, Special Agent Hellman, it seems to be a reasonably technical dialogue, however are you able to simply inform us, in that first half of the paper, what did you set out and what did you conclude?
A. It seems to be to be that they had been in search of domains related to Trump, and the way in which that they did that was they checked out an inventory of kind of all domains and seemed for domains that had the phrase “Trump” in them as a method to slender down the quantity of domains they had been taking a look at.
And then they needed to discover, nicely, which of that preliminary set of Trump domains, which of them are e mail servers related to these domains. And the way in which they did that was to seek for phrases related to e mail, like “mail” or different email-related phrases to then slender down their record of domains even additional to be Trump-associated domains that had been e mail servers.
Q. And did you opine on the soundness of that methodology? In different phrases, did you categorical a view as to whether or not this was a great way to go about this mission?
A. We didn’t — I didn’t really feel that that was probably the most expeditious method to go about figuring out e mail servers related to the area.
Q. And why was that?
A. You can title an e mail server something you need. It doesn’t have to have the phrases “mail” or “SMTP” in it. And so by — for those who’re simply trying to find these phrases, I might wager to guess you’ll miss an precise e mail server as a result of there are different — there are different extra technical ways in which you need to use — mainly look-up instruments, Internet look-up instruments the place you’ll be able to say, for any area, inform me the related e mail server. That’s basically like a registered e mail server. But the way in which that they had been doing it was they had been simply in search of key phrases, and I believe that it simply didn’t make sense to me why they might go about figuring out e mail servers that method as opposed to simply having the ability to look them up.
Q. Was there anything in regards to the methodology used right here by the author or writers of this paper that you simply discovered questionable or that you simply didn’t agree with?
A. I believe simply the general assumptions that had been being made about that the server itself was really speaking in any respect. That was in all probability one of the most important ones.
Q. And what, if something, did you conclude about whether or not you believed the authors of the paper or creator of the paper was pretty and neutrally conducting an evaluation? Did you could have an opinion both method?
MR. BERKOWITZ: Objection, Your Honor.
THE COURT: Basis?
MR. BERKOWITZ: Objection on basis. He requested him his opinion. He’s not certified as an skilled for that.
THE COURT: I’ll overrule it.
A. Sorry, are you able to please repeat the query?
Q. Sure. Did you draw a conclusion somehow as to whether or not the authors of this paper appeared to be making use of a sound methodology or whether or not, to the opposite, they had been attempting to attain a selected consequence? Did you —
A. Based upon the conclusions they drew and the assumptions that they made, I didn’t really feel like they had been goal within the conclusions that they got here to.
Q. And any specific causes or assist for that?
A. Just the idea you’ll have to make was thus far reaching, it didn’t — it simply didn’t make any sense.
That’s how, as his second witness, Andrew DeFilippis launched the opinion of a man who admitted he wasn’t an skilled on DNS that DeFilippis had requested to function an skilled regardless that DeFilippis ought to have recognized that he didn’t have the experience to provide skilled opinions like this.
If Sussmann is discovered responsible, I might guess an awesome deal of cash this stunt will likely be one half of a a number of pronged attraction, as a result of Judge Cooper permitted DeFilippis to do exactly what Cooper had prohibited him from doing earlier than trial, and he let him do it with a man who by his personal admission isn’t a DNS skilled.
Cyber Division reaches a conclusion with out trying on the thumb drives
Now let’s have a look at what Hellman describes his personal methodology to be.
First, it was fast. DeFilippis appears to suppose that serves his narrative, as if these items was so crappy that it took a mere glimpse to discredit it.
Q. Special Agent Hellman, how lengthy would you say it took you and Special Agent Batty to write this up?
A. Inside of a day.
Q. Inside of a day, you mentioned?
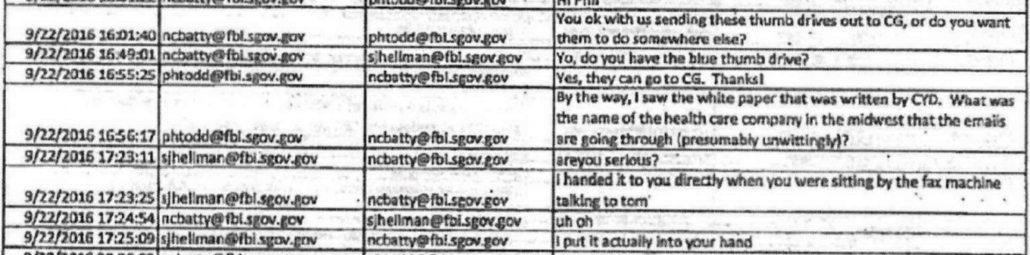
Berkowitz walked Hellman by way of the timeline of it, and boy was it fast. There’s some uncertainty about this timeline, as a result of John Durham’s workplace doesn’t really feel the necessity to clarify whether or not reveals they’re turning over in discovery mirror UTC or ET. But I believe I’ve laid it out beneath (Berkowitz received it unsuitable in cross-examination, which DeFilippis used to assault his evaluation).
As you’ll be able to see, not solely had been FBI’s crack cybersecurity brokers making a last conclusion in regards to the information inside a day however — by all appearances — they did so earlier than that they had ever seemed on the thumb drives included with the white papers. From the file, it’s really not clear when — if!!! — they seemed on the thumb drives. But it’s sure that they had their evaluation finalized no a couple of working day after they admitted they hadn’t seemed on the thumb drive, which was itself after that they had already determined the white paper was shit.
Timeline
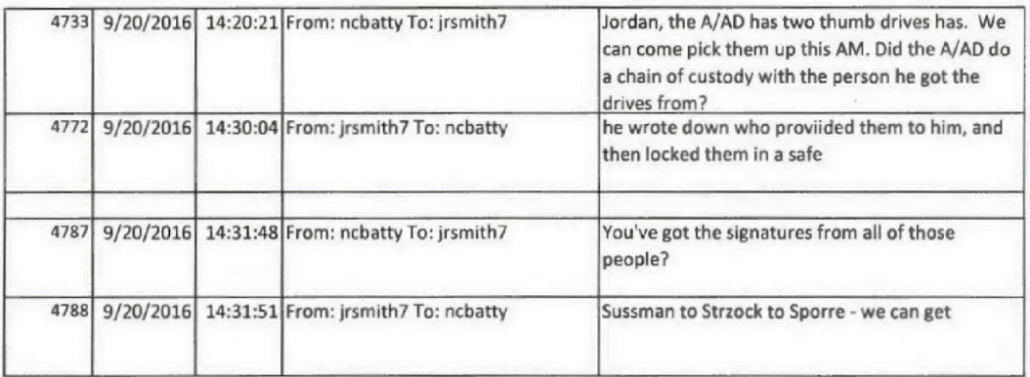
September 20, 10:20PM: Nate Batty tells Jordan Kelly they’ll come from Chantilly to DC get the thumb drives
September 20, 10:31PM: Jordan Kelly tells Batty the chain of custody is “Sussman to Strzock to Sporre”
September 20, 12:29PM: Hellman and Nate Batty settle for custody of the thumb drives
September 20, 1:30PM: Hour drive again to Chantilly, VA
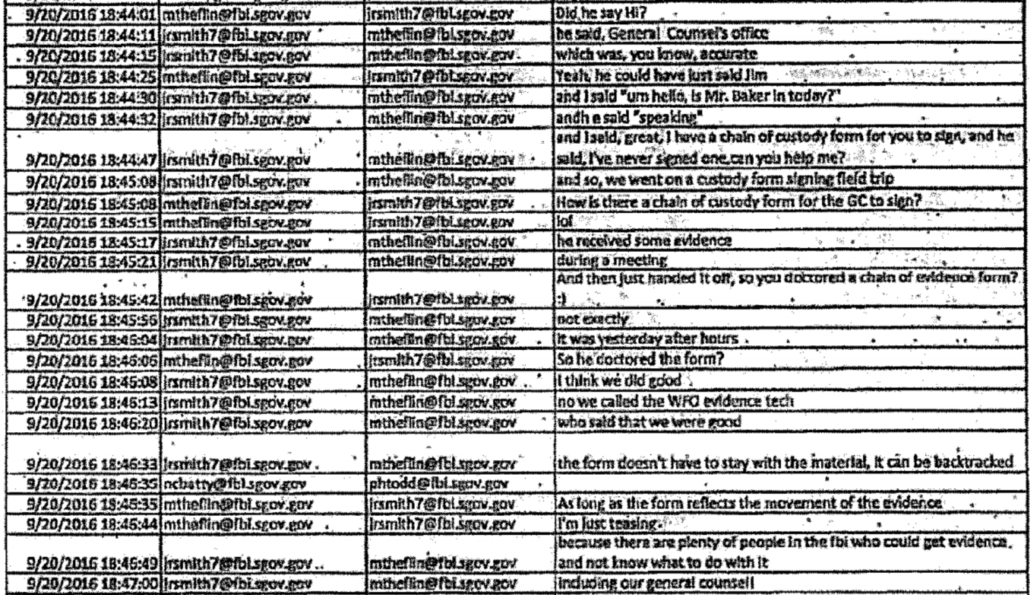
September 20, 4:44PM: Hellman seems to clarify the method of choosing up the thumb drives to jrsmith, claiming to have spoken to Baker on the cellphone. jrsmith jokes about “physician[ing] a series of proof kind.”
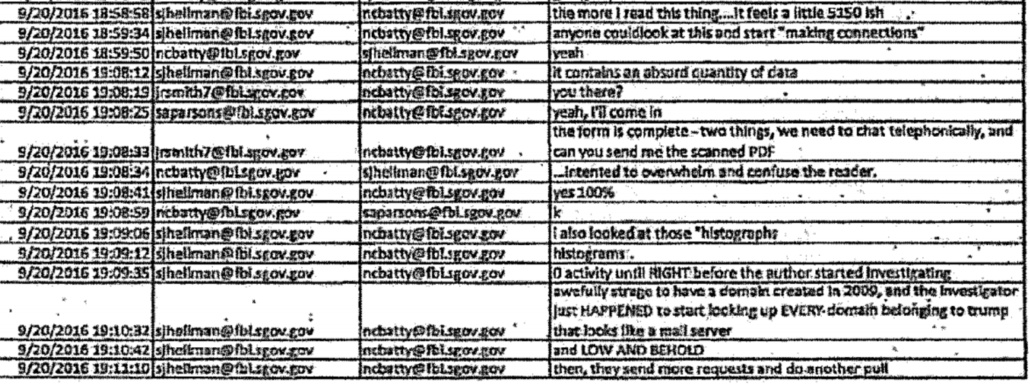
September 20, 4:58: Hellman says the extra he reads the report “it feels just a little 5150ish,” suggesting (as he defined to Berkowitz on cross) the authors suffered from a psychological incapacity, and Batty responds complains that “it incorporates an absurd amount of information … inserted to overwhelm and confuse the reader.”
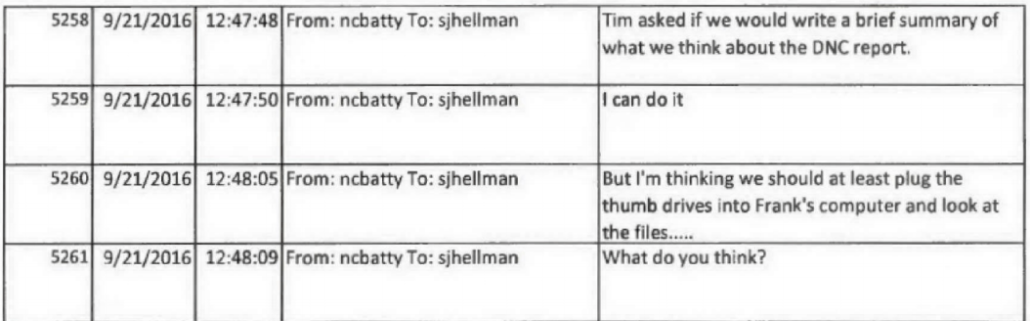
September 21, 8:47AM: Batty tells Hellman their supervisor needs them to “write a quick abstract of what we take into consideration the DNC report.” Batty continues by suggesting that “we should always no less than plug the thumb drives into Frank’s pc and have a look at the information…”
9/22, 9:44AM: Curtis Heide, in Chicago, asks Batty to ship the contents of the thumb drive so counterintelligence brokers can start to have a look at the proof. The boys in Cyber wrestle to accomplish that for a bit.
9/22, 2:49PM: Batty asks Hellman what he did with the blue thumb drive.
9/22, 4:46PM: Batty sends “evaluation of Trump white paper” to others.
In different phrases, the cyber division spent lower than 24 hours doing this evaluation.
Yes. The evaluation was fast.
Hellman says his evaluation is legitimate as a result of he seemed on the information
The hastiness of the evaluation and the truth that Hellman didn’t have a look at the thumb drive earlier than making preliminary conclusions in regards to the analysis is pretty problematic, as a result of when he mentioned his personal methodology, he described the information driving every part.
Q. Now, what principally, from the supplies, did you depend on to do your evaluation?
A. So it was actually two issues. It was trying on the information, the technical information itself. There was a abstract that it got here with. And then additionally we had been evaluating what we noticed within the information, kind of the story that the information informed us, after which trying on the narrative that it got here with and evaluating our evaluation of the information to the narrative.
[snip]
Q. And in reference to that evaluation, did you additionally check out the information itself that was underlying this paper?
A. Yes
[snip]
Q. And if we have a look at that first web page there, Agent Hellman, what sort of information is that this?
A. It seems to be — so far as I can inform, it seems to be to be — it’s log information. So it’s a log that exhibits a date and a time, a site, and an IP deal with. And, I imply, that’s — simply taking a look at this log, there’s not an excessive amount of extra from that.
Q. And do you perceive this to be no less than an element of the DNS information that was contained on the thumb drives that I believe you testified about earlier?
A. Yes.
[snip]
A. It would have mattered — nicely, I believe on one hand it could not have mattered from the technical standpoint. If I’m taking a look at technical information, the information’s going to inform me no matter story the information’s going to inform me unbiased of the place it comes from. So I nonetheless would have achieved the identical technical evaluation.
But understanding the place the information comes from helps to inform me — it offers me context concerning how a lot I consider within the information, how genuine it’s, do I consider it’s actual, and do I belief it. [my emphasis]
He repeated this declare on cross with Berkowitz.
I simply disagreed with the conclusions they got here to and the evaluation that they did primarily based upon the information that got here together with the white paper.
When Berkowitz requested him why counterintelligence opened an investigation when Cyber didn’t, Hellman steered that the individuals in CD wouldn’t perceive how to learn the technical logs.
A. Um, I believe they’d in all probability be taking a look at it from the identical vantage level, however for those who’re not — you don’t have expertise taking a look at technical logs, it’s possible you’ll not have the potential of doing a evaluate of these logs. You may depend on any person else to do it. And maybe counterintelligence brokers are going to be eager about different investigative questions. So I assume it could in all probability be a mix of each.
“If I’m taking a look at technical information,” DeFilippis’ star cybersecurity agent defined, “the information’s going to inform me no matter story the information’s going to inform me.”
Except he didn’t have a look at the technical information, no less than not the information on the thumb drives, earlier than he reached his preliminary conclusion.
Hellman makes a declare unsupported by the information in his personal evaluation
I’ll go away it to individuals extra skilled than me to rip aside Hellman’s own analysis of the white paper Sussmann shared with the FBI. In early consultations, I’ve been informed he misunderstood the methodology, misunderstood how researchers used Trump’s different domains to show that only one had this anomaly (that’s, as a method to take a look at their speculation), and misstated the need of some long-term suggestions loop for this anomaly to be sustained. Again, the consultants will ultimately clarify the issues.
One half of his report that I do know damns his methodology, nonetheless, is the place he says the researchers,
Searched “…international nonpublic DNS exercise…” (unclear how this was achieved) and found there are (4) main IP addresses which have resolved to the title “mail1.trump-email.com”. Two of these belong to DNS servers at Russian Alfa Bank. [my emphasis]
This is the purpose the place each single individual I do know who assessed these allegations who’s no less than marginally skilled on DNS points stopped and mentioned, “international nonpublic DNS exercise? There are solely a handful of folks that could possibly be!” Everyone marginally skilled individual I do know has, upon studying one thing like that, tried to determine who would have that sort of visibility on the information, as a result of that sort of visibility, by itself, would converse to their experience. Those marginally skilled individuals didn’t have the means to establish the doable sources of the information. But loads of them — together with the NYTimes!! — had been ready to discover individuals who had that sort of visibility to higher perceive the anomaly. When Hellman learn that, he merely mentioned, “unclear how this was achieved” and moved on.
Still, Hellman didn’t contest (or probably even take a look at) the evaluation that mentioned there have been actually simply 4 IP addresses conducting look-ups with the Trump advertising server. Dozens of individuals have continued to take a look at that consequence within the years since, and whereas there have been changes to the final consequence, nobody has disproven that the anomaly was strongest between Alfa Bank and Trump’s advertising area.
Where Hellman’s insta-analysis actually goes off the rails, nonetheless, is in his assertion that, “it seems that the presumed suspicious exercise started roughly three weeks prior to the said begin date of the investigation performed by the researcher.”
I’m not a DNS skilled, however I’m fairly good at timelines, and by my learn listed below are the important thing dates within the white paper.
May 4, 2016: Beginning date for look-up evaluation
July 28, 2016: Lookup for hostnames yielding Trump
September 4, 2016: End date for look-up evaluation
September 14, 2016: Updated seek for look-ups protecting June 17 by way of September 14
The begin date mirrored on this white paper is July 28, 2016. Three weeks earlier than that will be July 7, 2016, a date that doesn’t seem within the white paper. The anomaly began 85 days earlier than the beginning date mirrored on this white paper (and the beginning date for the analysis started months earlier, however nonetheless over three weeks after the May 4 begin date).
I don’t perceive the place he received that declare. But DeFilippis repeated it on the stand, as if it had been mirrored within the information, I assume believing it makes his star cybersecurity agent look good.
DeFilippis’ star cybersecurity agent has some credibility issues
There are just a few extra issues with the credibility of Hellman, DeFilippis’ star cybersecurity agent who isn’t a DNS skilled. One of these is that he in contrast notes together with his boss earlier than first testifying.
Q: And you additionally spoke with Nate Batty round that point, Right?
A: Yes.
Q: Did you speak to him earlier than the primary interview to sort of prepare for it?
A: I believe so, however I don’t bear in mind.
Q: Is that one thing that you simply encourage witnesses to do, to speak to different witnesses to see in case your recollections are constant?
A: No.
In addition, however that Batty was informed that Sussmann was within the chain of management, Batty claimed to consider the supply was “nameless” and Hellmann claimed to consider it was delicate–a human supply. Even after evaluating notes their tales didn’t match.
There are different issues with Hellman’s reminiscence of the occasions, notably that in his first interview — the one he did shortly after evaluating notes with Batty — he claimed that Baker had informed him he was unable to establish the supply of the information.
Q. And while you went to Mr. Baker’s workplace, do you bear in mind what, if something, was mentioned throughout that dialogue or throughout that interplay?
A. I bear in mind being within the workplace, however I don’t distinctly recall what the dialog was. I do bear in mind after the very fact, although, that I used to be pissed off that I used to be not ready to establish who had supplied these thumb drives, this info to Mr. Baker. He was not keen to inform me.
At the very least, this presents a battle with Baker’s testimony, but it surely’s additionally one other testomony to how variable reminiscences may be 4 years, a lot much less six years, after the very fact.
Hellman additionally claimed, when requested on cross, that the primary time he had ever seen the reference to a “DNC report” in September 21 Lync notes he obtained was two years in the past, when he was first interviewed.
A: The first time I noticed this was two years in the past after I was being interviewed by Mr. DeFilippis, and I don’t recall ever seeing it. I by no means had any recollection of this info coming from DNC. I don’t bear in mind DNC being an element of something we learn or mentioned.
Q: Okay. When you say, the primary time you noticed it was two years in the past while you met with Mr. DeFilippis, that’s not correct. Right? You noticed it on September twenty first, 2016. Correct?
A: It’s in there. I don’t have any reminiscence of seeing it.
And when Sean Berkowitz requested about Hellman the importance of seeing the reference to a “DNC report” very first thing on September 21, he described that DeFilippis steered to him that it was probably only a typo for DNS.
Q. What’s your clarification for it?
A. I’ve no recollection of seeing that hyperlink message. And there may be — I’ve completely no perception that both me or Agent Batty knew the place that information was coming from, not to mention that it was coming from DNC. The solely clarification that popped or was mentioned was that it might have been a typo and any person was attempting to refer to DNS 12 as an alternative of DNC.
Q. So you suppose it was a typo?
A. I don’t know.
Q. When you mentioned the one one suggesting it — isn’t it true that it was Mr. DeFilippis that steered to you that it may need been a typo lately?
A. That’s right.
When requested a few matter for which there was documentary proof Hellman had seen in actual time that he claimed not to bear in mind, Andrew DeFilippis supplied up a proof that Hellman then supplied on the stand.
On the stand, DeFilippis additionally tried to get Hellman to name a advertising server a spam server, although Hellman resisted.
Once you look intently, I don’t suppose Hellman’s testimony helps Durham all that a lot. What it proves, nonetheless, is that DeFilippis tried to coach testimony.
One last factor. DeFilippis received his star cybersecurity agent to observe that the researchers didn’t embody their title or different markers on their report, as if that’s a measure of unreliablity.
Q. Now, let me ask you, had been you ready to decide from any of these supplies who had really drafted the paper alleging the key channel?
A. No.
Q. In different phrases, was it contained anyplace within the paperwork?
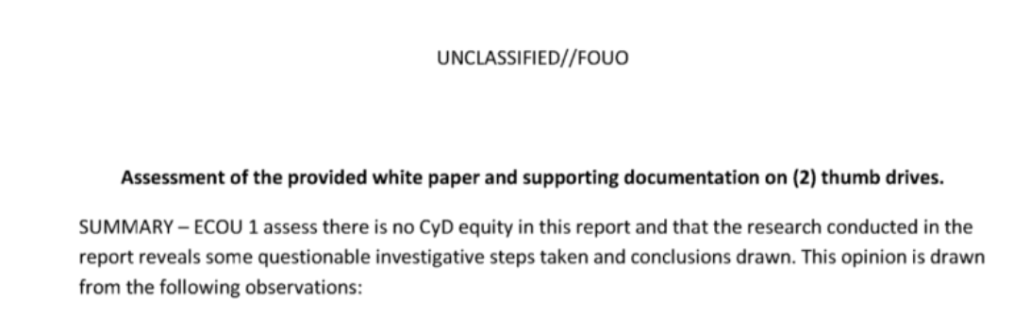
Here’s what Hellman’s personal report seems to be like:
There’s a unit — ECOU1 — however the names of the person brokers seem nowhere within the report. The report isn’t dated. It doesn’t particularly establish the white papers and thumb drives by management numbers, one thing key to evidentiary evaluation.
It has none of the markers of regularity you’d anticipate from the FBI. Hellman’s personal evaluation doesn’t meet the requirements that DeFilippis makes use of to measure reliability.
This long-time Grand Rapids resident is livid that Hellman judged there was no hack
Everything above I write as a journalist who has tried to perceive this story for nearly six years. Between that and 18 years of protecting nationwide safety instances, I hope I now have ample familiarity with it to know there are actual issues with Hellman’s evaluation.
But let me converse as somebody who lived in Grand Rapids for many of this era, and had buddies who had to cope with the aftermath of Spectrum Health showing on the heart of a politically contentious story.
Hellman had, as he testified, two jobs. First, he was supposed to decide whether or not there have been any cyber equities, then he was supposed to do some insta-analysis of the information with out first trying on the thumb drives.
According to Hellman, there was no hack.
I used to be requested to carry out two duties in tandem with Special Agent Batty, and our duties had been, primary, to have a look at this information, have a look at the information and have a look at the narrative that it got here with and establish had been there any what’s referred to as cyber equities. And by that it was, was there any allegation of a hacking. That’s what cyber division does. We examine hacking. So was there an allegation that any person or some firm or some pc had been hacked. That was first.
[snip]
As I discussed, the primary piece was we had to establish was there any actual allegation of hacking; and there was not. That was our first process by our supervisor. There was not.
[snip]
The allegation was that somebody purported to discover a secret communication channel between the Trump group and Russia. And so we recognized first that, no, we didn’t suppose that there was any cyber fairness, which means that there was in all probability nothing extra for cyber to examine additional, if there was no hacking crime.
Except right here’s what the white paper says about Spectrum, that Grand Rapids enterprise that was swept up on this story.
The Spectrum Health IP deal with is a TOR exit node used solely by Alfa Bank. ie., Alfa Bank communications enter a Tor node someplace on this planet and people communications exit, presumably untraceable, at Spectrum Health There is totally no cause why Spectrum would desire a Tor exit node on its system. (Indeed, Spectrum Health wouldn’t desire a TOR node on its system as a result of, by its nature, you by no means know what is going to come out of a TOR node, together with little one pornography and different authorized content material.)
We found that Spectrum Health is the sufferer of a community intrusion. Therefore, Spectrum Health might not realize it has a TOR exit node on its community. Alternatively, the DeVos household might have individuals at Spectrum who know there’s a TOR node. i.e., might have been positioned there with inside assist.
When confronted with some anomalous exercise that appeared to tie into the bizarre DNS site visitors, the consultants steered that possibly the Spectrum hack associated to the DNS anomaly.
To be clear, this Tor allegation is the the weakest half of this white paper. You will hear about this to no finish over the subsequent week. It was technically unsuitable.
But the allegation within the white paper is that possibly a current hack of Spectrum Health is why it had this anomalous site visitors with Trump’s advertising server. There’s your hack!!
Had the individuals at FBI’s cybersecurity facet really handled this as a doable compromise, it may need addressed the half of this story that by no means made any sense. And we’d not, now, six years later, be arguing about what may clarify it.
Let me be clear: I do suppose the white paper overstated its conclusions. I don’t suppose secret communication is the obvious clarification right here.
But there are hacks after which there are hacks within the testimony of DeFilippis’ star cybersecurity agent.
Update: Corrected an attribution to Batty as an alternative of Hellman.
https://www.emptywheel.web/2022/05/20/the-methodology-of-andrew-defilippis-elaborate-plot-to-break-judge-coopers-rules/






:max_bytes(150000):strip_icc()/HowtoSpecifyaPreferredSMTPServerforaMacOSXMailAccount2016-01-04-568a7f403df78ccc153b7b78.png)