Hornetsecurity 365 Total Protection Enterprise Backup is a cloud-based safety answer that gives safety in opposition to spam, malware, and different superior threats, mixed with backup and restoration options.
The answer is particularly designed for and absolutely built-in with Microsoft 365, providing e-mail and information safety to prospects. Its principal goal is to create a easy, safe, and hassle-free surroundings.
Installation
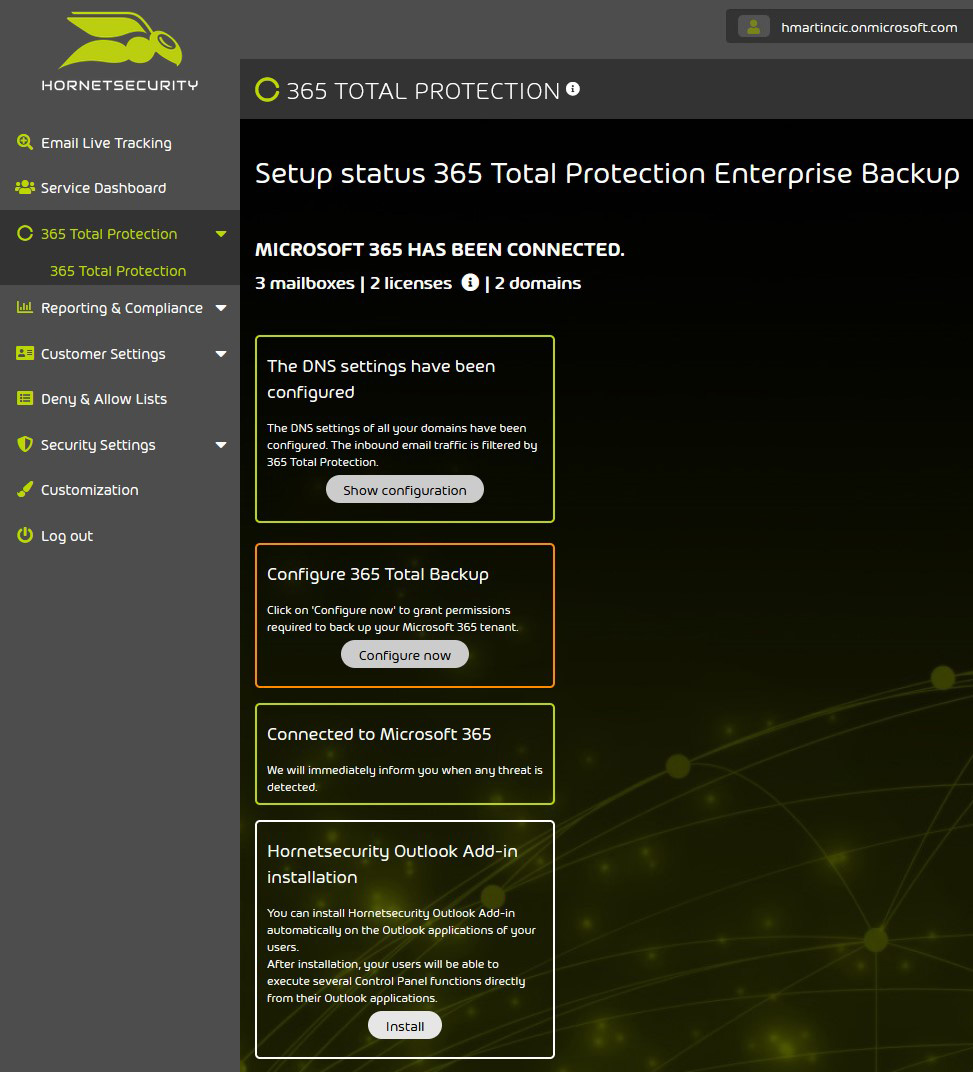
It all begins with the onboarding wizard, the place you, because the IT admin, should enter the first area in your tenants and your international admin credentials to entry the Microsoft tenants. The solely “handbook” a part of the method is the switch of the DNS report. The answer is activated when you end onboarding and swap the suitable MX information over to Hornetsecurity.
Figure 1 – Permissions required for the answer to work
Figure 2 – Options after ending the set up
Hornetsecurity Outlook Add-in
After ending the preliminary setup, you possibly can set up the Hornetsecurity Outlook Add-in in your customers’ Outlook purposes. The add-in can be utilized as a fast instrument for classifying info associated to “Allow” and “Deny” lists, by reporting messages to the Control Panel instantly. Additionally, it permits directors to overview “Allow” and “Deny” checklist entries created by every (consumer) account. Unfortunately, the archive interface (i.e., logging in to the Control Panel) from inside Outlook is simply obtainable on Windows Outlook shoppers – it isn’t supported on Mac or the Outlook internet interface.
Figure 3 – Users get notified of the add-in set up
Figure 4 – Add-in choices for a quarantine report delivered to a consumer
Security settings
This is the place all e-mail safety modules are listed and extra companies are activated. I’ll summarize the choices that may be fine-tuned.
Though I discovered the default settings appropriate, Spam and Malware Protection – the answer’s principal service – could be personalized. As admin, it’s possible you’ll need to lookup the obtainable choices underneath “User rights” and provides entry to (or restrict) the choices obtainable to your customers through the Outlook add-in.
Figures 5 and 6 – Spam and Malware Protection choices
Hornetsecurity recommends activating Advanced Threat Protection as a result of it’ll add a number of parts to assist fight the extra subtle assaults coming through e-mail:
- Real-Time Alert sends notifications to the personnel in cost if emails that have been obtained by customers of the area later turn into harmful.
- URL Rewriting will create “click on safety” for any hyperlinks inside emails, by changing them with customized hyperlinks that may redirect customers via the answer’s Web Filter. Any e-mail that went via this course of is clear. If it has a hyperlink that’s weaponized later and the consumer clicks on it, a rescan of the hyperlink is initiated and the consumer remains to be protected by the Web Filter.
- Targeted Fraud Forensics Filter blocks focused (personalised) malicious emails with out malware or hyperlinks.
Another possibility you would possibly need to swap on is the Quarantine Report, which could be activated for a complete buyer or for particular customers.
When Quarantine Report is configured for the shopper’s area, one in every of these two choices could be chosen: both the customers will obtain and may entry the quarantine stories supposed for them, or a quarantine report that incorporates quarantined emails of the entire area might be despatched to an e-mail tackle specified by the administrator.
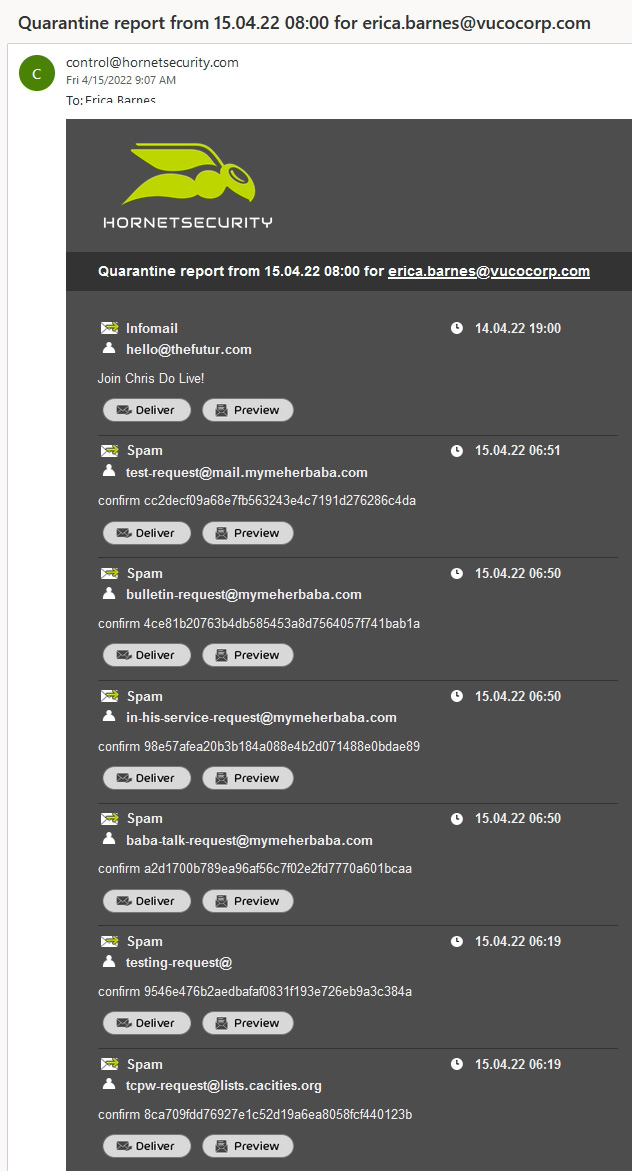
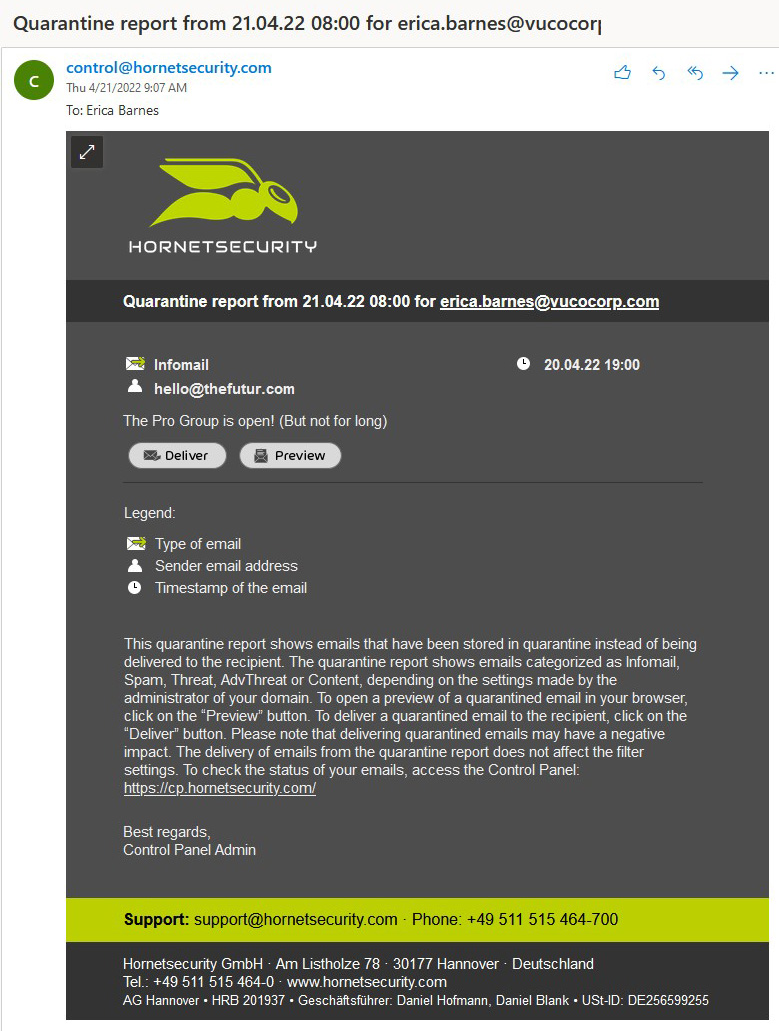
After quarantine standards is configured by the admin, quarantine stories might be created for probably malicious emails which were saved in quarantine as an alternative of being delivered to the recipient.
Depending on the settings made by admin, the quarantine report can present emails categorized as Infomail, Spam, Threat, AdvThreat or Content. Users can “launch” some classes of emails to themselves with out logging in to the Control Panel. Emails categorized as Spam and Infomail could be “launched” by the customers to their very own mailbox, whereas these falling into the Threat, AdvThreat or Content classes can’t, as a result of further admin overview is required for additional motion.
Figure 7 – IT admins’ selections for the Quarantine Report possibility
Figure 8 – A basic quarantine report delivered to a consumer
Figure 9 – A selected quarantine report delivered to a consumer
The Signature and Disclaimer function permits the admin to arrange e-mail signatures and disclaimers throughout the area for all customers. Different signatures and disclaimers could be arrange for varied inter-organizational teams (e.g., completely different departments, regional workplaces, and so forth).
New signature/disclaimer entries could be created through the embedded HTML editor and information could be pulled from Azure AD. Admins may embed banners, hyperlinks, pictures, social media icons, and so forth. Once a signature/ disclaimer entry is created, admins can preview the way it’s going to seem like earlier than making use of it to domains, customers or a selected group.
Figure 10 – A preview of a customized signature and disclaimer
Several strategies for Email Encryption are provided:
- TLS (Transport Layer Security) – Encrypts emails between the outgoing and incoming mail server (all the time activated)
- EmiG (E-Mail made in Germany) – A type of TLS encryption with necessities for the TÜV-certified communication companions, their server safety and the certificates used for encryption
- S/MIME – A typical for encrypting and signing MIME emails. The certificates authority (CA) assures the validity of the e-mail tackle and sender’s identify
- PGP (Pretty Good Privacy) – An uneven encryption customary utilizing private and non-private keys
- Websafe – Allows customers to ship encrypted emails to recipients who don’t help every other supported encryption strategies
Figure 11 – Email Encryption choices
Hornetsecurity says that, of their expertise, prospects primarily use the TLS and Websafe choices.
When utilizing Websafe, the emails are despatched to a portal (and saved there for 3 months). The recipients obtain an e-mail with credentials to entry the portal. Registration is accomplished after the recipients enter a PIN (delivered through telephone), a password and the reply to a safety query. Once created, the account is legitimate for all future emails obtained via the Websafe portal.
Depending in your most popular e-mail setup, further Email Authentication strategies (SPF, DKIM, DMARC) could be enabled:
Figure 12: Email Authentication choices
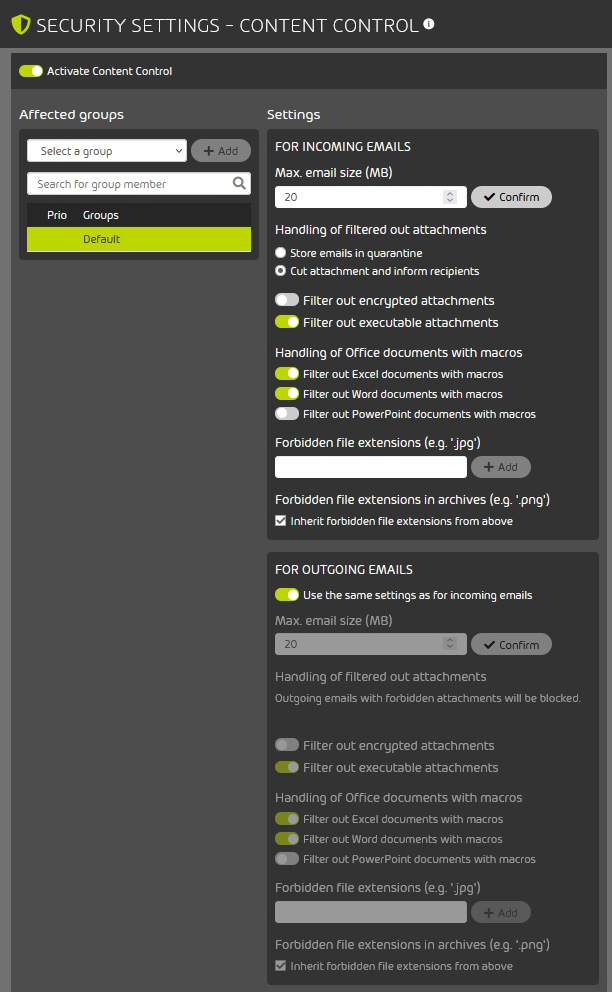
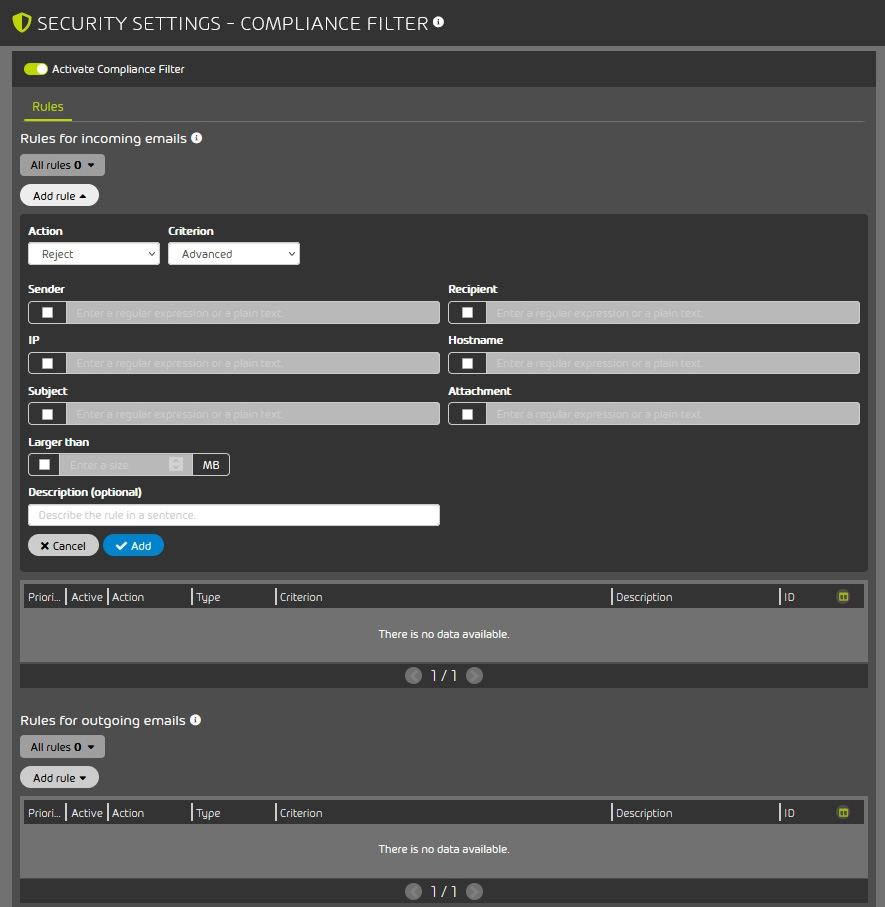
The Security Settings additionally embody choices for Content Control for incoming and outgoing emails. Admins can set e-mail dimension limits, filter out executable or encrypted attachments, Office paperwork with macros, and so forth.
Figure 13 – Content Control choices
Additional filtering guidelines could be created through the Compliance Filter to categorise incoming emails as Clean, Spam or Threat. Admins may make it in order that particular emails are rejected, redirected via a special server, or forwarded to different recipients.
Figure 14 – Compliance Filter choices
Archiving: After the service is activated, from that time on all obtained and despatched emails on the related area are archived for 10 years. The possibility could be deactivated for particular person domains, teams and/or customers. By including an exception, the archiving interval can be modified, or archiving solely deactivated.
Continuity Service permits customers to proceed to obtain and ship emails even when the e-mail server fails. This may turn out to be useful throughout catastrophe restoration.
Figure 15 – Continuity Service choices
Reporting and compliance
In this tab, admins can view and generate Email Statistics in line with specified standards, see a report of tried assaults throughout a specified timeframe through Threat Live Report, and monitor consumer actions within the Control Panel through Auditing 2.0.
Figure 16 – Threat Live Report
365 Total Backup
This answer gives backup and restoration for Microsoft 365 mailboxes, OneDrive accounts, SharePoint doc libraries, Teams chats, and Windows-based endpoints. Storage is offered and maintained by Hornetsecurity and is limitless in dimension with a “eternally” retention interval (i.e., till deleted by the consumer). Due to the doable delicate nature of the backed-up information, Hornetsecurity gives full GDPR compliance, with a further layer of safety: the info saved on the corporate’s servers is encrypted utilizing AES-256 encryption.
The following information is backed up:
- Mailbox: Emails, calendar entries, contact addresses
- OneDrive: All information saved within the consumer’s OneDrive for Business account
- Teams Chats: Teams chats for customers and teams inside your group, together with any information which are shared through the conversations
- SharePoint: Files and communication in SharePoint doc libraries, together with entry permissions
The Data Restore perform helps the next eventualities:
- Data could be restored to the unique mailbox/OneDrive account/SharePoint web site
- Data could be restored to a special mailbox/OneDrive account/SharePoint web site inside the similar or in a special group belonging to the identical buyer
- Data could be restored to a ZIP archive, which may then be downloaded
- Data could be restored as a PST file (this feature is obtainable just for mailboxes)
- Microsoft 365 Teams chats could be restored to a brand new staff inside Microsoft Teams or restored to HTML information, which may then be downloaded
- By utilizing Granular Restore, the admin can choose particular parts inside a selected backup snapshot to be restored or downloaded (a obtain hyperlink to the password-protected restored content material might be despatched through e-mail).
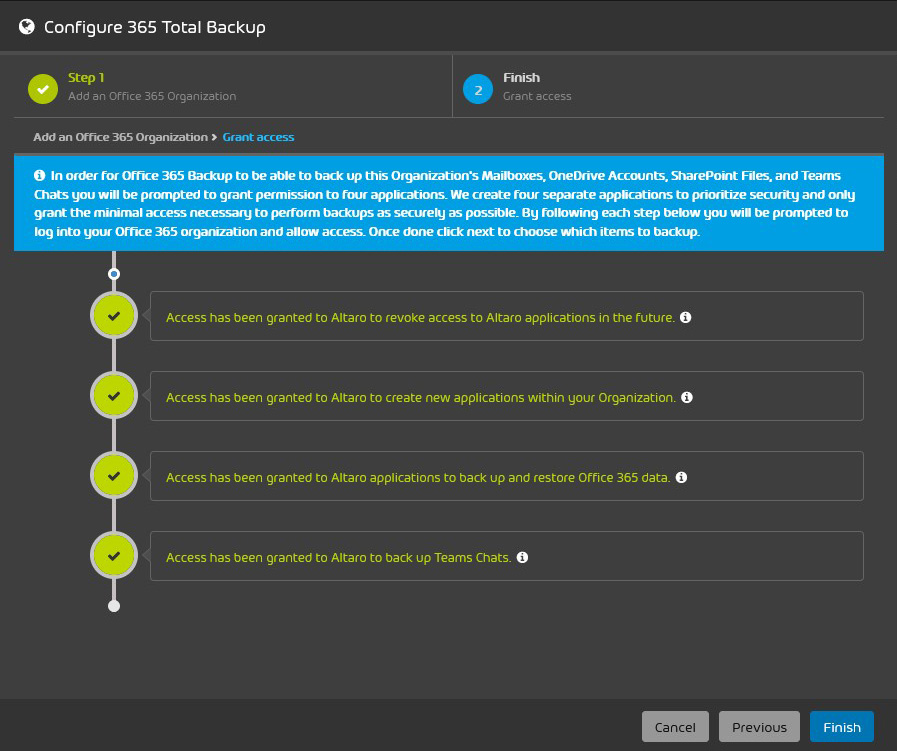
In my check, the activation of 365 Total Backup went with out a hitch. The info it’s essential to present is minimal and it’s essential to grant entry and permissions to Altaro Office 365 Backup (Hornetsecurity acquired Altaro, an organization that specialises in backup and restoration software program, in 2021).
Figure 17 – The info required for configuring 365 Total Backup
Figure 18 – Granting permissions to Altaro purposes
After being introduced with a user-friendly dashboard, the invention of latest customers and mailboxes, teams and SharePoint doc libraries begins mechanically. It can be triggered through a button later.
Figure 19 – The 365 Total Backup dashboard
Figure 20 – Users and backups
Restore actions are performed via wizards or Granular Restore, enabling admins to revive a complete account or a single file from a backup snapshot.
Figure 21 – Granular Restore
Figure 22 – The choices for restoring mailboxes
During my testing, I haven’t had any points whereas backing up or restoring mailbox and OneDrive information – all of it went easily and rapidly. Of course, the restoration pace is determined by the dimensions of the dataset that must be restored. The obtain of the info wanted for backup integrity verification went as quick as my ISP allowed.
One very last thing to say is that Hornetsecurity 365 Total Protection Enterprise Backup consists of help for (Windows) endpoint backup.
The Endpoint Backup Manager should be put in on a Windows server. This EBM server doesn’t should be on the identical community because the workstations, however a connection between them is required.
After putting in the EBM, it may be linked to the Cloud Management Console, from which the admin can setup backup insurance policies and deploy the endpoint brokers to the workstations. The EBM is used to configure and coordinate the backups and set the storage configuration. The storage must be Azure Cloud Storage, provisioned and managed by an MSP or the shopper firm. This is completely different from 365 Total Backup, for which Hornetsecurity gives and manages the storage.
Verdict
In my opinion, Hornetsecurity 365 Total Protection gives a degree of e-mail, OneDrive and SharePoint safety that ought to be sufficient for many Microsoft 365 customers.
During my testing of the e-mail safety options I’ve encountered no false positives. Emails have been accurately categorized and consumer categorization from the e-mail shopper or quarantine report labored flawlessly. I liked the user-friendly interface and appreciated how easy it’s to deal with the answer.
Customers ought to assess for themselves whether or not they want a number of the further mail companies equivalent to Email Encryption or Continuity Service.
The Enterprise Backup aspect of the answer covers all enterprise backup wants for the commonest user-generated sort of information inside a Microsoft 365 surroundings. It delivers a easy answer that may be arrange in underneath quarter-hour (if you happen to already outlined organizational backup insurance policies).
If you might be working a Microsoft 365 surroundings and also you care about e-mail safety and backup, I can suggest this answer. It gives a centralized backup answer, provides further safety layers over Microsoft 365 companies, and gives worth for each customers and IT directors.
https://www.helpnetsecurity.com/2022/05/26/review-hornetsecurity-365-total-protection-enterprise-backup/


















:max_bytes(150000):strip_icc()/HowtoSpecifyaPreferredSMTPServerforaMacOSXMailAccount2016-01-04-568a7f403df78ccc153b7b78.png)
