If you’re like most companies, it’s is your foremost communication channel with clients. Here are some e mail server safety greatest practices you need to use straight away to assist create a safe e mail server on your group
Imagine you’re making ready for a hurricane that’s coming your manner (we Floridians are effectively acquainted with this process). You set up straps to assist make your roof safer. You pull all of your garden gear, furnishings, and different exterior gadgets into your storage or shed. You board your home windows and doorways and purchase a lot of meals and water in case you’re stranded with out energy. But in case you select to depart your own home’s exterior doorways open because the storm strikes in, you’ll be able to kiss your own home and all the pieces in it goodbye. Similarly, that is form of what it’s like when corporations don’t hassle implementing a safe e mail server.
Radicati estimates the overall variety of enterprise and client emails despatched and obtained per day will surpass 376 billion by the tip of 2025. If you ship emails however don’t have a safe e mail server, then it implies that any information transmitted by way of them is liable to compromise. (Data is the lifeblood of your online business — you’ll be able to’t threat your delicate data falling into the mistaken palms.)
But what does it imply to have a safe e mail server? Let’s cowl X e mail server safety greatest practices and remind you why implementing these measures is critical to defend your online business and clients.
Let’s hash it out.
What Is a Secure Email Server?
Much just like the phrase safe implies, having a safe e mail server implies that you’re defending your e mail area and information from unauthorized utilization. This means:
- Protecting your emails each when they’re in transit and sitting in your staff’ inboxes
- Preventing unauthorized customers from sending emails utilizing your group’s area
- Setting up e mail filters and antivirus safety in your servers
- Securing the community(s) your staff and different approved customers use to entry these e mail companies
- Ensuring that your e mail servers are bodily inaccessible to unauthorized events (in case you run your personal e mail server)
- Understanding what steps your online business e mail service supplier (Amazon WorkMail, Google Workspace, Rackspace, Microsoft Exchange, and many others.) takes to safe the server(s) that may host your group’s email-related information
But how will you obtain these outcomes? Let’s dive proper into what you got here to study…
10 Email Server Security Best Practices You Implement Now
The following e mail server safety greatest practices listing isn’t a whole or complete information. However, this listing supplies you with an amazing beginning place to assist make your e mail server safer.
1. Change All Default Configurations, Usernames and Passwords for Your Email Server
A giant mistake that organizations make just isn’t taking the time to change their servers’ default settings and configurations. This could also be as a result of they’re in a rush or, maybe, they don’t understand simply how dangerous it’s to use the default settings. Regardless of the rationale, make certain to take the additional step and alter these settings.
This consists of altering default login data as effectively. Account and password security are paramount in cybersecurity as an entire. If you utilize a default username and weak password combo to safe something, it’s the equal of getting the choice of utilizing a double deadbolt lock in your entrance door however opting to use a flimsy chain lock as a substitute. Sure, it supplies minimal safety, however an attacker solely wants to use a bit “brute force” (get it?) to bust their manner in and acquire entry to your own home.
Using the default credentials (username and password) that comes along with your server or software program is like this. It’s not safe and leaves your e mail server and its information liable to theft and different compromises.
2. Set Up Mail Transfer Agent Strict Transport Security (MTA-STS)
A mail switch agent strict transport safety is a verification verify of incoming emails. According to Google, “SMTP connections for e mail are safer when the sending server helps MTA-STS and the receiving server has an MTA-STS coverage in enforced mode.”
Uh, certain. Great. But what does this imply? Basically, that is saying in layman’s phrases that in case you have MTS-STS enabled in your group’s e mail server, it’ll solely allow emails to be obtained by way of safe, authenticated connections (utilizing TLS 1.2 or 1.3).
This helps defend your recipients towards receiving unauthenticated messages despatched by way of insecure connections (i.e., connections the place somebody might insert malware or modify information in transit, or what’s often called a man-in-the-middle [MitM] assault).
If the sender’s digital id can’t be authenticated or they didn’t have SSL/TLS enabled, then the message will get rejected.
3. Select Secure Email Protocols to Protect Your Communications in Transit
Setting up a safe MTA is just a part of the equation; you additionally want to take just a few further steps to assist make your server — and the inbound and outbound communications to/from it — safer.
Install an SSL/TLS Certificate on Your Server to Enable HTTPS
Did you understand that SSL/TLS additionally applies to e mail? That’s proper, you need to use SSL/TLS safety to safe the communication channel of your messages. This permits you to encrypt the communications that transpire between your e mail server and different e mail servers that it communicates with. This manner, nobody can intercept the communications in transit.
Every time one in every of your staff sends or receives an e mail from somebody, it creates a reference to that particular person’s e mail server. If that connection isn’t safe, it implies that anybody with the know-how can intercept that message in transit and steal or modify the information with out the 2 authentic events figuring out what occurred.
Of course, in case you’re utilizing an e mail signing certificates to encrypt your e mail information immediately (extra on that later), then this serves as an extra layer of safety on your communications.
Use Secure Ports for Your Inbound and Outbound Email Services
Traditionally, IMAP or POP3 are protocols which might be used for incoming emails (i.e., messages e mail shoppers seize out of your mail server). SMTP, alternatively, is used for outgoing emails. Be certain to set your companies under to the next safe TCP/IP ports for incoming out outgoing messages:
- Outbound — Secure port 465 or 587 (with STARTTLS enabled) for SMTPS
- Inbound — With SSL/TLS enabled, you need to use one of many following ports:
- Port 993 for IMAP (with SSL enabled)
- Port 995 for POP3 (with SSL enabled)
4. Embrace DMARC to Help Prevent Brand Domain Spoofing
Cybercriminals love taking part in costume up with corporations’ manufacturers and capitalizing on their reputations. It’s not unusual for dangerous guys to impersonate organizations as a manner to perform phishing scams. Check Point studies that the most impersonated brand of Q1 2022 was LinkedIn, which was concerned in additional than half (52%) of all phishing assaults they analyzed globally. In (*10*), Check Point stated that DHL held that title, and Microsoft prior to that was the reigning champion of the title that no firm needs.
Domain-based message authentication, reporting and conformance (DMARC) is an e mail protocol that helps to defend your area towards inauthentic utilization by unauthorized people. The Internet Engineering Task Force (IETF) introduced it into the fold as a manner to assist organizations defend their domains towards these fraudulent usages. DMARC builds upon two different authentication protocols to be sure that solely your approved customers are sending emails on behalf of your area:
- Sender policy framework (SPF): An SPF textual content is a report you connect to your area title system (DNS). This helps to validate messages which might be despatched by your area.
- DomainKeys identified mail (DKIM): This protocol attaches your digital signature to outbound e mail message headers. This permits you to use public key cryptography to assist show the authenticity and integrity of the emails that come out of your area.
But simply how well-liked is DMARC? Mimecast studies of their report The State of Email Security 2022 that just about 9 in 10 corporations (89%) are both utilizing DMARC or plan to accomplish that over the following 12 months. This is in accordance to their world survey of 1,400 IT and cybersecurity professionals from 12 nations.
Of course, you’ll be able to take DMARC a step additional and convey your group’s digital id to the following degree. You can do that by integrating model indicators for message identification (BIMI) and verified mark certificates (VMCs) in your group’s e mail digital id. Doing this may allow you to insert your group’s verified brand into your entire group’s outbound emails from reputable senders.
5. Keep Your Server Software and Firmware Current with Patches and Updates
Running an outdated or unpatched model of your server’s software program is a surefire recipe for catastrophe. Patches are a writer or developer’s manner to repair bugs and different points that depart your e mail servers weak. If you don’t apply these patches in a well timed method, you run the chance of cybercriminals exploiting these vulnerabilities to acquire entry to your e mail server(s) and information.
Something you’ll want to select is the way you need to implement updates. Do you need to deal with them manually? Do you need to discover the choice of automation? Each strategy has its professionals and cons, however the level is that you simply want to be sure that updates and patches don’t fall between the cracks and don’t end up going through one other Eternal Blue situation.
(Quick rationalization: Eternal Blue was a vulnerability in legacy Windows methods that Microsoft issued a patch for however organizations uncared for to roll out in a well timed method. The finish consequence was tons of of 1000’s of gadgets globally being contaminated by ransomware in an assault that impacted tons of of hundreds of thousands of individuals [if not more].)
6. Use Email Server Firewalls to Keep an Eye on Inbound & Outbound Traffic
Alright, we’re greater than half manner by way of our listing of safe e mail server greatest practices. Much like how community firewalls function, e mail server firewalls filter inbound and outbound site visitors primarily based on the principles in your e mail server. What this does is provide help to to preserve tabs on incoming and outgoing communications in your area to look out for any suspicious actions.
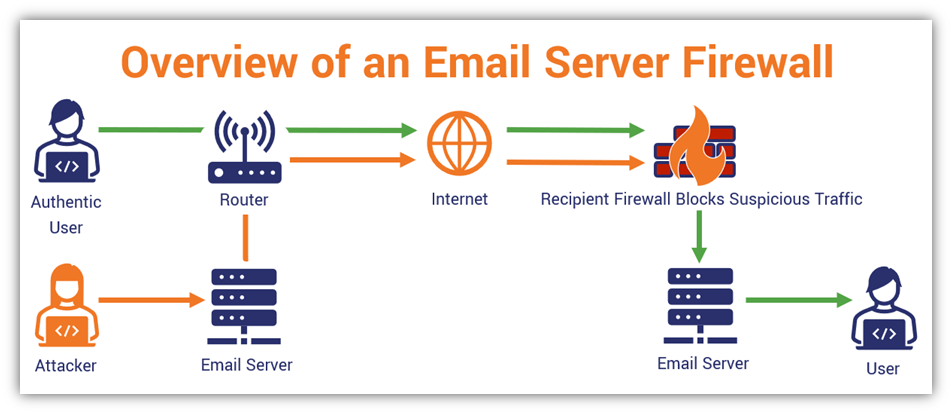
Of course, we will’t provide you with any particular instructions about organising guidelines in your e mail server since each system is totally different. So, you’ll want to refer to your particular firewall producer’s website for specifics on how to accomplish this objective.
Set Rate Limits and Size Restrictions on Outbound Traffic
While it’s essential to monitor your site visitors, you’ll additionally need to make certain to limit each the variety of emails that may originate out of your area in addition to their sizes. A spike in outbound messages might point out that a number of of your approved accounts could possibly be compromised and is getting used to ship spam or phishing messages. Setting price limits might help defend your area’s repute.
7. Be Selective in Who (or What) You Give Access to Your Mail Server
We’ve stated it earlier than and can proceed to say that not everybody wants entry to all the pieces. This is true concerning all the pieces from buyer and worker database data to privileged entry to your e mail servers. This is the place entry administration greatest practices come into play.
You can set worker profiles in order that customers have solely the minimal degree of entry they want to do their jobs. If somebody wants entry to a delicate system for a undertaking, assign them permission for the period of time mandatory to full it. Be certain to take away these privileges as soon as that entry is not mandatory (e.g., once they full the undertaking).
Furthermore, make certain to have a process in place that ensures entry is revoked for accounts when staff depart your group. Attackers and even disgruntled former staff love to use outdated logins to nostril round methods they need to not have entry to. You can stop this from occurring by deactivating their accounts straight away.
8. Use Secure Passwordless SSH Authentication as Admin to Manage Your Server
As an administrator, you doubtless use safe shell (SSH) to handle your group’s numerous servers. Traditionally, this requires utilizing a username and password mixture for authentication. But there’s a greater (and safer) manner of doing that than counting on probably weak login credentials: you need to use public-private key pairs as a substitute.
This methodology of authentication includes utilizing cryptographic keys to show your digital id as a reputable approved consumer. One of which is public and the opposite your gadget retains non-public that proves you’re you. This course of permits you to authenticate simply and securely with out ever having to keep in mind a cumbersome password.
We’ve talked at size concerning the significance of SSH key management best practices beforehand. To shortly recap, SSH key administration is about securing your cryptographic keys as a part of your SSH entry administration technique and safety practices. (Be certain to take a look at the article linked in the beginning of this paragraph for extra in-depth data.)
9. Teaching Users How to Keep Their Accounts Secure
Protecting account credentials isn’t non-obligatory; it’s the duty of each particular person worker and community consumer. Why? Because compromising customers’ accounts is the simplest manner for hackers to compromise your server. Part of this strategy to hardening your group’s cyber defenses includes educating and coaching customers on cyber safety greatest practices.
Some of the issues efficient cyber consciousness trainings ought to cowl embrace:
- How to acknowledge and keep away from social engineering and customary phishing threats (use real-world examples for this)
- What they need to do once they obtain suspicious emails or cellphone calls (present particular steerage and contacts)
- How to create safe passwords (which you’ll want to implement)
- How to use single signal on (SSO) and password administration instruments
- Why they shouldn’t set up shadow IT (unauthorized and probably malicious software program)
10. Require Your Authorized Users to Digitally Sign and/or Encrypt Their Emails
To assist stop your staff — particularly admins and different privileged consumer — from falling for credential phishing scams, require everybody to digitally signal their emails. By including a cryptographic digital signature (i.e., a signature that’s verified by a public CA) to your e mail, you’re doing two large issues:
- Offering an e mail recipient assurance that the sender is reputable, and
- Ensuring the message’s integrity hasn’t been compromised because it was signed.
You may use these certificates to encrypt emails containing delicate information for added measure. This course of requires each events (sender and recipient) to have e mail signing certificates, and for the e-mail sender to use the recipient’s public key. You then use their public key to encrypt the e-mail earlier than urgent Send and so they use their corresponding non-public key to decrypt the message on their finish.
If this sounds difficult, don’t fear — all you’ve got to do is ask the recipient to ship you a digitally signed e mail first. This manner, you’ve got a duplicate of their public key available. It’s that easy.
Final Thoughts on Why Having a Secure Email Server Is a Must for All Organizations
Frankly, there are numerous the explanation why implementing these e mail server safety greatest practices is essential for companies and different organizations globally. The greatest cause is that it’s the suitable and accountable factor to do. Your clients, customers and different stakeholders are entrusting you to defend their information.
Second, it helps to defend your curiosity by retaining your information safe from prying eyes. Cybercriminals and even your opponents would love to get their palms on the digital goodies you’ve got saved in your e mail server.
Here are just a few different fast the explanation why having a safe e mail server is crucial on your group:
- Keeps your information safe from unauthorized entry
- Prevents information breaches and compromise
- Avoids the model and reputational damages that may consequence from safety points
- Ensures compliance with information privateness and safety rules (GDPR, CCPA, PCI DSS, and many others.)
- Mitigates the chance of getting to face direct and oblique prices of getting an insecure e mail server (assume information breach mitigation, lawsuits, noncompliance penalties, and many others.)
https://www.thesslstore.com/weblog/10-email-server-security-best-practices-to-secure-your-email-server/

:quality(70)/cloudfront-us-east-1.images.arcpublishing.com/archetype/SCZ7KJP7ORB5RNLCL52RKINQPY.jpg)