Hackers are focusing on Microsoft email servers after a collection of vulnerabilities had been detailed at a pc security convention earlier this month.
Although software program updates for these vulnerabilities have been out there for months, greater than 50% of Microsoft Exchange servers within the UK haven’t been up to date, in accordance to security researchers.
Among the servers nonetheless vulnerable to assault are a number of on the British government’s gov.uk area in addition to the police.uk area utilized by forces in England, Wales and Northern Ireland.
Kevin Beaumont, a security researcher who previously labored for Microsoft, criticised the corporate for what he termed “knowingly terrible” messaging to get prospects to replace their software program.
The vulnerabilities are “as severe as they arrive”, wrote Mr Beaumont, as they permit hackers to remotely execute code on an email server with no need to enter a password.
Several security researchers and organisations have reported detecting cyber criminals hacking into servers by exploiting this vulnerability and then deploying ransomware.
Although the flawed code was mounted in April and May, Microsoft didn’t assign the issues a CVE identifier (Common Vulnerabilities and Exposures) till July, delaying the strategies many organisations use to observe and replace vulnerabilities.
“Given many organisations vulnerability handle by way of CVE, it created a state of affairs the place Microsoft’s prospects had been misinformed concerning the severity of probably the most important enterprise security bugs of the 12 months,” Mr Beaumont wrote.
A spokesperson for Microsoft stated: “We launched security updates to assist preserve our prospects protected and protected in opposition to this assault method.
“We advocate that prospects undertake a technique to guarantee they’re operating supported variations of software program and promptly set up security updates as quickly as attainable after every month-to-month security launch,” they added.
They stated they’d nothing to share in response to Mr Beaumont’s criticism about whether or not it had successfully communicated the significance of putting in these updates.
At the time that Microsoft issued a patch for the vulnerabilities there have been no publicly out there proof of idea exploits, which generally informs how extreme a danger any given vulnerability is taken into account to pose. It’s the distinction between understanding Superman has a weak spot, and truly possessing some Kryptonite.
The CVE identifier was assigned earlier than the difficulty was technically detailed on the Black Hat pc security convention by a hacker who makes use of the deal with Orange Tsai.
It was primarily based on these technical particulars that different hackers have been ready to develop exploits permitting them to recreate Orange Tsai’s strategies for accessing Exchange servers.
Orange Tsai stated they’d found extra vulnerabilities affecting Microsoft Exchange which had been “coming quickly” however didn’t reply to a Twitter message from Sky News for remark.
Mr Beaumont confirmed Sky News how he had recognized hundreds of unpatched Exchange Servers within the UK operating the Outlook Web App, together with a number of on the gov.uk area and two on the police.uk area.
The UK’s National Cyber Security Centre informed Sky News: “We are conscious of ongoing world exercise focusing on beforehand disclosed vulnerabilities in Microsoft Exchange servers.
“At this stage we’ve got not seen proof of UK organisations being compromised however we proceed to monitor for affect.”
“The NCSC urges all organisations to set up the newest security updates to defend themselves and to report any suspected compromises by way of our web site,” it added.
A spokesperson for security enterprise Mandiant informed Sky News they’d noticed “a variety of industries” being hacked.
“It is tough to attribute this exercise to anybody group of menace actors as a result of a number of examples of proof of idea exploit code have been developed and launched publicly by security researchers,” the spokesperson stated.
“This implies that any group may very well be leveraging the exploit and organisations who haven’t patched are vulnerable to assault,” they warned, including that patch charges “stay low” and urging corporations to apply patches as rapidly as attainable.
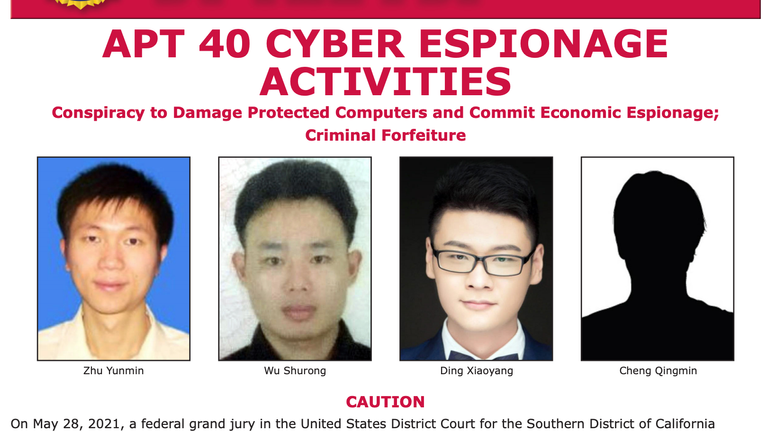
The new wave of assaults focusing on Microsoft Exchange servers follows Microsoft issuing a warning earlier this 12 months a couple of world hacking marketing campaign additionally focusing on these servers which it attributed to state-sponsored hackers based in China.
An estimated 400,000 servers worldwide had been “indiscriminately” compromised in the course of the espionage marketing campaign.
The British government slammed the “reckless” strategies utilized by China as the tactic its cyber spies had been utilizing to retain entry to sufferer servers additionally left these servers open to criminals.
While cyber espionage actors typically search to observe with out disrupting their goal networks, criminals will repeatedly disrupt the networks by deploying ransomware – making important recordsdata irretrievable except the victims pay an extortion charge.
Last month, the UK and allies accused China of “systematic cyber sabotage” in reference to that marketing campaign.
At the identical time, the contractors utilized by Beijing’s cyber intelligence equipment had been accused of conducting “unsanctioned cyber operations worldwide… for their very own private revenue” however it’s not clear whether or not these unsanctioned operations had been primarily based on exploiting the entry established by the sanctioned espionage marketing campaign.
https://information.sky.com/story/uk-government-and-police-servers-vulnerable-to-new-microsoft-email-hack-security-researchers-say-12388802


:max_bytes(150000):strip_icc()/registration-3938434_1280-e2aa7e5d57264ae19b69027f14c85c2f.jpg)



