Allow domains to ‘drop’ and also you’re rising the effectiveness of a wide range of assaults
Managing domains is a job that enterprises usually depart to the advertising division fairly than the safety crew.
Yet expired – or ‘dropped’ – domains can pose an actual safety threat. Cybercriminals can hijack redundant domains and use them to hold out a spread of assaults in opposition to organizations.
These vary from phishing and enterprise e mail compromise to ransomware and provide chain assaults. Almost any compromise the place an attacker makes use of an ostensibly respectable id to beat defences is made simpler by taking up an expired area.
Why domains are left to run out
Organizations permit domains to run out for various causes. Sometimes it’s a easy mistake: a site renewal is missed as a result of a cost methodology has expired or the renewal contact has moved on.
But domains additionally drop as a result of a model is not getting used, as a result of they had been arrange for take a look at and improvement functions, or as a result of they belong to a enterprise or product that has been acquired by one other firm.
In April 2021, for instance, Google’s Argentina area was acquired by web designer Nicolas Kurona for a mere £2 ($2.90). The area was shortly transferred again to Google, and there’s no suggestion Kurona meant to misuse it – nevertheless it exhibits how simple it’s to lose management of such a key, high-value asset.
RELATED Flaws in Tonga’s top-level domain left Google, Amazon vulnerable to takeover
“Organizations have a number of domains, and also you’d anticipate fairly a little bit of governance and care round the principle area,” Phil Robinson, principal guide and founding father of Prism Infosec, advised The Daily Swig.
Domains for subsidiaries or inside programs are tougher to maintain observe of, nevertheless. “Through acquisitions, in case you’re not cautious you can find yourself with a site that has fallen between the cracks which may then expire,” he warns.
This may then be registered by others, to make use of as they please.
 Domains will be ‘dropped’ due to oversights or as a result of a model has been deserted or acquired
Domains will be ‘dropped’ due to oversights or as a result of a model has been deserted or acquired
What occurs to expired domains?
Domain expiration follows a set course of. Every area has an expiry date on its WHOIS document. Once that date is reached, there’ll normally be a renewal grace interval; this varies from registrar to registrar.
After that there’s a redemption interval, the place the area can nonetheless be reclaimed, after which a five-day ‘pending delete’ interval. Subsequently it’s added to a site drop listing, which criminal hackers are identified to trawl for promising targets, earlier than being made available for purchase on the open market.
How may a malicious hacker exploit an expired area?
Cybercrooks can use dropped domains for any assault vector that exploits a corporation’s id, resembling account takeovers or phishing campaigns that leverage false enterprise invoices.
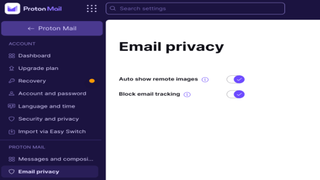
Criminal teams have even arrange mail servers utilizing expired domains. In flip, these can be utilized to realize entry to social media accounts related to the expired area, or extra worryingly, web companies and SaaS functions.
“There are some ways attackers can use previous domains to their benefit,” Tom McVey, answer architect at cloud safety platform Menlo Security, advised The Daily Swig.
Read more of the latest internet infrastructure news
“For instance, a producing organisation may overlook to resume their area ‘manufactory.com’. Attackers may then buy the area and use it to host a web site that’s constructed to look identical to the producer’s website – besides each obtain hyperlink secretly accommodates contaminated recordsdata.
He provides: “They may additionally execute phishing and social engineering assaults by emailing previous shoppers with what seems to be a respectable and protected e mail tackle, [such as] gross [email protected].
“The attackers basically depend on the status of the area to help enhance the efficacy of their assaults.”
 Hijacked domains are used for identity-based assault vectors resembling account takeovers or phishing campaigns
Hijacked domains are used for identity-based assault vectors resembling account takeovers or phishing campaigns
There are different, extra advanced vectors, resembling exploiting web site scripts that decision up the expired area. In one blog post, as an example, Israeli cybersecurity firm Reflectiz breaks down an assault on stolen information website WeLeakInfo, in addition to script-based assaults.
In a separate post, safety knowledgeable Gabor Szathmari seems at how expired domains might be used to assault companies – on this case, legislation corporations in Australia.
Researchers, Szathmari recounted, had proved that by organising a catch-all email server, they might acquire entry to a authorized observe’s Office 365 and GSuite accounts, and from there confidential paperwork. The potential for dangerous actors to abuse dropped domains, the safety guide argued, is intensive.
How to examine whether or not a site is expired or expiring
The finest option to keep away from dropped area assaults is to have a sturdy system for area administration. Security groups ought to work with others within the enterprise, together with builders and advertising groups, to make sure previous domains usually are not left to run out. The price of retaining previous domains registered – and so protected – is small in comparison with the potential harm arising from not doing so.
Firms may contemplate industrial area monitoring, or free companies resembling Expired Domains.
YOU MIGHT ALSO LIKE UK Department for Transport inadvertently served pornographic content to site visitors
Penetration assessments also needs to establish programs linked to expired domains, in order that dependent programs are shut down or reconfigured. And, as Menlo Security’s Tom McVey factors out, ‘zero belief’ and related architectures can scale back the menace by eradicating belief for legacy domains and programs.
“This actually isn’t a brand new downside and it illustrates organizations’ tendency to concentrate on their new shiny programs and overlook about legacy programs or, on this case, domains,” Jeff Goldberg, principal safety architect at 1Password, tells The Daily Swig.
Domains, he provides, are sometimes a part of “shadow IT” that’s registered legitimately by workers utilizing particular person e mail accounts, for development functions and even to stop phishing.
How to resume an expired area title
If your area title has expired, you need to contact the registrar or reseller that supplied your area title registration companies to learn the way to resume the area.
You can confirm your registrar of document through the use of this lookup tool, which is maintained by the Internet Corporation for Assigned Names (ICANN).
Further registrar info will be discovered on the ICANN-Accredited Registrar list.
However, if an expired area has been taken over, you’ll have to pay the brand new house owners to regain management.
Where dropping management of domains is worried, prevention is manifestly higher, and cheaper, than the remedy.
https://portswigger.internet/daily-swig/how-expired-web-domains-help-criminal-hackers-unlock-enterprise-defenses