Cases of ransomware assaults are on the rise.
89 instances of ransomware assaults had been reported to the Cyber Security Agency of Singapore (CSA) in 2020, a 154 per cent enhance from 2019.
Ransomware is a sort of malicious software program that infects a pc and restricts customers’ entry to it till a ransom is paid to unlock it.
The CSA additionally identified a number of observations about native ransomware assaults in its Singapore Cyber Landscape 2020 publication.
Cybercriminals seem to be fishing for bigger victims in the manufacturing, retail and healthcare sectors for greater payouts.
Those who need to utilise ransomware, however are not technologically adept, are ready to get their fingers on subtle ransomware, which is more and more being provided as a service. This makes it simpler for extra criminals to get their fingers on malware.
The common price to a enterprise in ransomware funds is US$220,000 (S$295,896) in accordance to Coveware. So what can companies do to protect themselves towards ransomware? Local cybersecurity consulting agency INTfinity Consulting has some sensible ideas and actual life examples to provide.
Tip 1: Use robust passwords and multi-issue authentication
This very simple step can’t be overemphasised.
What does a robust password seem like? It’s positively not <password123>
Key features of a robust password embrace size (longer passwords have a tendency to be more durable to hack), a mixture of higher and decrease case letters, numbers and symbols, and unpredictability (which means no private info like your identify or start date, and no dictionary phrases).
A robust password may seem like <[email protected]!%HHufR>. Using a password supervisor may even make it simpler to preserve safe and distinctive passwords for various web sites and platforms.
These make your password more durable to guess with a brute-power assault. In addition, ought to your password in some way be disclosed, having multi-issue authentication may forestall an attacker from totally compromising your account.
Company A, a medium-sized enterprise which operates a community that’s used as a management centre to handle distributed providers island-broad, was attacked due to a weak password.
The firm had a misconfiguration which uncovered certainly one of its servers to the web and allowed anybody to entry it remotely.
Unfortunately, the password that guarded entry to the server was too straightforward to guess and shortly an attacker managed to enter Company A’s server, and from there, entry extra programs throughout the community, permitting the attacker to get info like which account had administrative entry.
The system did throw up a number of warning indicators, like malware alerts, however nobody heeded them.
Eventually the attacker managed to acquire management of the executive account throughout the community that gave them full management over all programs.
Using these credentials, the attacker accessed the file and e-mail server, the place they proceeded to disable scheduled backups, erase earlier backups, and deployed a ransomware encryption software program that crippled practically all their programs. As a results of this, Company A had an operational downtime of greater than a month.
Tip 2: Get knowledgeable to evaluate your web site/community/database periodically
Just like how you’ll go for normal medical examine ups for your well being, it’s a good apply to carry out a safety evaluate on your web site, community, or database recurrently to spot weak areas that may be exploited.
Many Singapore-based cybersecurity companies, comparable to INTfinity Consulting, can do an evaluation every time you implement a web site change or on a periodic foundation.
These assessments can vary from primary necessities like hole evaluation and vulnerability evaluation to extra complete providers like threat hunting and digital forensics incident response.
Company B, which runs a bustling e-commerce enterprise, is totally reliant on its web site to market its merchandise. And so it continuously upgrades the look of its web site to appeal to extra clients.
Unfortunately, certainly one of its upgrades included a coding flaw which was exploited by an attacker. The attacker then went on to uncover extra passwords inside the online server and at last gained entry to Company B’s purchasers’ private info, which might be bought on the black market.
The attacker took out the info slowly over a time period in order not to set off any detection mechanism. Finally, the attacker unleashed a ransomware which encrypted the info on Company B’s server.
Company B was pressured to take its web site offline and will solely get better its e-commerce enterprise a number of weeks later.
Tip 3: Update your peripheral units like firewalls, printers, and VPN
An growing variety of organisations are deploying firewalls and VPNs (digital personal networks) as extra of their workers begin working from house.
However, the patches and safety updates for these units are typically missed, generally for years, and this makes them prime targets for cyberattacks.
While most endpoint working programs do a superb job of enabling and pushing updates, customers sometimes overlook peripheral units comparable to printers (yes, printers can be hacked!), VPNs, and firewalls.
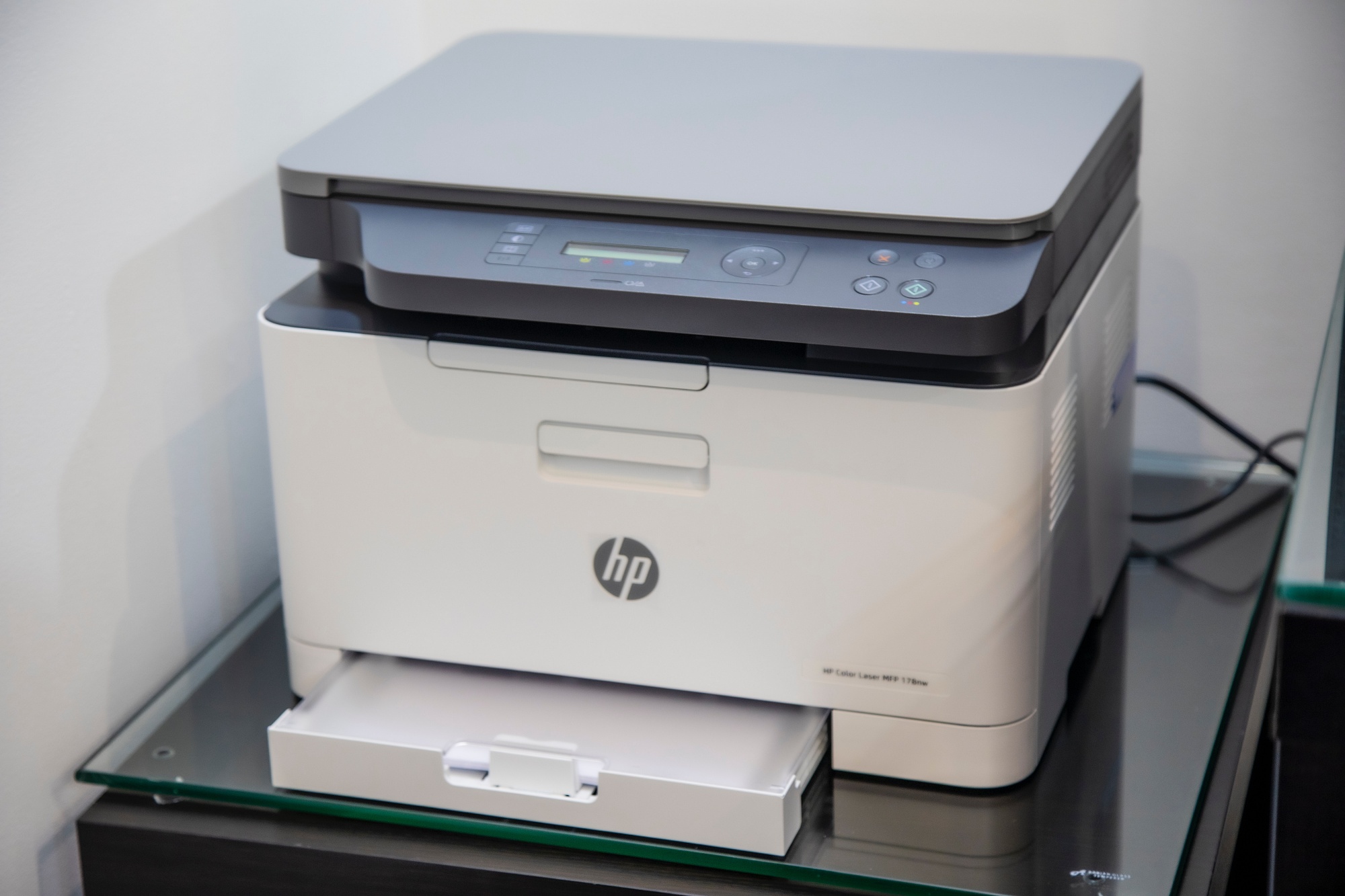 You see a printer, hackers see a backdoor. Photo by Mahrous Houses on Unsplash
You see a printer, hackers see a backdoor. Photo by Mahrous Houses on Unsplash
These units reside in the identical community as your customers and must be up to date as continuously as your working system.
According to INTfinity Consulting, as of July 2021, there are round 100 Singapore IP addresses that also exhibit a selected vulnerability which may have been patched greater than two years in the past.
Using an unpatched firewall makes your community extra susceptible as a result of cyber threats are always evolving.
Once a cybercriminal bypasses your firewall and enters your community, they sometimes wait till they discover a possibility to entry accounts with increased privileges, comparable to an administrator account. This will then grant them the flexibility to deploy their ransomware.
INTfinity Consulting additionally revealed that there’s an growing development of ransomware operators misappropriating a software program known as Cobalt Strike.
While Cobalt Strike is marketed as a reputable business software program which emulates cybersecurity threats for testers to establish vulnerabilities, it has been adapted by cybercriminals to assault, extract information, and unleash malware on their victims. It is favoured by them as a result of it leaves fewer traces of digital proof behind, making it tough for incident responders to monitor and deploy fixes.
Tip 4: Backup your information
INTfinity Consulting has this recommendation for backing up your information: Follow the three-2-1 backup rule, which shall be very useful when it comes to catastrophe restoration.
Have three copies of your information (one copy is manufacturing information whereas the opposite two are backup copies).
Store your information on two completely different media, and guarantee that no less than one copy is positioned offline and even higher, off-web site.
Back up typically and at all times guarantee that backups could be restored.
Tip 5: Be vigilant towards phishing emails
Lastly, ransomware is often delivered by way of phishing emails the place customers are lured into clicking a malicious obtain hyperlink or opening a seemingly innocuous e-mail attachment.
Staff must be taught to establish suspicious emails, particularly people who originate from outdoors the organisation.
For this objective, INTfinity Consulting suggests filtering emails that originate from exterior senders and including “[External]” to the topic. This is to immediate workers to be extra vigilant after they open the e-mail.
For extra info on INTfinity Consulting and the providers it gives, you possibly can head over to its website here.
Thanks to this text that was sponsored by INTfinity Consulting, this author went to change all his passwords. Top pictures by way of Agefis on Unsplash, malwarebytes.com






