(MENAFN – Asia Times) President Joe Biden’s July 27 warning a couple of“shooting battle” arising from cyberattacks underscores the fraught state of US-Chinese strategic relations.
“I believe it is extra probably we’ll find yourself – properly, if we find yourself in a battle, an actual shooting battle with a significant energy, it may be as a consequence of a cyber breach of nice consequence,” Biden mentioned throughout a speech on the Office of the Director of National Intelligence.“And it is growing exponentially – the capabilities.”
Significantly, the remarks have been made obtainable in a textual content circulated by the White House press workplace, not a spontaneous outburst by the president.
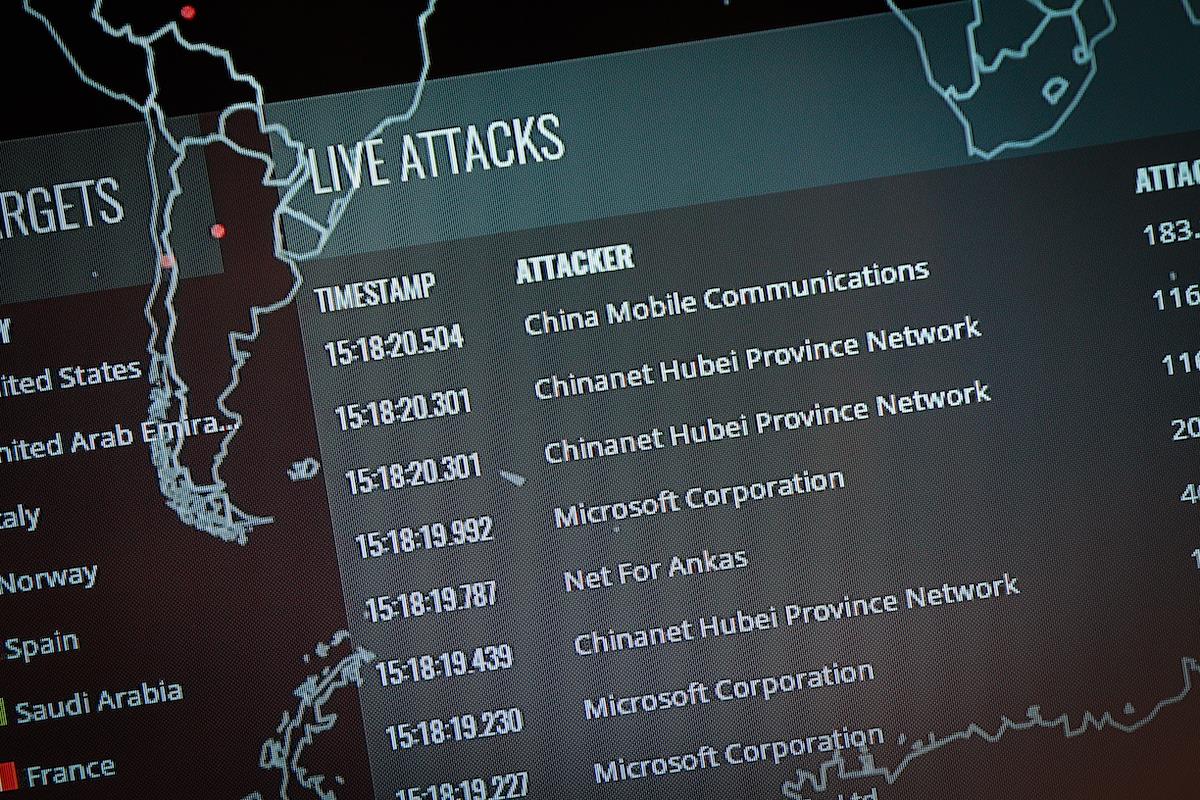
The United States and its allies final week denounced China for complicity in assaults on the Microsoft Exchange e mail server, and China responded by accusing the Central Intelligence Agency (CIA) of hacking Chinese techniques.
A Foreign Ministry spokesman cited a 2020 report by the Chinese cybersecurity agency 360 Core Security claiming {that a} CIA hacking group referred to as APT-C-39 carried out industrial espionage in opposition to Chinese corporations.
US President Joe Biden addresses the Intelligence Community workforce and its management whereas on a tour on the Office of the Director of National Intelligence in McLean, Virginia, on July 27, 2021. Photo: AFP / Saul Loeb
If the intelligence world is a wilderness of mirrors, as James Angleton mentioned, cyber warfare is a wilderness of nanometers. Unless an insider leaks info to the skin world, it’s inconceivable to know what intelligence providers are doing and any info supplied to the media is sort of definitely false.
But each Washington, by warning Beijing that cyberattacks may provoke a shooting battle, and Beijing, by taking emergency measures to make sure the safety of its personal networks, are signaling an excessive stage of concern.
This doesn’t seem like a drill.
China’s crackdown on ride-hailing app Didi simply after its New York preliminary public providing earlier this month was extensively interpreted as a smack-down of Chinese entrepreneurs by the Communist Party.
Getting powerful on these Internet unicorns was seen as arising out of the Communist Party’s rancor on the look of inequality from personal tutoring corporations, and the pay of ride-hailing and meals supply drivers.
Security, nevertheless, was clearly framed as the problem earlier this week when Tencent’s ubiquitous WeChat app, which does all the things from on-line funds to social media, suspended new registrations till August.
“We are at the moment upgrading our safety expertise to align with all related legal guidelines and rules,” Tencent instructed the Reuters information service.“During this time, registration of recent Weixin private and official accounts has been briefly suspended. Registration providers will likely be restored after the improve is full, which is anticipated in early August.”

WeChat brand. Photo illustration: AFP / Jakub Porzycki / NurPhoto
WeChat has 1.24 billion customers. The affect on China is greater than a suspension of Facebook, Instagram and Apple Pay downloads can be within the United States. Downloads of different in style Chinese apps have been suspended as properly, together with the Toutiao information app supplied by ByteDance, the guardian of TikTok. Again, safety seems to be the foremost situation.
China is deeply anxious about its system vulnerabilities, as Wu Yunkun, the president of Q’anxin Technology Group, instructed the“Observer” web site (a information and opinion outlet near the State Council) in a July 13 interview . (The textual content will be learn with in style Internet translation packages).
Wu is very anxious in regards to the utility of synthetic intelligence to hacking: If an intruder extracts sufficient private details about a goal, AI can create a bot that credibly imitates the cyber presence of the goal.
China’s web corporations working abroad, Wu added, could symbolize a vulnerability of protected knowledge:
Exercises on cyber warfare and safety are seen happening throughout the NATO CWIX interoperability train on June 22, 2017, in Bydgoszcz, Poland. Photo: AFP / Jaap Arriens / NurPhoto
In March 2017, Wikileaks revealed what it claimed have been 8,761 paperwork and information from the CIA’s Center for Cyber Intelligence. Wikileaks wrote:
By the tip of 2016, the CIA’s hacking division, which formally falls below the company’s Center for Cyber Intelligence (CCI), had over 5000 registered customers and had produced greater than a thousand hacking techniques, trojans, viruses and different ‘weaponized’ malware [programs].
Such is the dimensions of the CIA’s enterprise that by 2016, its hackers had utilized extra code than that used to run Facebook. The CIA had created, in impact, its ‘personal NSA’ with even much less accountability and with out publicly answering the query as as to if such a large budgetary spend on duplicating the capacities of a rival company might be justified.
There is not any approach to confirm the alleged CIA paperwork revealed by Wikileaks. Nor is there any approach to confirm a May 6, 2019, New York Times story claiming that Chinese spies“captured” hacking instruments from the US National Security Agency after which used them to hack American installations.
Two issues we will conclude with a sure diploma of confidence are that:
- If the president of the United States warns of a“shooting battle” on account of cyberwar, he’s anxious about one thing; and
- If China halts new downloads of its hottest smartphone apps, it’s anxious about safety as properly.
It’s a good presumption that each side do their finest to probe the defenses of the opposite.
What we have no idea is what kind of injury cyberattacks may trigger and the way shut they could carry the United States and China to the brink of battle.
During the Cold War, Russian and American planes skirted one another’s air area to check responses; warships shadowed one another; and armies drilled for all-out nuclear battle.

Exercises on cyber warfare and safety are seen happening throughout the NATO CWIX interoperability train n 22 June, 2017 in Bydgoszcz, Poland. Photo: AFP / Jaap Arriens / NurPhoto)
These have been essential however extremely dangerous workout routines. When the workout routines grew to become too practical, throughout the 1983 Able Archer operation by NATO, the Russians thought that the West actually was getting ready for a preemptive strike and really practically launched considered one of their very own. For this, I check with Nate Jones’s glorious e-book on the topic.
Evidently, the stakes within the present cyber skirmishes between the United States and China transcend the occasional act of business espionage or disruption of an e mail server. It’s conceivable that cyberattacks might shut down monetary techniques, or disrupt main utilities, or interrupt mass transit, or interdict digital communications.
This is the stuff of situation novels fairly than information reporting. One can solely hope that the general public expressions of fear coming from the American and Chinese governments don’t portend a battle in our on-line world that we’re ill-equipped to grasp, not to mention management.
Studying Operation Able Archer is an effective place to start out.
MENAFN29072021000159011032ID1102533868
Legal Disclaimer: MENAFN offers the knowledge “as is” with out guarantee of any variety. We don’t settle for any duty or legal responsibility for the accuracy, content material, photos, movies, licenses, completeness, legality, or reliability of the knowledge contained on this article. If you will have any complaints or copyright points associated to this text, kindly contact the supplier above.

:max_bytes(150000):strip_icc()/registration-3938434_1280-e2aa7e5d57264ae19b69027f14c85c2f.jpg)




