US and allies, together with the European Union, the United Kingdom, and NATO, are officially blaming China for this yr’s widespread Microsoft Exchange hacking marketing campaign.
These early 2021 cyberattacks focused over 1 / 4 of one million Microsoft Exchange servers, belonging to tens of hundreds of organizations worldwide.
The Biden administration attributes “with a excessive diploma of confidence that malicious cyber actors affiliated with PRC’s MSS carried out cyber espionage operations using the zero-day vulnerabilities in Microsoft Exchange Server disclosed in early March 2021.”
“The assault on Microsoft Exchange software program was extremely more likely to allow large-scale espionage, together with buying personally identifiable info and mental property,” the UK National Cyber Security Centre (NCSC) additionally said at this time.
“The National Cyber Security Centre – which is a component of GCHQ – assessed that it was extremely possible {that a} group referred to as HAFNIUM, which is related to the Chinese state, was chargeable for the exercise.”
The UK added that the Chinese Ministry of State Security (MSS) can be behind Chinese state-backed hacking teams tracked as APT40 and APT31.
Today, the UK has revealed that Chinese state-backed actors had been chargeable for having access to laptop networks around the globe by way of Microsoft Exchange servers https://t.co/ot05RPxUOq
(1/3) pic.twitter.com/LiXvD4VlTT
— NCSC UK (@NCSC) July 19, 2021
The NSA, CISA, and FBI additionally issued a joint advisory containing greater than 50 techniques, methods, and procedures (TTPs) that Chinese state-sponsored cyber actors have utilized in attacks focusing on the US and allied networks.
CISA and the FBI additionally revealed indicators of compromise and TTPs to assist organizations detect and remediate APT40 intrusions and established footholds inside their networks.
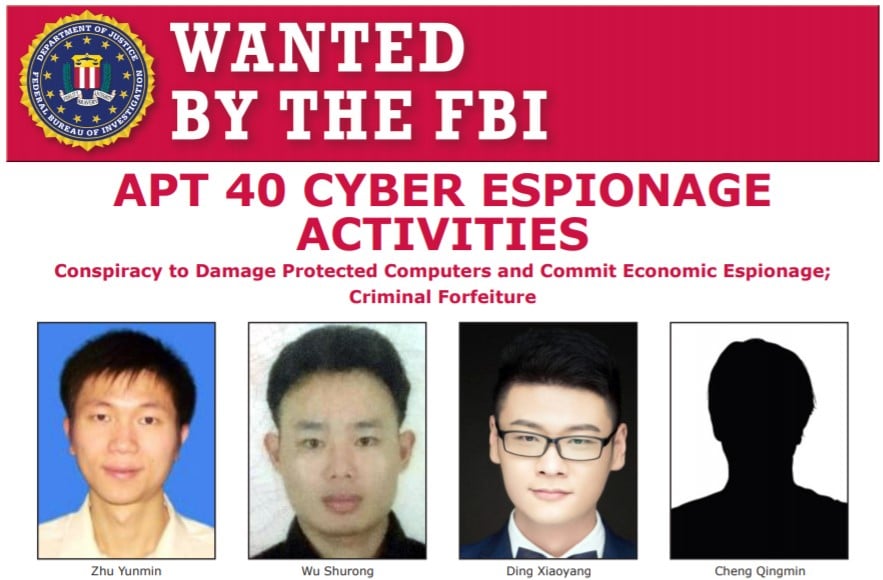
The US Department of Justice additionally announced criminal charges in opposition to 4 MSS hackers (indictment here) concerning actions half of a multi-year marketing campaign focusing on governments around the globe and organizations from crucial sectors.
“The assault on Microsoft Exchange servers is one other severe instance of a malicious act by Chinese state-backed actors in our on-line world,” the EU and its Member States added in a separate assertion issued at this time.
“This type of conduct is totally unacceptable, and alongside our companions we is not going to hesitate to name it out once we see it.”
Abused to deploy ransomware and cryptominers
In early March 2021, Microsoft disclosed 4 zero-days actively being exploited in attacks targeting on-premises Microsoft Exchange servers.
The vulnerabilities (collectively referred to as ProxyLogon) had been exploited in indiscriminate attacks in opposition to organizations from a number of business sectors worldwide, with the tip objective of stealing delicate info.
Threat actors behind ProxyLogon attacker have been noticed whereas deploying web shells, cryptomining malware, in addition to DearCry and Black Kingdom ransomware payloads on compromised Exchange servers.
After Microsoft disclosed the attacks, Slovak web safety agency ESET found at least ten APT groups focusing on weak Exchange servers.
Microsoft stated on the time that the Chinese state-sponsored hacking group referred to as Hafnium is behind these attacks.
“Historically, Hafnium primarily targets entities within the United States for the aim of exfiltrating info from a quantity of business sectors, together with infectious illness researchers, regulation corporations, greater schooling establishments, protection contractors, coverage assume tanks and NGOs,” Microsoft said.
“While Hafnium is predicated in China, it conducts its operations primarily from leased digital non-public servers (VPS) within the United States.”






