A brand new cryptocurrency stealer variant is being unfold through a worldwide spam marketing campaign and probably through Discord channels.
Dubbed Panda Stealer, Trend Micro researchers said this week that the malware has been discovered concentrating on people throughout international locations together with the US, Australia, Japan, and Germany.
The malware begins its an infection chain through phishing emails and samples uploaded to VirusTotal additionally point out that victims have been downloading executables from malicious web sites by way of Discord hyperlinks.
Panda Stealer’s phishing emails faux to be enterprise quote requests. So far, two strategies have been linked to the marketing campaign: the primary of which makes use of connected .XLSM paperwork that require victims to allow malicious macros.
If macros are permitted, a loader then downloads and executes the principle stealer.
In the second chain, an connected .XLS file incorporates an Excel method that hides a PowerShell command. This command makes an attempt to entry a paste.ee URL to pull a PowerShell script to the sufferer’s system and to then seize a fileless payload.
“The CallByName export operate in Visual Basic is used to name the load of a .NET meeting inside reminiscence from a paste.ee URL,” Trend Micro says. “The loaded meeting, obfuscated with an Agile.NET obfuscator, hollows a official MSBuild.exe course of and replaces it with its payload: the hex-encoded Panda Stealer binary from one other paste.ee URL.”
Once downloaded, Panda Stealer will try to detect keys and addresses related to cryptocurrency wallets holding funds together with Ethereum (ETH), Litecoin (LTC), Bytecoin (BCN), and Dash (DASH). In addition, the malware is ready to take screenshots, exfiltrate system knowledge, and steal data together with browser cookies and credentials for NordVPN, Telegram, Discord, and Steam accounts.
While the marketing campaign has not been attributed to particular cyberattackers, Trend Micro says that an examination of the malware’s energetic command-and-control (C2) servers led the workforce to IP addresses and a digital personal server (VPS) rented from Shock Hosting. The server has since been suspended.
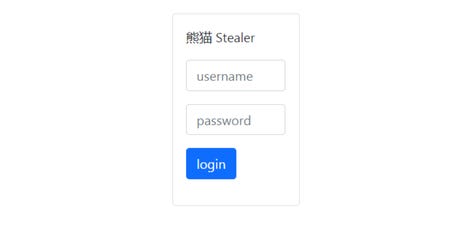
Panda Stealer is a variant of Collector Stealer, malware that has been offered in the previous on underground boards and through Telegram channels. The stealer has since appeared to have been cracked by Russian risk actors going underneath the alias NCP/su1c1de.
The cracked malware pressure is comparable however makes use of completely different infrastructure parts resembling C2 URLs and folders.
“Because the cracked Collector Stealer builder is overtly accessible on-line, cybercriminal teams and script kiddies alike can use it to create their very own custom-made model of the stealer and C2 panel,” the researchers be aware. “Threat actors can also increase their malware campaigns with particular options from Collector Stealer.”
Trend Micro says there are similarities in the assault chain and fileless distribution methodology to Phobos ransomware. Specifically, as described by Morphisec, the “Fair” variant of Phobos is comparable in its distribution strategy and is being always up to date to scale back its footprint, resembling decreasing encryption necessities, in order to keep underneath the radar for so long as attainable.
The researchers additionally famous correlations between Phobos and LockBit in an April 2021 report.
Previous and associated protection
Have a tip? Get in contact securely by way of WhatsApp | Signal at +447713 025 499, or over at Keybase: charlie0





