For ten days in March, thousands and thousands had been caught in the identical massive spam marketing campaign.
Each e mail appeared prefer it got here from somebody the recipient knew: the spammer took stolen e mail addresses and passwords, quietly logged into their e mail account, scraped their lately despatched emails and pushed out customized emails to the recipient of that despatched e mail with a hyperlink to a faux web site pushing a weight reduction tablet or a bitcoin rip-off.
The emails had been so convincing greater than 100,000 folks clicked by means of.
We know this as a result of a safety researcher found the server leaking your entire operation. The spammer had forgotten to set a password.
Security researcher Bob Diachenko found the leaking data and with assist from TechCrunch analyzed the server. At the time of the invention, the spammer’s rig was now not operating. It had completed its job, and the spammer had possible moved onto one other server — possible in an effort to keep away from getting blacklisted by anti-spam suppliers. But the server was primed to start out spamming once more.
Given there have been greater than three million distinctive uncovered credentials sitting on this spammer’s server — hosted on intelimost.com, we wished to safe the information as quickly as potential. With no contact info for the spammer — shock, shock — we requested the internet hosting supplier, Awknet, to tug the server offline. Within a few hours of constructing contact, the supplier nullrouted the server, forcing all its community site visitors into a sinkhole.
TechCrunch offered a copy of the database to Troy Hunt. Anyone can now verify breach notification web site Have I Been Pwned to see if their e mail was misused.
But the dormant server — whereas it was nonetheless energetic — provided a uncommon alternative to grasp how a spam operation works.
The one factor we didn’t have was the spam e mail itself. We reached out to dozens of individuals to ask concerning the e mail they acquired. Two replied — however just one nonetheless had a copy of the e-mail.
The e mail despatched by the spammer. (Image: provided)
“The identical mail appeared on three events,” mentioned one of many recipients in an e mail to TechCrunch. “The topic was associated to an e mail I had despatched beforehand to that particular person so the attacker had clearly bought entry to his mailbox or the mail server,” the sufferer mentioned.
The e mail, when clicked, would direct the recipient by means of a number of web sites in fast succession to find out the place they had been situated, based mostly off their IP handle. If the recipient was within the U.S., they’d be pushed to a faux CNN web site selling a bogus well being treatment. In this case, the spammer was concentrating on U.Okay. residents — and most had been directed to a faux BBC web page selling a bitcoin rip-off.

One of the faux web page.s (Screenshot: TechCrunch)
The spammer had different servers that we had no visibility into, however the uncovered server revealed most of the cogs and equipment to the operation. The server, operating an Elasticsearch database, was well-documented sufficient that we found one of many three spam emails despatched to our recipient.
This entry alone tells us a lot about how the spam operation labored.

A database document of 1 e mail despatched by the spammer. (Screenshot: TechCrunch)
Here’s the way it works. The spammer logs into a sufferer’s @btinternet.com e mail account utilizing their stolen e mail handle and password. The scammer pulls a lately despatched e mail from their sufferer’s e mail server, which feeds into one other server — like inbox87.host and viewmsgcs.stay — tasked with producing the customized spam e mail. That e mail incorporates the topic line of the despatched e mail and the goal recipient’s e mail handle to make it appear to be it’s being despatched from the true particular person.
Once the message is able to ship, it’s pushed by means of a proxy connection, designed to masks the place the e-mail has come from. The proxy server is made up of a number of cell telephones, every connecting to the web over their mobile connection.
Each spam message is routed by means of one of many telephones, which often rotates its IP handle to stop detection or being flagged as a spammer.
Here’s what that proxy server seems like.
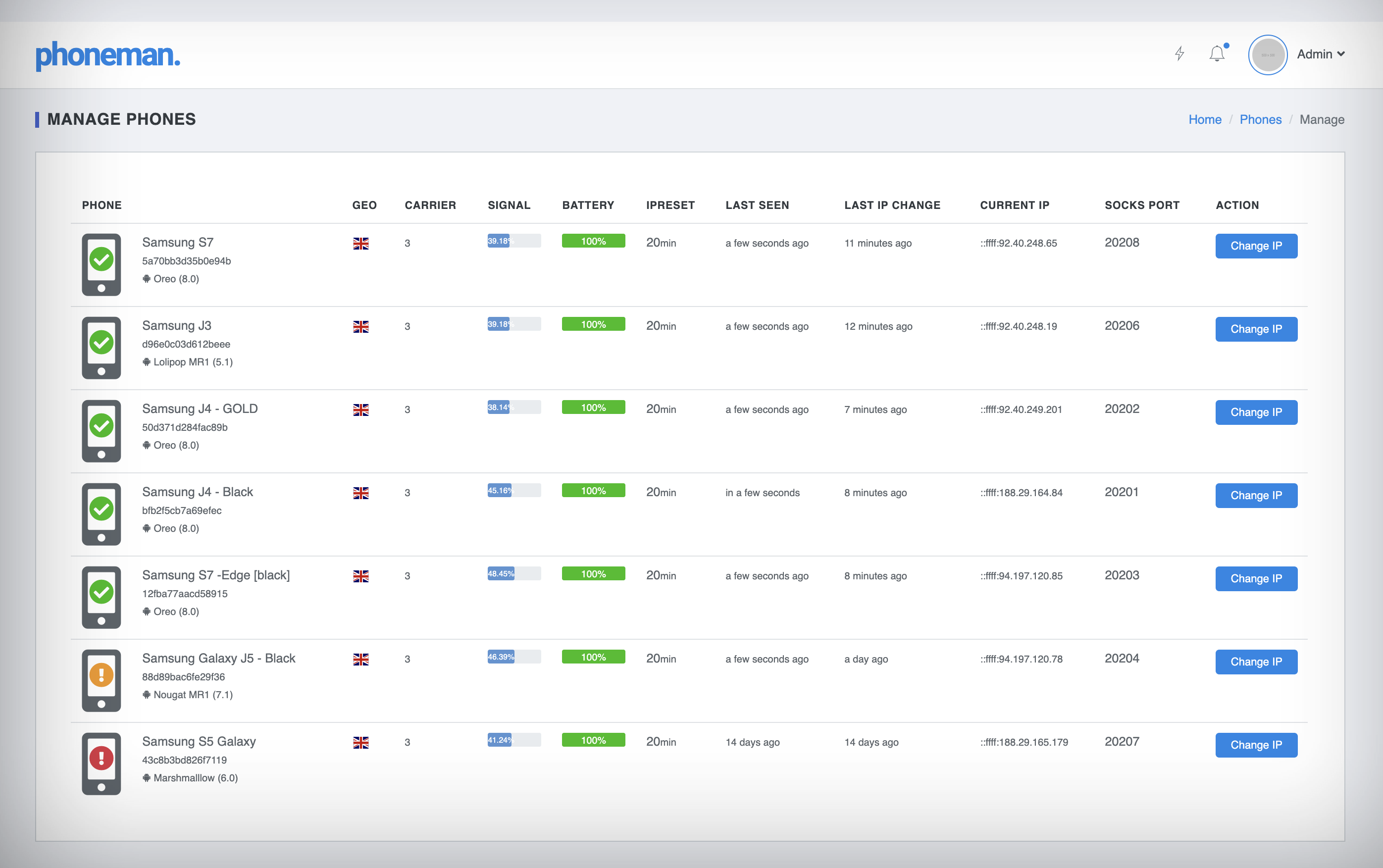
The proxy server comprised of a number of cell telephones with rotating IP addresses. (Screenshot: TechCrunch)
Once the spam message leaves the proxy server, the spam message is pushed by means of the sufferer’s personal e mail supplier utilizing their e mail handle and password, making it appear to be a real e mail to each the e-mail supplier and the recipient.
Now think about that a whole bunch of occasions a second.
Not solely was the spammer’s Elasticsearch database leaking, its Kibana consumer interface was additionally uncovered. That gave the spammer a detailed at-a-glance have a look at the operation in motion. It was so granular that you might see which spam-sending domains had been probably the most environment friendly in tricking a recipient into clicking the hyperlink within the spam e mail.
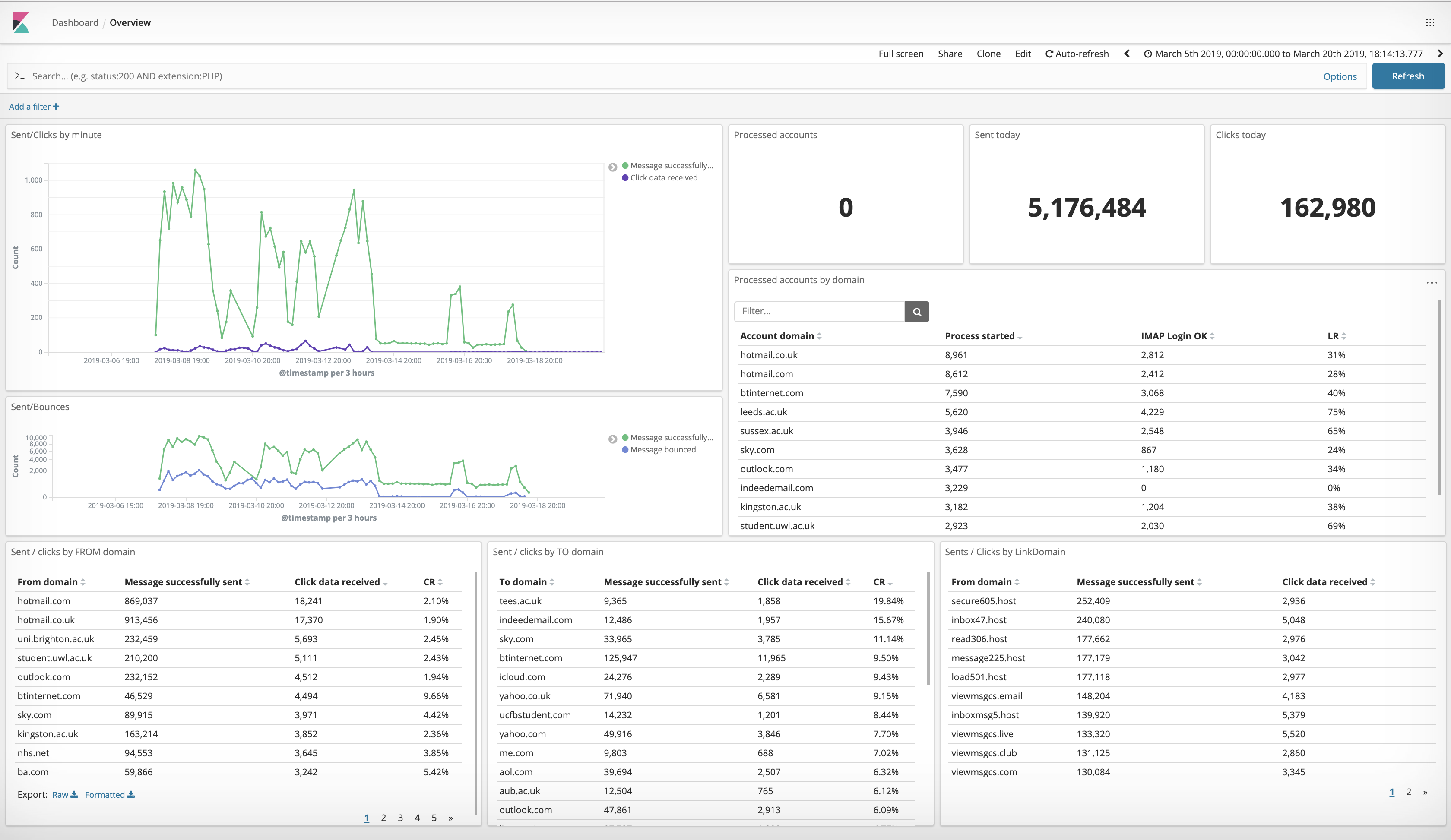
The spammer’s Kibana dashboard, displaying the operation at a look. (Screenshot: TechCrunch)
Each spam e mail contains a tracker within the hyperlink that fed info again to the spammer. In bulk, that permits the spammer to determine which e mail area — like outlook.com or yahoo.com customers — is extra prone to click on on a spam e mail. That can even point out how an e mail supplier’s spam filter acts. The larger variety of clicks, the extra probability of its spam going by means of — permitting the spammer to focus on particular e mail domains sooner or later.
The dashboard additionally contained different info associated to the spam marketing campaign, corresponding to what number of emails had been efficiently despatched and what number of bounced. That helps the spammer residence in on probably the most precious logins sooner or later, permitting them to ship extra spam for decrease bandwidth and server prices.
In all, some 5.1 million emails had been despatched through the 10-day marketing campaign — between March 8 and March 18, with some 162,980 folks clicking on the spam e mail, in accordance with the information on the dashboard.
It’s not the primary time we’ve seen a spam operation in action, nevertheless it’s uncommon to see how profitable it’s.
“This case jogs my memory on a number of different events I reported at some factors up to now — when malicious actors create a subtle system of proxying and logging, leaving a lot tracks to establish their patterns for authorities within the investigations to return,” Diachenko instructed TechCrunch. “This reveals us — once more! — how vital a correct cyber hygiene needs to be.”
What’s clear is that the spammer is aware of the right way to cowl their tracks.
The language settings within the Kibana occasion steered the spammer could also be based mostly in Belgium. We found a number of different related spamming domains using data collected by RiskIQ, a cyberthreat intelligence agency, which scours the net for info. Of the domains we found, all had been registered with faux names and addresses.
As for the server itself, the supplier mentioned it was presumably hacked.
“This was a resold field and the shopper already responded to the abuse ahead saying it was imagined to have been terminated way back,” mentioned Awknet’s Justin Robertson in an e mail to TechCrunch.
And we nonetheless can’t determine the place the e-mail addresses and passwords got here from used to ship the spam. Only 45 percent of emails had been already in Have I Been Pwned, ruling out the chance that the entire passwords had been stolen from credential stuffing.
Since the internet hosting supplier pulled the spammer’s server offline, a number of of their faux websites and domains related to the spam marketing campaign now not load.
But given the unfold of domains and servers propping up the marketing campaign, we suspect the sunken server is just a single casualty in an in any other case ongoing spam marketing campaign.
Got a tip? You can ship suggestions securely over Signal and WhatsApp to +1 646-755–8849. You can even ship PGP e mail with the fingerprint: 4D0E 92F2 E36A EC51 DAAE 5D97 CB8C 15FA EB6C EEA5.






