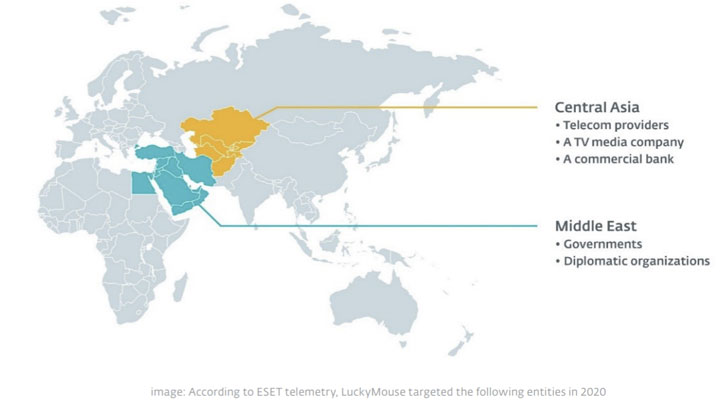
An adversary recognized for its watering hole attacks towards authorities entities has been linked to a slew of newly detected intrusions focusing on varied organizations in Central Asia and the Middle East.
The malicious exercise, collectively named “EmissarySoldier,” has been attributed to a risk actor referred to as LuckyMouse, and is alleged to have occurred in 2020 with the purpose of acquiring geopolitical insights in the area. The assaults concerned deploying a toolkit dubbed SysUpdate (aka Soldier) in quite a few breached organizations, together with authorities and diplomatic companies, telecom suppliers, a TV media firm, and a industrial financial institution.
LuckyMouse, additionally known as APT27 and Emissary Panda, is a classy cyberespionage group that has a historical past of breaching a number of authorities networks in Central Asia and the Middle East. The actor has additionally been linked to cyberattacks aimed toward transnational organizations such because the International Civil Aviation Organization (ICAO) in 2019 and not too long ago attracted consideration for exploiting ProxyLogon flaws to compromise the e-mail server of a governmental entity in the Middle East.
EmissarySoldier is simply the newest in a sequence of surveillance efforts aimed on the targets.
“In order to compromise victims, LuckyMouse sometimes makes use of watering holes, compromising web sites more likely to be visited by its meant targets, ESET malware researcher Matthieu Faou stated in a report revealed at present. “LuckyMouse operators additionally carry out community scans to seek out weak internet-facing servers run by their meant victims.”
What’s extra, ESET additionally discovered a number of contaminated internet-facing programs operating Microsoft SharePoint, which the researchers suspect occurred by making the most of distant code execution vulnerabilities in the appliance.
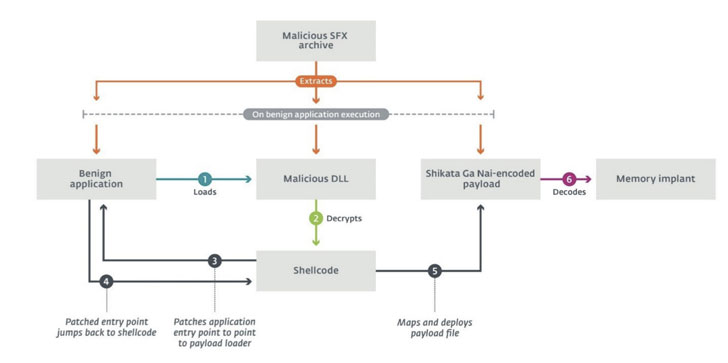
Regardless of the strategy used to realize an preliminary foothold, the assault chain culminates in the deployment of customized post-compromise implants, SysUpdate or HyperBro, each of which leverage DLL search order hijacking to load malicious payloads and thwart detection. “The trident mannequin includes a legit software weak to DLL hijacking, a customized DLL that hundreds the payload, and a uncooked Shikata Ga Nai-encoded binary payload,” Faou famous.
For its half, SysUpdate capabilities as a modular software, with every element dedicated to a specific operational function. It entails abusing a benign software as a loader for a malicious DLL, which in flip hundreds the first-stage payload that in the end decodes and deploys the reminiscence implant on the compromised system. Since its discovery in 2018, the toolkit has undergone quite a few revisions dedicated to including new functionalities, indicating that the operators are actively working to revamp their malware arsenal.
“LuckyMouse was more and more lively all through 2020, seemingly going by a retooling course of in which varied options had been being incrementally built-in into the SysUpdate toolkit,” Faou stated. “This could also be an indicator that the risk actors behind LuckyMouse are regularly shifting from utilizing HyperBro to SysUpdate.”






:max_bytes(150000):strip_icc()/HowtoSpecifyaPreferredSMTPServerforaMacOSXMailAccount2016-01-04-568a7f403df78ccc153b7b78.png)
